Hunt turns unstructured text into enriched IP and domain data you can use immediately in investigations.
Pivot and Expansion
Bootstrap investigations by using research from other teams to narrow in on an incident or threat actor by expanding using their TTPs or ensuring that you don’t hit a dead end.
faq
What is Bulk Enrichment used for?
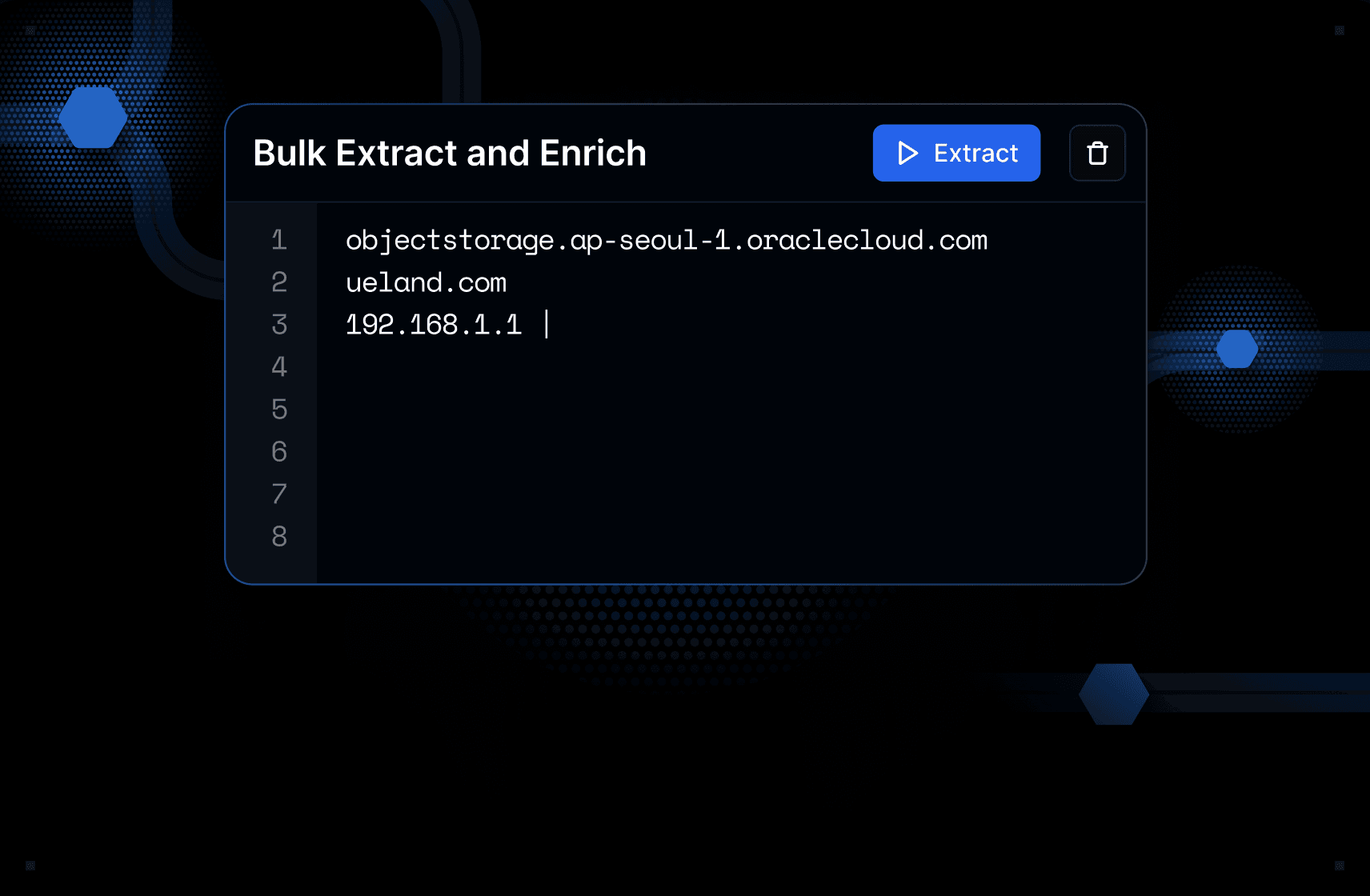
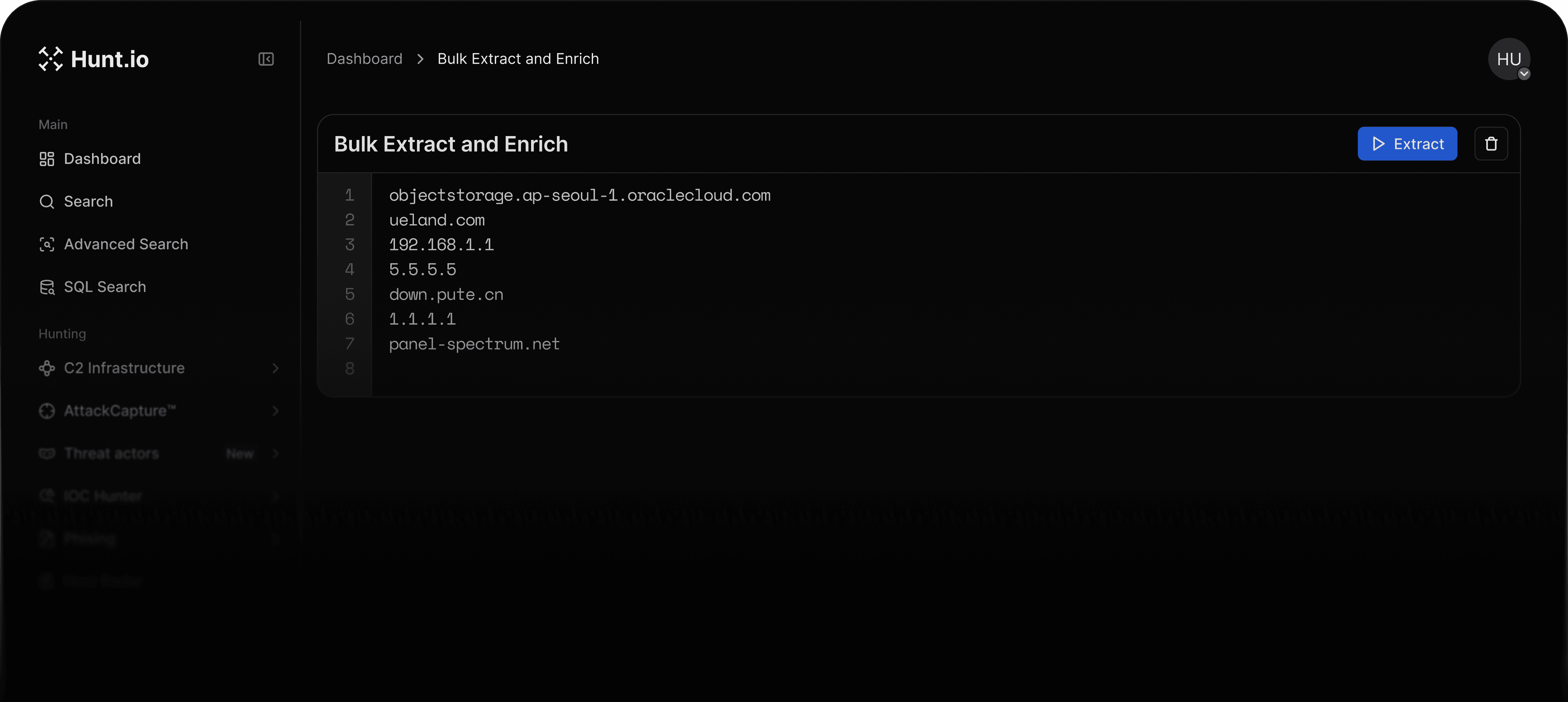
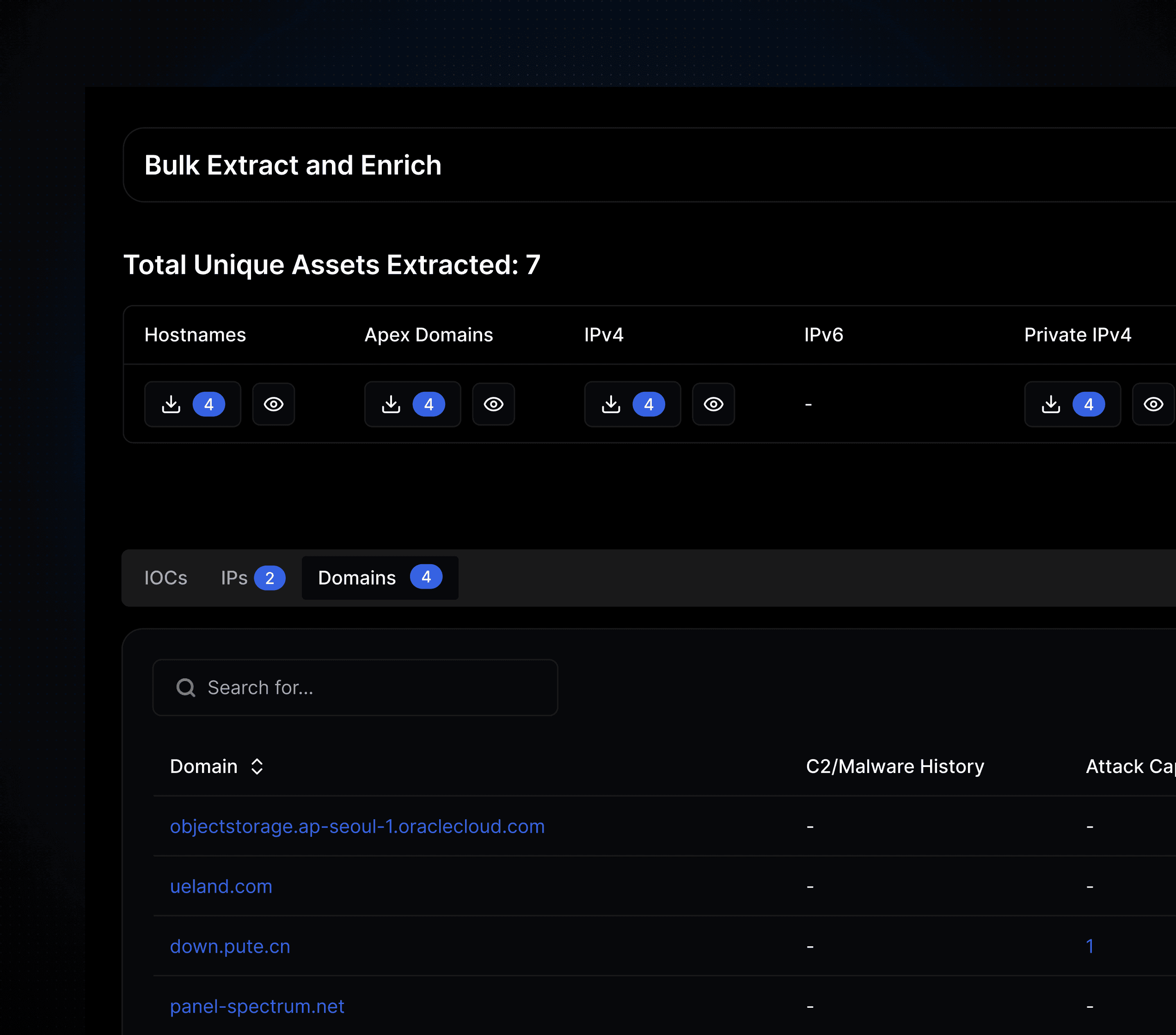
Bulk Enrichment is used to process large amounts of unstructured text and extract IP addresses and domains for enrichment and investigation.
What kind of input can I upload?
You can upload text files or paste raw text containing indicators such as IP addresses and domains for automatic extraction and enrichment.
What does the enrichment output look like?
The enrichment results are returned as a downloadable CSV file containing enriched data for the extracted IPs and domains.
How does Bulk Enrichment help investigations?
It helps teams quickly pivot from raw research or shared intelligence into enriched indicators, making it easier to expand investigations and avoid dead ends.