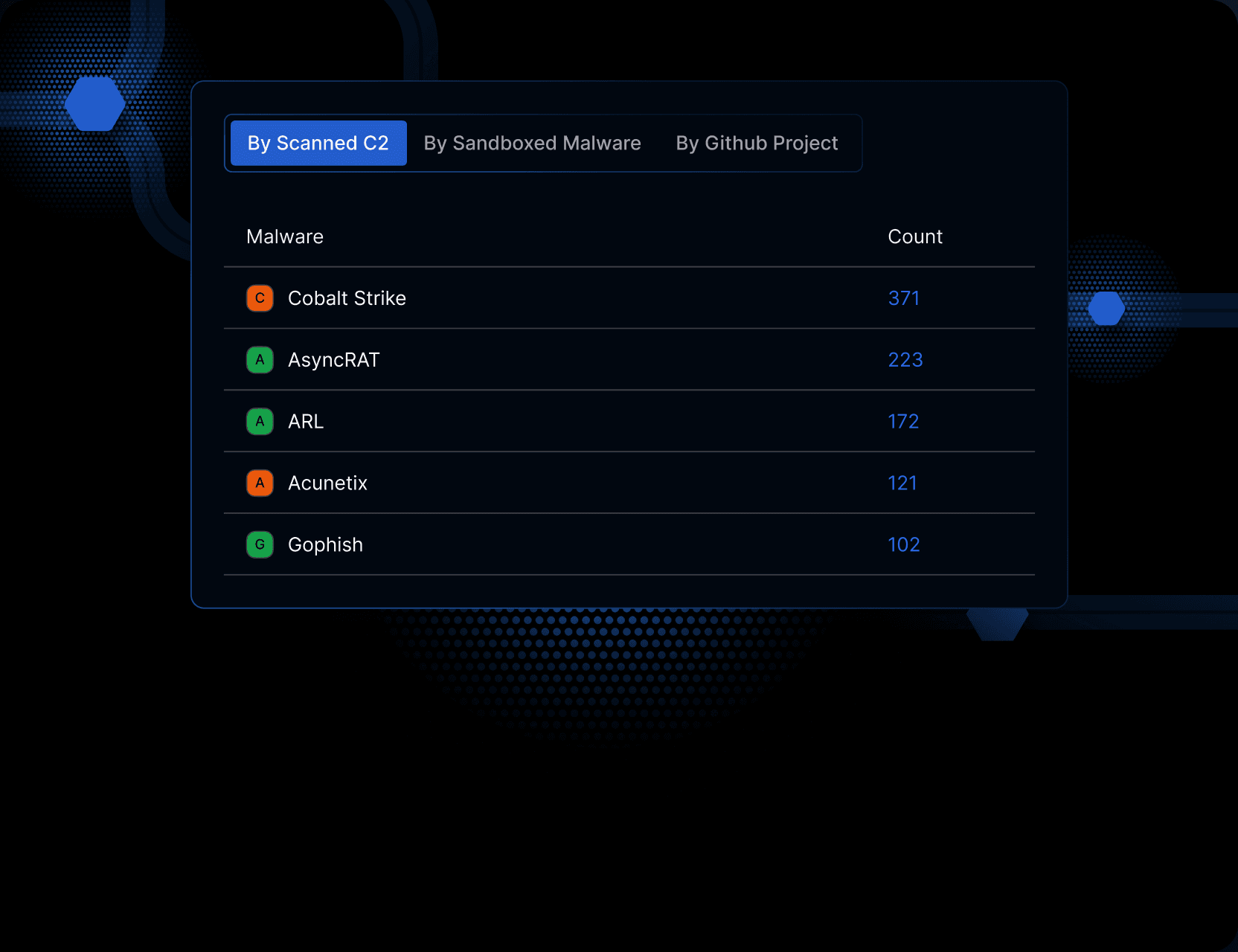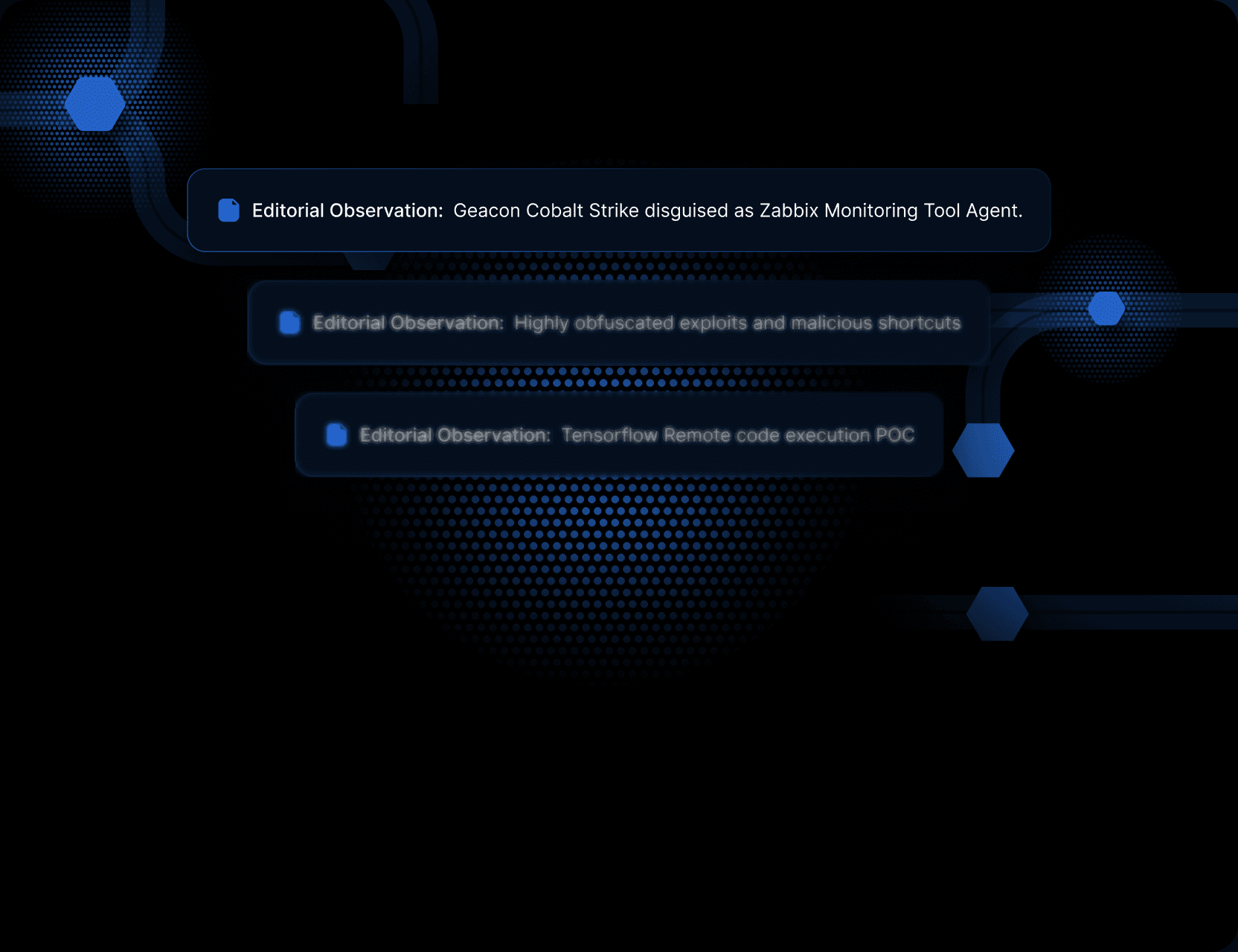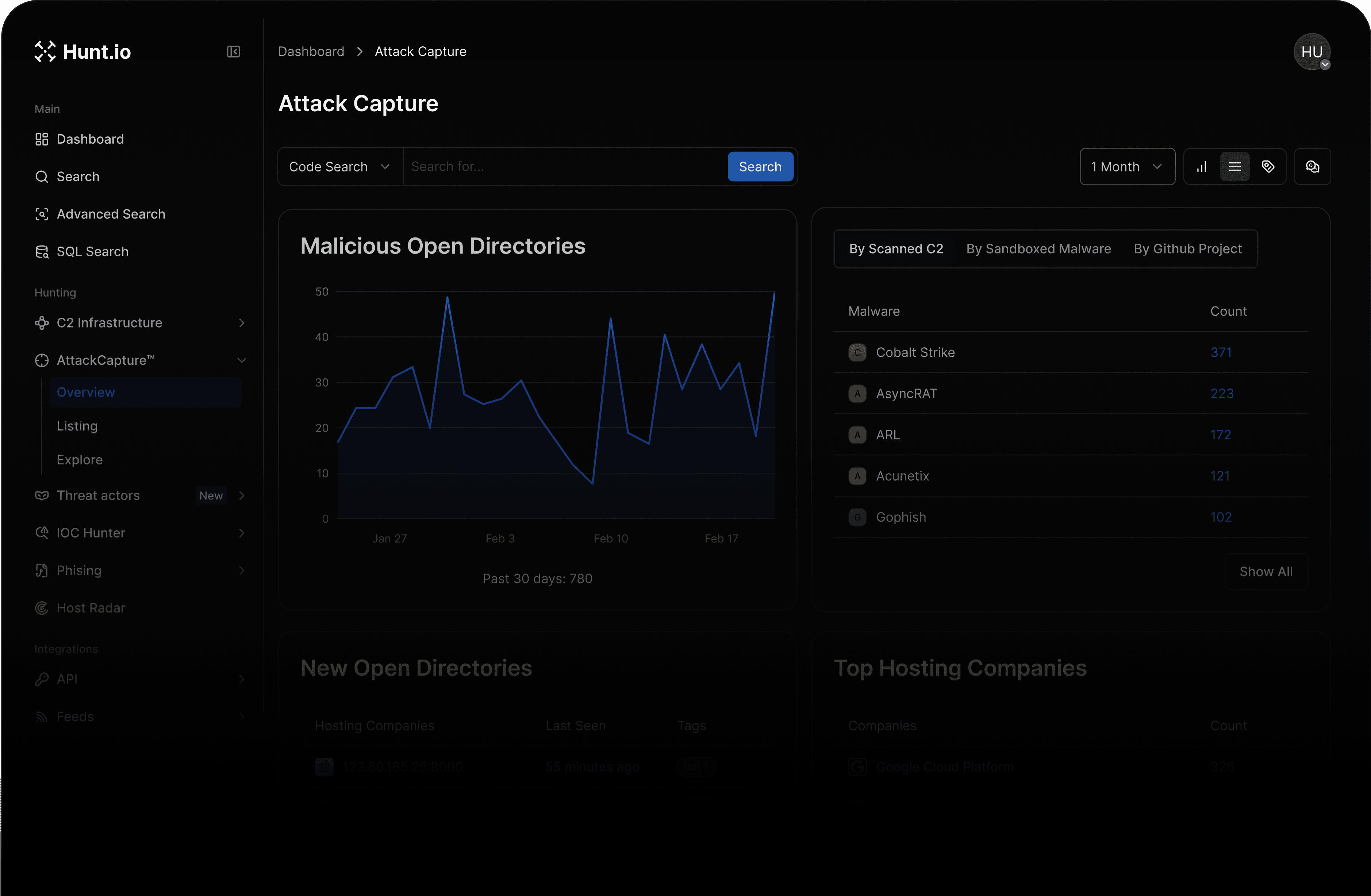
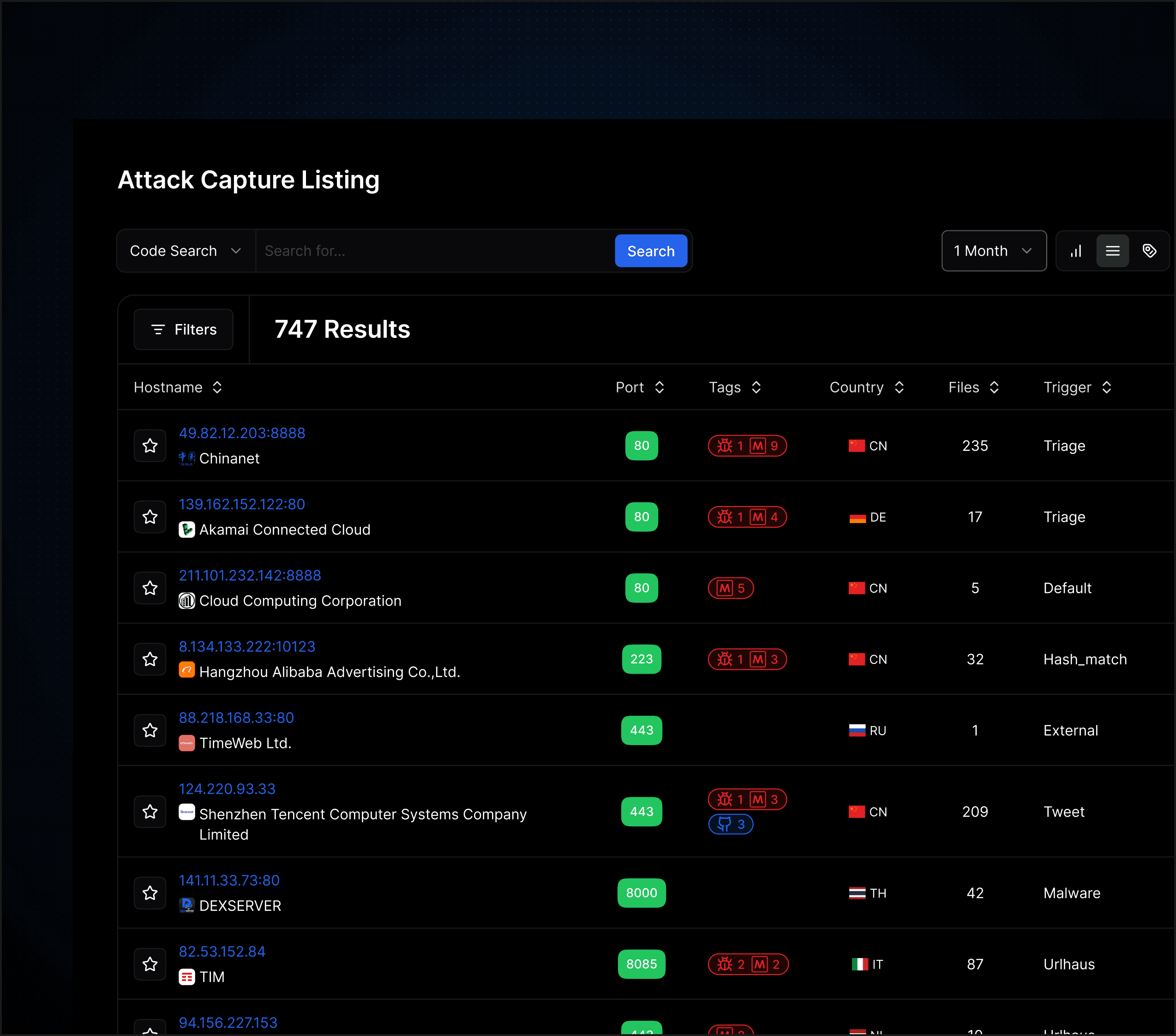
AttackCapture™ enables you to uncover and mitigate potential cyber threats within exposed directories. With this feature, you can detect malicious open directories, secure sandbox malware, download comprehensive file archives, identify exploit kits and reconnaissance tools, discover log files and potential victims, and access downloads of malware and unseen exploits.
faq
What is AttackCapture used for?
AttackCapture is used to investigate exposed attacker directories and analyze the files, tooling, and artifacts left behind on live malicious infrastructure.
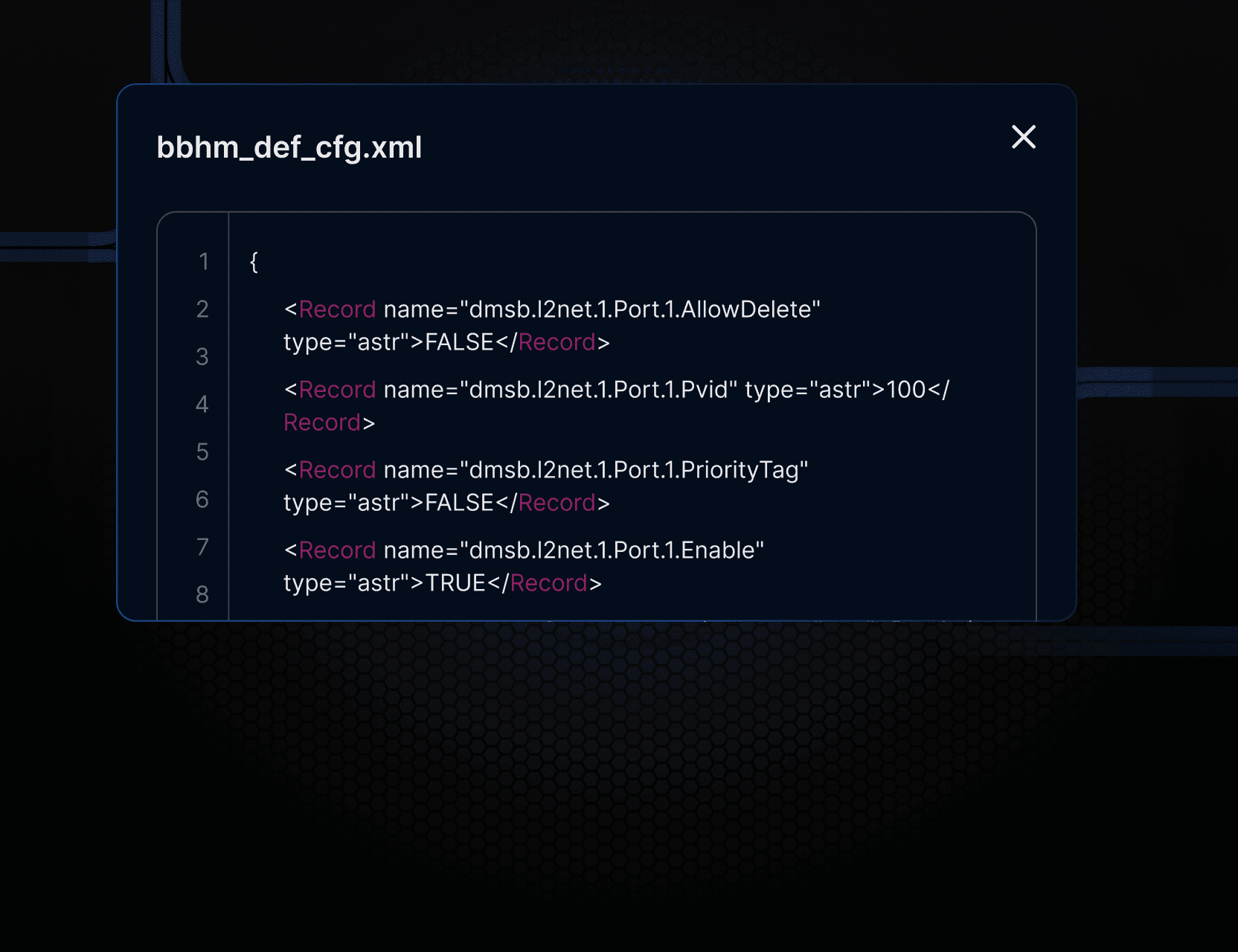
What kind of data does AttackCapture analyze?
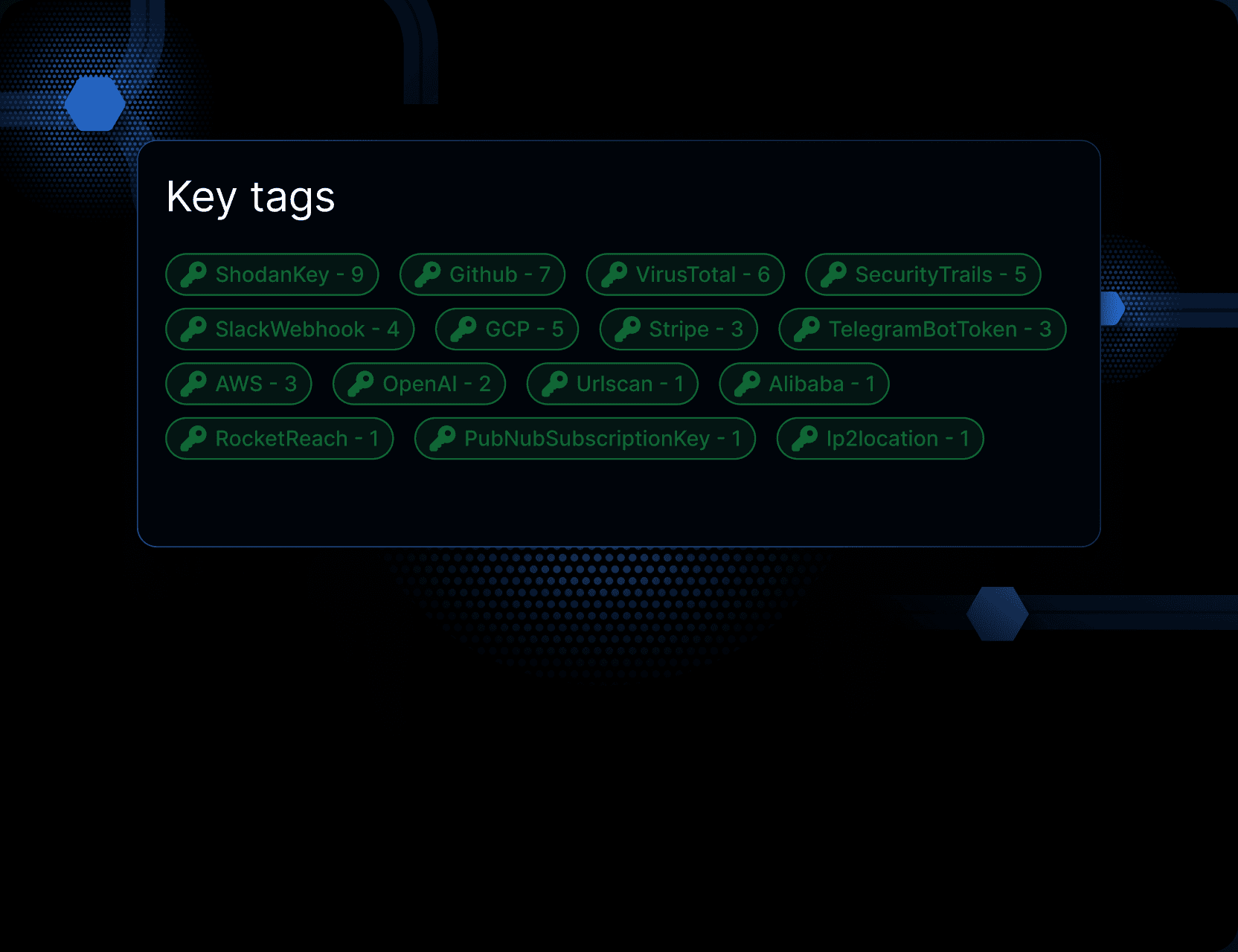
AttackCapture analyzes files found in exposed directories, including malware, scripts, credentials, logs, exploit tooling, and other attacker-related artifacts.
How does AttackCapture help threat investigations?
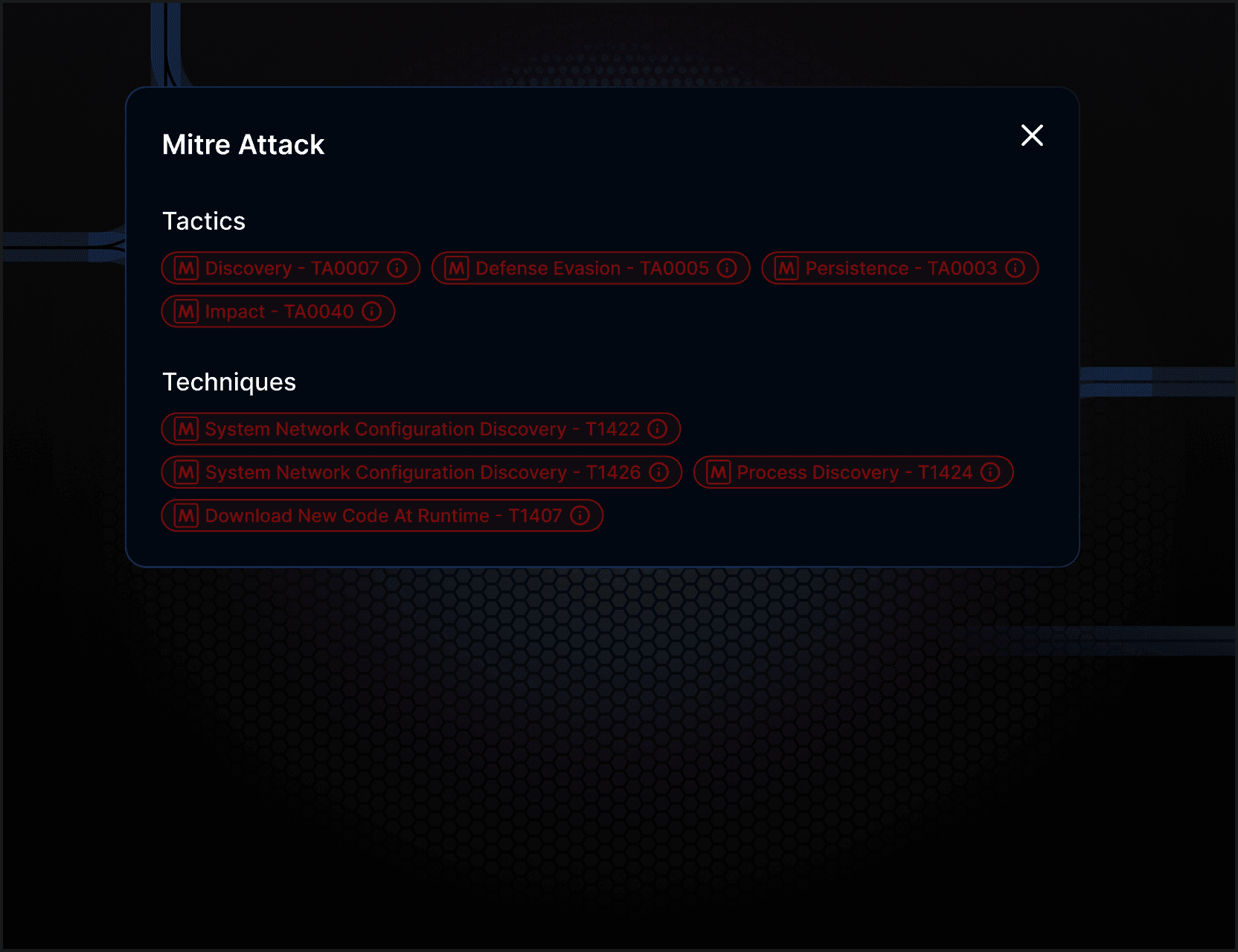
It allows analysts to explore real attacker files, search code and text across archives, correlate credentials, and map activity using MITRE ATT&CK techniques.
What makes AttackCapture different from indicator-based tools?
Instead of focusing only on indicators, AttackCapture provides direct access to attacker-hosted files, enabling deeper investigation into how campaigns actually operate.