Our partner plans are designed around predictable pricing, generous usage, and a roadmap shaped around integration, resale, and real-world use, not investor optics.
We beat Censys quotes by 25%+
Show us a 2025 or later threat intelligence Partner quote and we’ll beat it by 25% or more.
You won’t hit your usage ceiling
We guarantee hitting query and API limits isn’t something you’ll need to think about.
Flexible and friendly terms and conditions
Your agreement will include the features, ongoing support, and terms and conditions that make sense for you.
Easy to join (and leave)
We keep renewal terms straightforward and transparent.
A partner-centric product roadmap
Our roadmap is focused on coverage, data quality, and making it easy to integrate, embed, and resell.
We aren’t competing with you
We don’t want your customers or clients. We don’t want to build your product. We don’t want your scoop. We win when you win.
“
Hunt Intelligence reduced validation time by over 95 percent, enabling us to automate investigation workflows and scale detection without building or maintaining our own validation infrastructure.
“
Product Lead, Threat Detection
Threat Intelligence Platform

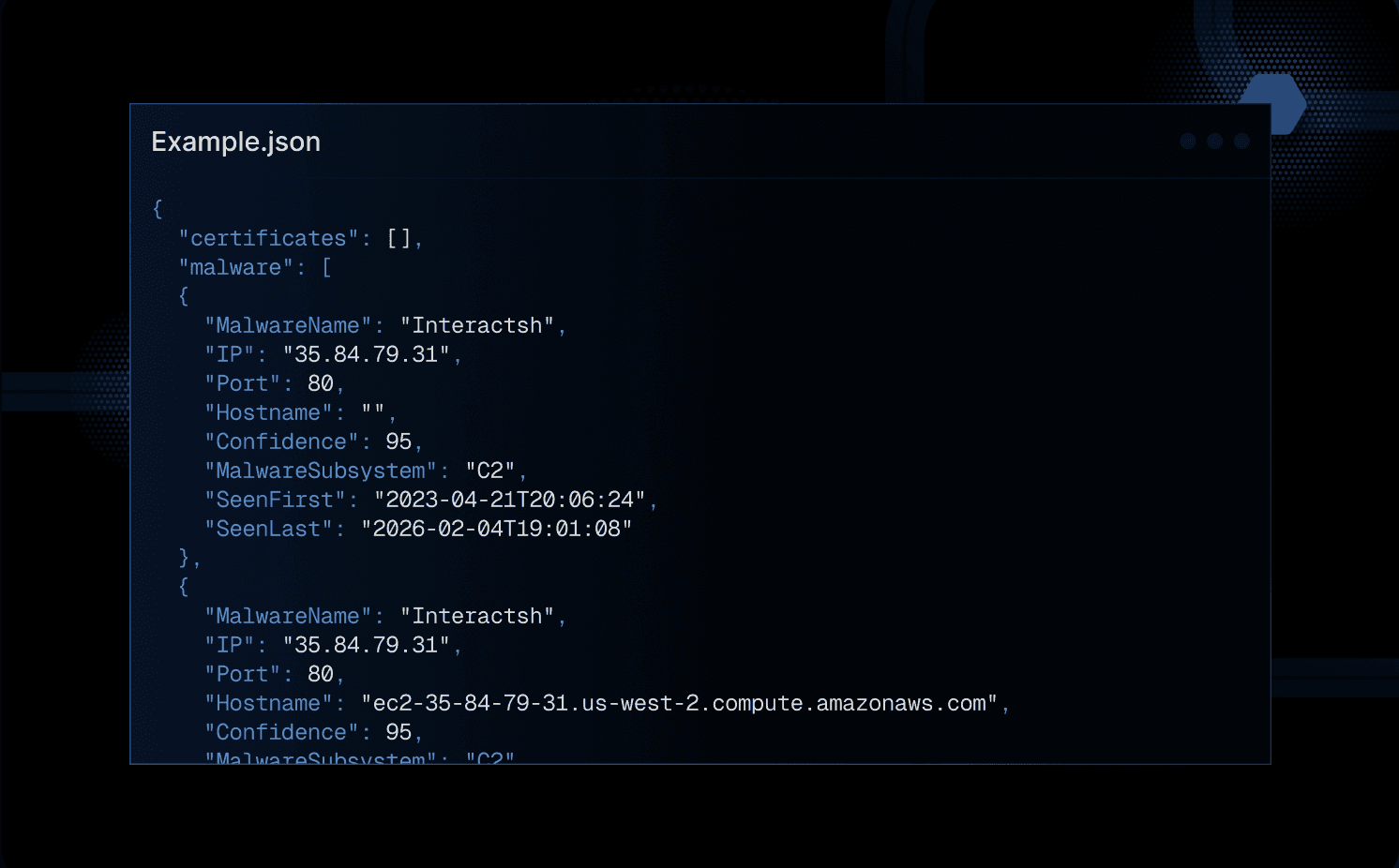
C2 Infrastructure Feed
Replace or augment your C2 detection pipeline with Hunt’s feed using first-party validation and our own scanning to hunt, amplify, and monitor malicious infrastructure
IOC Hunter
Investigate faster, pivot deeper, and block threats with confidence by extracting and enriching IOCs from trusted research.
HuntSQL™
Query Hunt’s database using SQL. Query first-party HTTP data, confirmed C2 servers, first-party certificate data, honeypot data, open directories, and phishing sites.
Phishing Infrastructure
Access an independent collection of heuristic analyses of weaponized, not-yet-weaponized, and benign websites. Pages are measured multiple times to understand an attack’s lifecycle.
AttackCapture ™
Uncover and mitigate potential cyber threats within exposed directories. Identify and automatically surface exploits, file paths, attacker tools, and even GitHub references.
Bulk Enrichment
Extract IPs, domains, and apex domains from any text file in three simple steps. Upload text files, automatically extract IP and domain, get back an enriched CSV
Operational Efficiency
95% less analyst validation for endpoint protection provider
~40% in savings by switching from Censys
70+ workflows automated monthly inside an XDR platform
Detection Coverage
10X increase in threat observables for an MDR provider
29k+ more live IP:Port detections than OSINT feeds
Nearly 3X broader malware family visibility through infrastructure discovery
Proactive Prevention
Targeted APT attack blocked at a global bank
Near real-time block-grade intelligence delivered to customers
Leveraged AttackCapture ™ to identify new threats before it was widely documented in traditional feeds

faq
What kind of data does Hunt.io provide, and how does it differ from search engines?
Hunt.io is infrastructure-first. Search engines index the global internet for content. We scan it for malicious infrastructure, C2 nodes, phishing sites, and exposed attack tooling. The asset data we produce is built around what security professionals actually need for detection, not general discovery. You get structured, enriched data covering ip addresses, dns records, open ports, and ssl certificates, ready to use. No raw noise, no stitching things together yourself.
How do I integrate Hunt.io into a product we're already building?
Everything is API-first, so you're not rebuilding your stack. Most partners keep their existing tools in place and layer Hunt.io on top to use those tools effectively. If you're coordinating across multiple tools or pipelines, we have documentation and a team that will hop on a call to help you integrate cleanly. We also support external attack surface management platforms natively, so there's usually a path regardless of your current architecture.
What capabilities go beyond what Censys ASM covers?
Censys ASM is built around asset discovery and perimeter visibility. Hunt.io comes from the other direction. The capabilities we offer are centered on what attackers are actively operating, not just what you own. C2 tracking, phishing infrastructure analysis, AttackCapture for exposed directories, IOC enrichment. You also get vulnerability scanning context, detailed information on active malware families, and visibility into known vulnerabilities tied to live infrastructure. These are valuable features that passive enumeration tools don't surface.
Does Hunt.io support continuous monitoring of attacker infrastructure?
Yes, and it's not a checkbox. Monitoring here means your feeds are updated continuously based on our own first-party scanning. We're tracking the attack surface of malicious infrastructure in near real-time, not working from stale snapshots. This matters for catching potential vulnerabilities being exploited in active campaigns before they reach your customers. Attack surface management is usually framed as defending your own perimeter. We give you the attacker side of that picture too.
How does Hunt.io help with identifying threats across the entire internet?
We scan internet connected devices and exposed infrastructure at scale. Not just web servers, but the full range of devices connected across the entire internet. Identifying active C2 nodes, phishing infrastructure, and attacker tooling early, before it shows up in an incident report, is exactly what this data is built for. You don't need to build your own scanning pipeline to get that signal.
What does Hunt.io cover when analyzing external assets and attacker reconnaissance?
Analyzing external assets is where a lot of threat intelligence platforms fall short. They cover what you own. We cover what's threatening you from outside. That includes infrastructure that attackers discover using search tools like Shodan to find exposed targets, plus misconfigured services, rogue certificates, and leaked tooling. If vulnerability management is on your product roadmap, we give you signals that go well beyond CVE lists.
What kind of servers does Hunt.io track, and how deep does the coverage go?
We track C2 servers, phishing servers, and anything else we can validate as actively malicious or suspicious through our own first-party scanning. Not passive indexing. For each confirmed host, we're collecting service banners, certificate chains, malware family associations, and directory exposures. The depth varies depending on how the infrastructure behaves, but if a server is doing something bad, we're usually on it before it shows up anywhere else.
How does Hunt.io help security teams stay ahead of threats?
Most detection tools are reactive. You're chasing alerts or reviewing logs after the fact. The way Hunt.io approaches threats is different. We do continuous first-party scanning, so the intelligence is fresh and tied to real infrastructure activity. Partners use us to block things proactively, not just document them after. We've seen APT infrastructure blocked at large organizations before it became a public incident, because the detection came from Hunt data before it showed up in traditional feeds.
What does the onboarding process look like, and how fast can we run an initial analysis?
Faster than you'd expect. Most partners get to a working integration with enough analysis to evaluate data quality within days, not weeks. We provide documentation, API keys, and direct access to our team. If you want to run an analysis on your current detections against our C2 feed or IOC Hunter, we can set that up during a demo. No lengthy procurement process required to start